 The first day started (too) early with Rafal Los’s (@Wh1t3Rabbit) briefing about “Defying Logic – Theory, Design, and Implementation of Complex Systems for Testing Application Logic“. Rafal explained some techniques not “brand new” but which are really interesting. The goal of application logic testing is to discover what an application does and how. What are the components and how they are interconnected together. The goal is not anymore to hack the application from a technical point of view but to hack the business process. A nice example was given with an application allowing to collect loyalty points before confirming the financial transaction! Often, organizations are not prepared to handle this kind of issue: No SQL injection nor remote shell to change the data, is required just attack the application behavior. This is not a new topic, for a while developers have to perform validation of all data passed to their application. But, surprisingly, this issue is not in the OWASP Top-10. To find breaches in application logic, human thought is required and automated tools cannot be use “out-of-the-box”. One question popped up in my mind after the presentation: What about legal aspects? By abusing application logic, we do not abuse the resources of a server or application. You don’t break anything. How to deal with this? I liked this talk!
The first day started (too) early with Rafal Los’s (@Wh1t3Rabbit) briefing about “Defying Logic – Theory, Design, and Implementation of Complex Systems for Testing Application Logic“. Rafal explained some techniques not “brand new” but which are really interesting. The goal of application logic testing is to discover what an application does and how. What are the components and how they are interconnected together. The goal is not anymore to hack the application from a technical point of view but to hack the business process. A nice example was given with an application allowing to collect loyalty points before confirming the financial transaction! Often, organizations are not prepared to handle this kind of issue: No SQL injection nor remote shell to change the data, is required just attack the application behavior. This is not a new topic, for a while developers have to perform validation of all data passed to their application. But, surprisingly, this issue is not in the OWASP Top-10. To find breaches in application logic, human thought is required and automated tools cannot be use “out-of-the-box”. One question popped up in my mind after the presentation: What about legal aspects? By abusing application logic, we do not abuse the resources of a server or application. You don’t break anything. How to deal with this? I liked this talk!
The second talk was presented by Tom Keetch from Verizon Business. Tom presented his research about sandboxes: “Escaping From Microsoft Windows Sandboxes“. Some “critical” applications (read: targeted by lot of threads) implement today a sandbox where they process the data in a “safe” way… Not so safe! Such sandboxes are based on the operating system facilities based on user-mode components. Tom reviewed three implementations: Internet Explorer, Adobe Reader and Google Chrome. Before going deeper, it’s important to understand why/how attackers will try to escape from a sandbox and how to defeat them (exploit mitigation):
- By increasing the cost of the exploitation
- By decreasing the target value
Two potential failures are: a value not enough decreased or a cost too low to block attackers. Tom insisted on some resources that are not protected by the sandboxes like network access or the “same origin policy“. Very important to keep in mind: such sandbox implementations will protect the integrity of data but not their confidentiality! It’s also possible to access the clipboard or other Windows resources. Question: How many of you copy/paste passwords via the clipboard?
Just after the coffee break, Andrés Riancho spoke about “Web Application Payloads“. Based on w3af, Andrés explained how to abuse system using GET/POST HTTP requests. Those requests are generated by web application payloads running on the attacker box. Many demos were performed. I did not follow the entire presentation due to the preparation of our workshop.
Wim Remes (@wimremes) and myself presented a workshop about OSSEC. The title was “Grepping for Gold“. The goal was to introduce the tool to the attendees but also to make them aware of the need for a log management solution whatever their size and business. Fifty people attended the first (theoretical) and twenty people stayed for the live exercises. For a first try, it was not so bad and we got nice feedbacks. Difficult to cover all aspects of OSSEC in three hours! Our slides are already available online here.
Finally, Bruce Schneier came for a keynote about cyber-war. Always interesting to listen to people like him. It seems he could talk for hours without any break. I like his words about the “Internet kill switch“: “a definition of stupidity”.
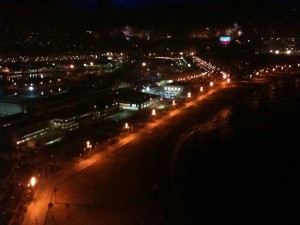
The first day ended with the sponsors party and the extra IOActive party. This year, they moved it from Friday to Thursday evening. Good idea! It was located on top of the “W” hotel in Barcelona. Nice view from the 25th floor and nice cocktails!
Stay tuned for the day #2! I’ll have more time now that my workshop is over. I recommend you to follow Frank’s blog (@seccubus) who also follows the conference.