 Yesterday, I went to bed very late after writing some documentation. Everythink looked quite on the Intertubes. A last check on my Twitter timeline and I felt quickly asleep. This morning, I woke up and started my daily ritual… Coffee, mail, RSS feeds, Coffee, Twitter timeline… Wooow! Did I miss something? The night was eventful! We were flooded by information about attacks against (amongst many others): the NY Times, Twitter UK, the Hufington Post. They are plenty of blog posts, articles and notifications online (example on the SANS ISCÂ website). What do they have in common? They use the same registrar to manage their domain names:Â Melbourne IT. And this one was the target of the Syrian Electronic Army.
Yesterday, I went to bed very late after writing some documentation. Everythink looked quite on the Intertubes. A last check on my Twitter timeline and I felt quickly asleep. This morning, I woke up and started my daily ritual… Coffee, mail, RSS feeds, Coffee, Twitter timeline… Wooow! Did I miss something? The night was eventful! We were flooded by information about attacks against (amongst many others): the NY Times, Twitter UK, the Hufington Post. They are plenty of blog posts, articles and notifications online (example on the SANS ISCÂ website). What do they have in common? They use the same registrar to manage their domain names:Â Melbourne IT. And this one was the target of the Syrian Electronic Army.
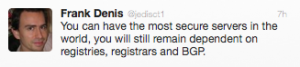
Usually, I don’t blog in the morning but a quote from @jedisct1 forced me to write down some comments:
This quote resumes everything: You can operate a very strong bullet-proof infrastructure (which does not exists at all!), you can spend huge amounts of money to buy extra security layers like multiple firewalls, reverse-proxies, IDS, WAF, load-balancers, operate a SOC or <insert-your-favorite-tool-here>. You will have to rely on common technologies which make the Internet work. Classic examples are DNS and routing protocols like BGP! They remain again and again the weakest links of your security chain. Bad guys won’t spent to much time against you directly (time is a precious resource). They will find another way like DNS hijacking. This was the case last night, Melbourne IT was pwn3d and the DNS servers of multiple big websites changed to other IP addresses. Think about this!
So, let’s grab another coffee and follow the next steps of this story…
@xme http://t.co/McYV0EBdNM “the weakest link” is one of the attacker principle. There are some variants on attacker principles (page 4).
RT @xme: [/dev/random] “The Weakest Link” is Back! http://t.co/B9MBKuJbPb
RT @xme: [/dev/random] “The Weakest Link” is Back! http://t.co/B9MBKuJbPb