 “E-mail”… What a wonderful online service! When I first connected to the Internet around 1994 (I’m feeling old writing this!), I was so exited to receive my first e-mail! Today, I’m very happy when I received less than 50 e-mails per day! E-mail has been, for years, associated with spam. Still today, most of the SMTP traffic on the Internet is spam. Fighting spam became a real sport for most of us.
“E-mail”… What a wonderful online service! When I first connected to the Internet around 1994 (I’m feeling old writing this!), I was so exited to receive my first e-mail! Today, I’m very happy when I received less than 50 e-mails per day! E-mail has been, for years, associated with spam. Still today, most of the SMTP traffic on the Internet is spam. Fighting spam became a real sport for most of us.
Today, most spam can be easily detected and blocked by filters. Being my own e-mail provider (I maintain my own domains, DNS & SMTP servers), regular spam is not an issue for a while. Each week, maximum two to three spams are not detected… I find this acceptable. Today, I’m most concerned by my privacy and how my personal information are managed by third parties.
How do I take care of this issue?
- With my Gmail account, I’m using “email+source@domain.com” e-mail addresses. This helps the creation of filters based on the “+strings” you used. Helas, more and more online services do not allow a plus sign in e-mail addresses.
- Using my own infrastructure, I’m using e-mail addresses like “source@nospam.rootshell.be“.
The goal of those techniques is tracking who leaked or shared your e-mail addresses without your authorization. For a few months, a new project has been initiated by a friend, Tomasz Miklas. His project is called honeymail.net. The principle looks the same as my own solution but it does not require any infrastructure on your side and no registration at all. How does it work?
- You visit a website which requires your e-mail address in a form.
- Create a new alias and activate it. It’s easy as sending an e-mail:
From: xavier@private-email.com To: create@my.honeymail.net Subject: Suspicious website
You will receive an e-mail with a link to activate your new alias.
- Continue with your registration on the suspicious website and provide your honeymail.net address.
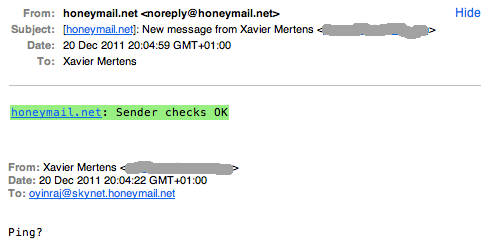
- The first time you will receive a mail to this address, honeymail.net will create a link between the sender and your alias (a “one-2-one” link). Then the message will be delivered to your private address:
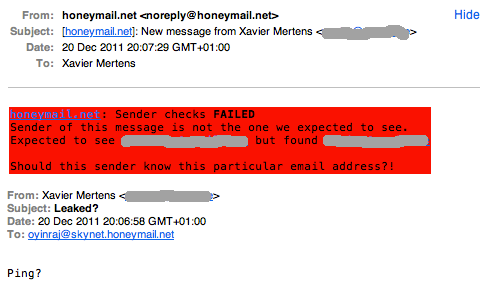
Now, your alias is linked to the sender! If you receive an e-mail to your alias from another source, you’ll be warned. - To test, just send a new e-mail from another account:
To manage your aliases, simply send other e-mails. Aliases can be temporary paused and resumed. This is useful to simply drop all e-mails sent to them. Another nice operation is the “reset“. It deletes the existing link with the source e-mail address. The website is clear and easy to use, have a look for more details!
At the moment, honeymail.net is still a proof of concept but it looks very promising. I recommend it if your privacy is a main concern!
Kudos to the new project ! A similiar service I have been using for years is spamgourmet.com
Try it out. And good luck for project completion