
During the pre-2000 years, hackers were mostly explorers (non goal/profit oriented). There was a low trade volume, but  it changed with the first boom of the dot-com companies.. The Internet was a nearly complete legal vacuum. The “law of the strongest” was applicable. In 2001, teens controlled huge DDoS networks. It was the time of 0-days “Internet-ending” and a significant percentage of Internet was pwned by amateurs.  This pre-2000 Internet is similar to 1500’s in Spain. Durng the 1600’s: there was wars between multiple countries:  Spain VS France VS Britain VS Holland and small-scale pirates switched into large-scale organisations. In 2001-2013: Internet faced rapid economic & societal changes trough the adoption of network. It was the rise of privateering: Governments realised the importance of Internet. The hackers community split into interesting fragments: Surveillance / monitoring. What are the different types of actors?
- Navy: full-government employment
- Privateers: hackers working as private org
- Mercenaries: hackers working to protect new trade routes
What about the future according to Halvar? Any document opened can lead to an open door for an attacker. That’s why sandboxing will be more and more used. But what’s next? He predicts a transitive trust is the silent killer (example: stealing signing keys from well-known vendors). Another question: Why exploit if I can update? Interesting keynote, I liked the comparison with the previous centuries.
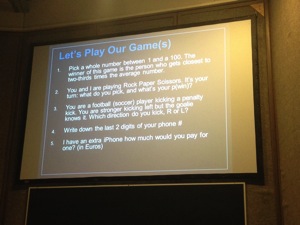
After the keynote, regular presentation started, the first one was performed by Allison Miller from Electronic Arts. Her topic was “Games We Play: Payoffs & Chaos Monkeys” or a game theory. Games are a big business today, there are millions of players on the Interent. Previously, games were distributed via resellers but today, the business model changed and companies developing games also sell them directly to the end-users and sell extra stuff. This means that have to implement fraud detection control like any financial companies. Electronic Arts implemented such a system. The main goal is to estimate the type of controls we need to deploy. That’s the job of Allison. Game theory can apply to real-life games like rock-paper-scissors or simply choosing left or right. It’s a branch of applied mathematics and it provides a framework to study decisions made by players. It is used in economy, military, negotiation, business etc. Allison reviewed some mechanics (payoff matrix, decision trees, etc) and explained how to implement them based on formulas.
To implement this, we have to:
- Identify players
- Clarify the rules
- Define a strategy (show me your moves)
- Describe Payoffs
- Single move or repeated game
After her slides about theory, Allison switched to the real world. What’s important: the rationality of actors and payoffs value. She gave a first example with the 2/3 game. For rock-paper-scissors, the best strategy to maximise chances to win is randomisation. Same for a penalty kick but if the kicker is better on left and the goal know that, it changes the strategy. Attackers and defenders can be compared to them. Finally, Allison explained that the game theory is used by risk management. Risk management is decision management. The talk was interesting but without real implementation example. I discussed with Allison during the speakers dinner and she gave me more details.
After a coffee break, the next talk was presented by myself. It was the same talk as the one of Hashdays last year. It went smoothly and I had interesting conversations with attendees during the day.
Then followed David Rook with the talks he performed in BSidesLondon last month. I missed it the first time so I was happy to be present today. David works for Realex and is busy with application security. He explained how he developed a strong security policy based on a strict SDLC (“Software Development Life Cycle“). It’s not easy to change the habits of developers. It took times and a lot of efforts. David explained this like a story with very nice slides.
The very first step was to review the legacy code: “SDLC? What SDLC?!” A first SDLC can be very simple (Use the “KISS” principle – Keep It Simple and Stupid): It was a Visio drawing with 4 squares. Then came, the first automation phase: security testing using BurpSuite. Then, threat modelling was implemented (based on the Microsoft approach but modified to best suit the needs). Then hired an external auditor to improve the SDLC: From 30 pages of improvements in 2008, they reached 2 pages in 2011! It’s important to share the knowledge: Talk to conferences, write blogs. They also switched from one big development department to small teams more focused on products. Each team does everything with strong focus on their applications. Then came the automation phase 2. The goal was to make security review easy and repeatable. The software Agnitio replaced old Word documents and Excel sheets. Can two companies use the same processes and SDLC? According to David, yes! With a strong SDLS, resource planning becomes more easy and  teams can grow. It’s also more easy to estimate and get the resources (read: better budget control). Based on his experience, David reported the three main categories of errors in code:
- Input validation
- Output encoding,
- Error handling
What’s the focus today? Mobile applications! Don’t forget them and implement the same controls. Very good presentation, this is a must-read for all developers or project managers.
After the lunch, Brian Honan spoke about “Learning from history“. The talks started with an introduction to his baby: the Irish CERT. It started in 2004 when there was no real structure in place. In 2008, IRISS was born but still without a strong structure (based on volunteers, no dedicated infrastructure, etc). Then Brian make a comparison of security defences with a classic Irish defense model: layers, perimeter defence, small ingress, egress doors. I like the following comparison:
“Security is like an egg: It will resist to press it on top and bottom but will break if you press it on the sides!”

IRISS participated to the Verizon DBIR and Brian mentioned interesting statistics from this report:
- 69% of data breaches were detected by 3rd parties
- 62% months or more
- 78% not complicated
- 74% due to phishing
Still today, most attacks use a classic scenario: phishing > rogue website > malicious code > pwned.
The organised crime is growing and DDoS, extrusion are common. What are the root causes?
- Poor passwords
- Patches
- Vulnerabilities in web platforms
- Out-of-date AV signatures
- Lack of monitoring
How to improve the situation?
- Learn and understand your business! Read the business plan.
- Don’t forget the basics.
- Strong passwords (use two factors authentication?)
- Monitor your logs
- Harden systems
- Use security tools
- Segment your information
- Analyse network patterns
- Train staff & partners
- Use open source data (pastebin, google alerts, shield, Arakis (?)
- Set traps (but properly!)
- Share with peers (veriscommunity.net/doku.php)
Another Brian’s quote:
“Data breach is like toothpaste! Once it’s out, it’s difficult to get it back in!”
Great talk, great speaker, what else?
The next talk was presented by Davi Ottenheimer about “Big data security: Emerging threats and how to predict them“. Big data? Everything has been said about bid data! Davi explained that big data can be compared to a wave. You can’t look at only a piece of it. Open your scope wider and wider.

After some example about big-data, he mentioned interesting example where the amount of data that we could grab from somebody could be re-used to improve online services or authentication. The first example was about the music online service Pandora’s box. Today, songs are selected based on the gender, the tones, sales, etc. But more interaction could be added to select right songs with the help of the weather and more precisely who you are and what you do. Example? Chose appropriate songs while jogging. The same could apply to authentication. Today we tend to implement 2-factors authentication. Why not switch to a n-factors authentication? Using factors coming from multiple personal devices like mp3 players, watches, etc). Davi called this “the modern spice of life“.
Then, Simon Roses Fermeling presented his talk “Dude, where’s my laptop?“. I already saw this presentation during BlackHat Europe. He changed some slides but my wrap-up is already online here. A great research! Just keep in mind: do NOT trust anti-theft applications!

To close the first day, Christien Rioux working for Veracode but also the organiser of SOURCE, spoke about static binary analysis. This is normally a talk of two hours. It was compressed to 40 mins and was quite… intensive! :-) They are two ways to perform binary analysis:
- Static (by reversing the code and understanding it)
- Dynamic (by executing the code – in a sandbox as example)
RT @xme: [/dev/random] SOURCE Dublin Wrap-Up Day #1 http://t.co/NgjdnNqzPE #srcdub
RT @xme: [/dev/random] SOURCE Dublin Wrap-Up Day #1 http://t.co/NgjdnNqzPE #srcdub