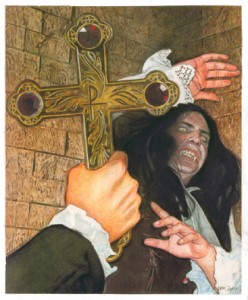
 I have hesitated a while before choosing the right image to illustrate this article. I read again a press-release about a new log-management product which pretends to provide “out-of-the-box security and compliance for business of all sizes“. Dear v€ndor, are you living in a care bears world or are you possessed?
I have hesitated a while before choosing the right image to illustrate this article. I read again a press-release about a new log-management product which pretends to provide “out-of-the-box security and compliance for business of all sizes“. Dear v€ndor, are you living in a care bears world or are you possessed?
Yes, your solution has maybe nice reports ready to be produced just by clicking a “Generate now” button. You allow searching across millions of events in seconds? Why not… But the power and reliability of a log management solution directly depend on how you feed it with events! Lack of events will produce poorly reports… then poor ROI!
Before deploying your top-notch log management solution, there are so many issues that could occur:
- Unreachable devices – They could be located on remote sites with limited bandwidth. Some firewalls might prevent monitoring protocols (which are often and hopefully blocked). Are they using private IP addresses with NAT rules?
- Supported format – Your devices might generate events in a unsupported format.
- Performance impacts on the network flows
- (De)commissioning of (old)devices
- Overlapping in IP subnets
- Procedures / follow-up
- …
Still today, most log management solutions are deployed urgently to face a need of compliance. For me, v€ndor$ pretending to provide “out-of-the-box” log management services could be blamed of “false advertising“! Implementing a log management solution is not a road without pitfalls. It could quickly drive you to hell…
Xavier, thank you for this post!
We see too much quick sales based on urgent compliance needs and vendors know this too well. For them it’s not a case of creating the best-in-breed product but the product that fits in the latest and greatest compliance challenge companies meet. Compliance hampers security in the enterprise just as much as it hinders progress at the vendor site.
At the moment … I don’t see a lot of solutions 🙁