 Here we go with a review of the last day. As usual, the social event had huge impacts on some attendees but after coffee everything was almost back to normal. The day started with Braden Thomas who presented “Reverse engineering MSP 430 device†or reverse engineering a real-estate lock box.
Here we go with a review of the last day. As usual, the social event had huge impacts on some attendees but after coffee everything was almost back to normal. The day started with Braden Thomas who presented “Reverse engineering MSP 430 device†or reverse engineering a real-estate lock box.
In US/Canada, such devices are used by real-estate agencies to store the keys of homes for sale. They allow to access the key when the owner is not present. Why focus on such devices? First, because they are used by many people and, usually, they tend to store crypto secrets into the flash. It’s cheap and easy but not necessarily nice. There is a legacy key using cell radio but more and more users use the eKey (an IOS/Android app). Braden explained with many details all the steps he performed to be able to access the firmware and then to extract the crypto key. Guess what? The presentation ended with a live demo: Braden just successfully unlock a lock. During the presentation, he explained the different attacks that are available and a special one (that was successful) called “Paparazzi” attack: the goal is to use the flash from a camera against a decap chip to make it behave differently.
Then, Peter Hlavaty talked about “Attack on the coreâ€. This talk went in the same direction as the one presented yesterday about bypassing security controls in Windows 8.1. On most operating systems, the kernel is the nice place to place malicious code. Why? Because modern o operating systems are more and more protected by implementing multiple controls. The talk focused on CLP3 to CPL0 (“Current Privilege Levelâ€). Level 3 being the user mode and level 0 the kernel mode. Peter not only focussed on Windows but also on Linux and Android. That’s clear: the kernel is the new target!
After a welcomed coffee break, Jean-Philippe Aumasson, renowned cryptographer, talked about… cryptography with a talk called “Cryptographic backdooringâ€. Usually, cryptography means a lot of formulas, etc but Jean-Philippe’s talk was very didactic! Why speak about backdoors? Because they are present in many crypto implementation and there is no official research paper on this topic. A backdoor can be used for surveillance, deception, … and also terrorists! There are also more and more backdoors in products and applications today.
Jean-Philippe explained what is a backdoor. His definition is:
A feature or defect that allows surreptitious access to data
Based on weakened a algorithms or covert channels. But what is a good backdoor? It must be:
- Undetectable
- Principle of “NOBUS” (No One But Us, NSA term)
- Reusable and unmodifiable
- Simple
Then, he reviewed examples of backdoor and how they have been implemented. A very nice talk!
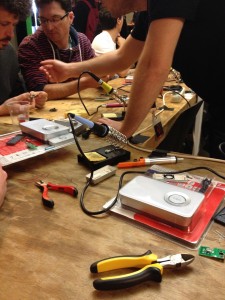
There was no lunch break for me because I attended a workshop about RF hardware: “Fun with RF remotes†prepared by Damien Cauquil. The goal of the workshop was to build a … RF door bell brute forcer. After an introduction to the RF technology and some demos to capture and analyse signals, it was a hands-on session. All participants received a door bell pack (a remote controller + door bell). The challenge was to hack the remote and make Damien’s doorbell rings. It was a premiere for me. After soldering some components and some stress, it worked! Very nice workshop!
And the last half-day started with Guillaume Valadon and Nicolas Vivet who presented “Detecting BGP hijacks in 2014â€. I arrived a bit late due to the hardware workshop. The first part was a recap about BGP, how it works, what are the features, etc. BGP hijacks are not new but they can have a dramatic effect! An hijack is a conflicting BGP announcement. It means that your packets are sent across not authorised networks (from a BGP point of view). The next part of the talk focussed on detected the hijacks. This is a critical step for ISP’s. Guillaume and Nicolas explained in details the platform deployed worldwide to collect BGP messages and store them, then they are processed by OCAml. They can emulate a BGP router via some Python code. By putting all the components together, they are able to analyse the BGP announces and detect issues. But this is offline and consumes a lot of data. They also presented a real-time detection mechanism. A nice presentation with many details. I recommend to read the slides if you’re working with BGP. Their conclusions are that such attacks are a real risk and that traffic must be encrypted and authenticated to prevent it to be read by 3rd parties.
Alex Ionescu came with a “surprise talkâ€. The title was “Unreal mode: Breaking the protected processâ€. It was a surprised talk because he received a last minute green light from Microsoft. Windows Vista introduced new protections at kernel level. In Windows 8.1, that model was extended to protect key processes even from admin and to mitigate attacks like pass-the-hash. Alex explained how digital signatues are working with the new versions of the OS. He also explained how process protection works (even with admin rights some processes can’t be killed or accessed by debuggers. A mass of interesting information if you’re working with Windows security models.
And to close the conference, a keynote was presented by Anthony Zboralski: “No Such Securityâ€. Anthony defines himself as “a bank robberâ€. When he was young he played with many computers and quickly started to break stuff. After some issues with the Justice, he switched to security consultancy. His keynote was a suite of reflexion about the security that is implemented today by companies but also recommended by consultancy companies.
The second edition of NoSuchCon is over! It is a great event with highly technical and nice presentation. I also met lot of new or old friends. The talks have already been published here:Â http://www.nosuchcon.org/talks/2014/.




RT @xme: [/dev/random] #NoSuchCon Wrap-Up Day #3 http://t.co/ZcjKubSJs5