Tor aka “The Onion Router” is a well known network running on top of the regular Internet. It protects the confidentiality of communications between users and regular online services. As the multiple layers of an onion, Tor is a worldwide decentralized network based on layers. When you need to connect to a remote site, your packets enter the Tor network and are routed to the final destination across several nodes which just relay the traffic anonymously. As explained on the website:
Tor aka “The Onion Router” is a well known network running on top of the regular Internet. It protects the confidentiality of communications between users and regular online services. As the multiple layers of an onion, Tor is a worldwide decentralized network based on layers. When you need to connect to a remote site, your packets enter the Tor network and are routed to the final destination across several nodes which just relay the traffic anonymously. As explained on the website:
“Tor is free software and an open network that helps you defend against a form of network surveillance that threatens personal freedom and privacy, confidential business activities and relationships, and state security known as traffic analysis.“
From an authority point of view (your boss, your country or who cares), there are several ways to implement blacklists. Examples:
- Using DNS redirection
- Using IP addresses blacklists
- Using Deep Packet Inspection
The first technique consists in redirecting hostnames to a new IP addresses via DNS. This method was already used once in Belgium in 2009 to prevent Belgian citizens to access a controversial website. This is completely irrelevant as websites are still available using their IP address(es) and people using open DNS resolvers like Google or OpenDNS will still be able to access the blacklisted resources. Or,if you are part of a international organization, they are chances that you use global resources localized in a foreign country.
The next technique, blacklists based on IP addresses, is also useless. This was proven during the “Wikileaks story”. The website was replicated on multiple locations. Those techniques are more a “cat & mouse” game between the prohibited resources owner and the authorities.
Finally, the DPI or “Deep Packet Inspection” perform filtering at another level. Instead of using the packet headers (where are located information like source and destination IP addresses and ports), DPI analyzes the payload of packets to detect prohibited content or applications (read: at layer 7 of the OSI model). You could, by example, prevent packets containing words like “pedo“, “twitter“, “revolution” or “Tibet” (Dear Chinese authorities, if you read this, a big hello from Belgium! ;-)) . Deep Packet Inspection becomes common in organizations to protect them against data loss or data leakage or to prevent users to waste their time/Internet connectivity. But it remains extremely difficult to implement and maintain at the ISP level for reasons of performance!
Even if you use Tor, access to some resources might be prohibited if the output node is connected to an ISP which implemented such controls. That’s why Tor developers implemented the “Hidden Services“! Once you joined the Tor network (as a client or a relay), you can offer such services (a web site, a SSH gateway or SMTP relay) which remain in Tor. Once your packets entered the network, they won’t go out. Basically, you will configure some kind of reverse proxy. In your torrc file, add some configuration lines like the example below:
### This section is just for location-hidden services ### HiddenServiceDir /home/tor/hidden_service/ HiddenServicePort 80 127.0.0.1:8080
Restart your Tor and two files will be created in the directory defined above: a private key (keep it safe!) and a “hostname” file which contains your assigned URL. Something like: r1sgytddkyjudx7.onion. This is your “public” hostname (but restricted to the Tor network) that you can communicate to your contacts. More information is available here.
This is a very convenient way to publish online services or data without being blocked by regular controls. Of course, Tor Hidden Services can also be used for malicious activities or to share prohibited contain. But it is another debate!
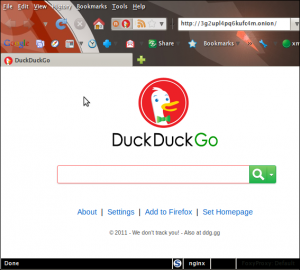
If you are looking for hidden services on the Tor network, there is even a search engine called “Duck Duck Go“. Available at the following address: http://3g2upl4pq6kufc4m.onion/: