
Yesterday evening, I went with friends to a traditional Swiss restaurant then we passed by the party to have a few drinks. Thanks to the sponsor for the open bar! That’s why it was difficult to wake up this morning… But, anyway, I had a wrap-up to write for you! This is a good opportunity to thank all my readers and followers. It’s always a pleasure to meet new people in conferences and hear: “Oh, you’re that guy who writes the wrap-ups! Nice to meet you!“. So, here is one for the second day of Hashdays 2012! This time, it will be shorter because I attended a workshop in the morning and talked in the afternoon.
My first choice was Jonathan Sinclair who also participated to the management session last Wednesday. Like Alexander yesterday, I was interested to see the “technical” version of his presentation: “Hypervisors and Virtual Machines – State of the Art“. It was an overview of the attacks that existed (and remain!) and currently exists in this field. First point: they are more and more hypervisors in the virtualisation landscape, so Jonathan had to focus on a specific one. He first gave some facts about the history of cloud and virtualisation. I liked a funny mention: All started in 1963 with a memo called “Memorandum for: Members and Affiliates of the Intergalactic Computer Network” (by J.C.R Libcklider). This looked extracted from Star-Trek! After all, for the oldest amongst is, isn’t just time-sharing computing? Remember BBS’s where everything was shared! You can of course exploit a lot of stuff in the cloud (Facebook, Twitter, iCloud, etc) but it’s not what Jonathan finds the most funny. He prefers to focus on “IaaS” (“Infrastructure as a Service“). Why? You have a much large attack surface and it brings most control. Once compromised you have the complete control of the infrastructure.
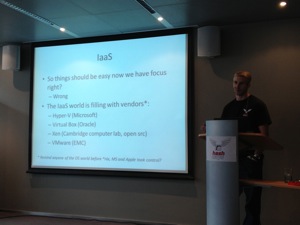
What are the constraints? You have the “bare-metal” hardware: Hypervisors run directly on the hardware or on top of a regular OS. It looks interesting to go to bare-metal systems because the technology is still immature regarding security and the landscape is still heterogeneous. According to Jonathan, VMware was a very good target for his researches. Why? Leadership and bare-metal installations. After this introduction, Jonathan spoke about VM penetration testing.What are you looking for? The reconnaissance phase is looking for 443, 902, 903, 8000 management ports (good candidates). Shodan and Google are your best friends ever. How to identify the hypervisor? There are tools and techniques to accomplish this: On Linux: imvirt or girt-what and on Windows: Elias Bachaalany has made interesting researches. Another interesting tip: VMware Backdoor is never fully disabled and may reveal very interesting information. Â Other interesting tools are:
- Blue Pill. VMChat is a tool demonstrated by Ed Skoudis and Tom Liston in 2006(!).
- Cloudburst
- Metasploit has modules to exploit VMware:
- vmware_guest_stealer
- vmware_session_rider
- xlen_login
- vmware_auto_pwner
- …
The “pass the hash” attack method was also briefly reviewed. “Crisis” (or “Morcut”) is a root kit that as the ability to adaptively weaponise for multiple targets included VM’s. And what about VMDK? They left the building already… 😉 Data extrusion is possible via the VM configuration file. (vmdk errwk). Appraisal:
- The “cloud” hypervisor world is upon us
- User demand for convenient tools at a lower cost. They are speeding the choice of virtualisation
- VMware Backdoor access isn’t secured
- VMDK exploitations are now gaining more attention
- vSphere SOAP calls are insecure
- vMotion transfers the memory image in clear text (wow!)
Virtualization is amazing for attackers, no need to break datacenters fences to reach the servers, do this from your sofa. VMotion network transmits the memory image in clear text #hashdays Who use an OoB network for this? To conclude, Jonathan gave a few words about his current project call “Parasite”. This is a project to abuse a virtualised environment. The objectives are: demonstrate capabilities of threats. Force automatic migration by triggering vMotion, sniff the network and perform reconnaissance analysis.
I skipped the other talks before noon and attended my first Arduino workshop (prepared by Jan Monsh). The Hashdays conference is reputed for their badges. This year again, it was amazing: Based on an Arduino board. Finally, I had the opportunity to play with this awesome piece of hardware!
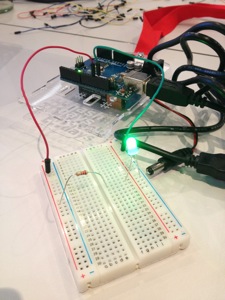
After an introduction to the hardware and software used to compile and upload the programs, we played with some components. It was basic but for me, without a huge background in electronic, it was rewarding: we make LEDs blick, played with potentiometer and display counters on 7-digits display. I’m now the proud owner of an Arduino kit with some sensors, now I need some time to play.
After the lunch, I followed the Ben April‘s talk about NFC (“Near Field Communication“): “I don’t think it means what you think it means“. People don’t have a lot of background about NFC today. It is ant close-range wireless communication, also known as ISO-18092:2004 aka NFCIP-1 with the exchange of NDEF records. Ben reviewed the different types of card (they are four) and the different layers defined in the ISO model. Some useful applications: configure your Wifi, remind to call your girl friend or to buy some milk! Exchange of vCard or course or MIME objects. Non standard uses are: set alarm, change ring or brightness (on phones). All those applications are using NDEF messages which contain NDEF (“NFC Data Exchange Format“) records. What about encryption on NFC tags? They are solutions but nothing very strong at the moment. We are starting to see NFC enabled advertisements (in airport by example) asking you to place your phone close to the poster. Good idea? Ben explained some experimentations he performed on hotel room cards. He has a nice NFC hacking toolbox:
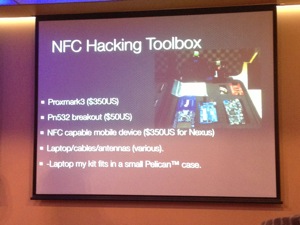
What can you do with this kit? Read/write tags, break MFIRE crypto, sniff NFC exchanges, emulate devices and tags. By default a phone which will read a tag will use it without notification (open an URL). There exists apps to first display the tag content. ndefeditor.com is a nice website which allows you to create/modifit NFC tags. Then Ben explained how he cloned hotel room keys. His conclusion: be very careful with NFC and most important tip: use a reader before scanning a NFC tag!
Then it was my turn to present my talk about the correlation of data across security devices: “Unity Makes Strength“. The goal is to create a toolbox which will inject data into security devices like firewalls and make their configuration dynamic and more reactive to attacks. My slides are online here.
Just after my presentation, I had to leave quickly to catch my flight back to Belgium. Unfortunately, I missed Iftach Ian’s presentation and was not able to say good-bye all the people I met. I just landed in Belgium and finishing this blog post. Thank you to the Hashdays crew for the hard work to set-up this nice event (not all of them are present on the picture) and for the opportunity to be a speaker.

Hi Xavier,
Welcome in the Arduino world! I’m preparing a demo for next month with a Teensy ++. Real usb mouse with usb hub + tennsy board embedded. As soon as you connect the mouse, it creates a powershell set of commands to create a reverse tcp connection to metasploit. It works like a charm… and it’s fully transparent 😉
See u
G
RT @xme: [/dev/random] Hashdays Wrap-Up Day #2 http://t.co/iQglnAxP #hashdays
RT @xme: [/dev/random] Hashdays Wrap-Up Day #2 http://t.co/iQglnAxP #hashdays