
Next step in my investigations with OSSEC. The possibilities of OSSEC are awesome and could clearly, in some case, replace a commercial log management solution! After collecting the Secunia vulnerabilities into OSSEC, I switched to the “dark side”: the Microsoft Windows agent. The USB sticks are very popular at users level and are a nightmare for system administrators. It’s so easy to get files away with critical data or to inject malicious code into the network via suspicious USB sticks. Why not try to detect if an USB storage is used on a Windows workstation or server?
First of all, this solution is certainly not bullet-proof! My goal is to demonstrate how OSSEC can make the life of security professional (a little) more easier. OSSEC comes with an agent for the Microsoft operating systems. This is only a “agent”, it cannot be used in stand alone mode and cannot act as its own server. It is controlled from an OSSEC server running on UNIX. Like the other agents, it can perform the following checks:
- Event log monitoring (Application, Security & System)
- Integrity monitoring
- Security Policy monitoring
- Log files monitoring (IIS included)
- Active response
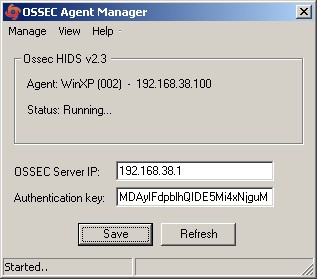
The installation is pretty straight forward via a Windows installer. Once done, the OSSEC agent will be executed as a standard Windows service:
C:\Temp> net start | find "OSSEC" OSSEC Hids
The agent is managed via a nice GUI – the “Agent Manager”. Available actions are:
- To start/stop the agent
- To edit the configuration file
- To display the log file
On the server side, there are three important files which define the security policy of Windows hosts [Note: I’m assuming that your OSSEC server is already running. Consult your documentation if needed]. These are located in the directory “$OSSEC_DIR/etc/shared/“:
- win_applications_rcl.txt
- win_audit_rcl.txt
- win_malware_rcl.txt
They come with predefined rules which should be sufficient to monitor a classical Windows environment. The rules are based on the following syntax:
#[Entry name] [any or all] [reference] # type:<entry name>; # # Type can be: # - f (for file or directory) # - r (registry entry) # - p (process running) # # Additional values: # For the registry , use "->" to look for a specific entry and another # "->" to look for the value. # For files, use "->" to look for a specific value in the file. # # Values can be preceeded by: =: (for equal) - default # r: (for ossec regexes) # >: (for strcmp greater) # <: (for strcmp lower) # Multiple="Multiple" patterns can be specified by using " && " between them. # (All of them must match for it to return true).
(For a complete overview and example, check out the OSSEC Wiki)
To detect the the presence of an USB stick (let’s focus of course on pure storage devices – we don’t care of mouse, keyboard or any other gadget), we will adapt the file “win_audit_rcl.txt“. Every time an USB storage device has been inserted into a port, the following registry key is incremented (+1 for each device inserted):
HKLM\SYSTEM\CurrentControlSet\Services\USBSTOR\Enum\Count
To detect the presence of a USB stick or disk, let’s define the following new rule in win_audit_rcl.txt:
[USB Storage Inserted] [any] [] r:HKLM\SYSTEM\CurrentControlSet\Services\USBSTOR\Enum -> Count -> !0;
Save the file and push the changes to all your Windows agents. If everything runs fine, insert an USB stick in a monitored Windows machine and the following event will be received by the server:
** Alert 1268430696.36057: - ossec,rootcheck, 2010 Mar 12 22:51:36 (WinXP) 192.168.38.100->rootcheck Rule: 512 (level 3) -> 'Windows Audit event.' Src IP: (none) User: (none) Windows Audit: USB Storage Detected.
Cool! But not very powerful. The alert will be triggered only if the USB device is connected when the rootkit scan is performed! If a user connects and disconnects an USB device between two rootcheck scans, nothing will be detected. A possible solution could be to reduce the interval between two rootcheck executions but this will requires more resources and could affect the overall system performances. Another alternative is to go back to the Windows registry. and look for other solutions. It is a wonderful source of information, almost everything is written there! There is another interesting key in our case:
HKLM\SYSTEM\CurrentControlSet\Enum\USBSTOR
The first time an USB storage device will be connected, the key will be created and a sub-key with the device information. Example:
HKLM\SYSTEM\CurrentControlSet\Enum\USBSTOR\Disk&Ven_USB&Prod_Flash_Disk&Rev_0.00
We can now create a second rule in win_audit_rcl.txt like:
[USB Storage Detected] [any] [] r:HKLM\SYSTEM\CurrentControlSet\Services\USBSTOR;
Restart again OSSEC and pushes the new audit files to your agents! Check your alert.log for messages like this one:
** Alert 1268681344.26683: - ossec,rootcheck, 2010 Mar 15 20:29:04 (WinXP) 192.168.38.100->rootcheck Rule: 512 (level 3) -> 'Windows Audit event.' Src IP: (none) User: (none) Windows Audit: USB Storage Inserted.
Note that this notification will remain while the registry key is present! It’s your job to clean up the Windows hosts which reported the alert! I’d like to increase the rootcheck rule accuracy by detecting if a new USB device has been inserted but at the moment, I didn’t find how to achieve this. If you have tips & trick, please share!
To conclude with this example, you can see how easy OSSEC can help you to keep an eye on threats inside your infrastructure. A next funny step could be to enable the remediation and configure the OSSEC agent to execute a script which will prevent from connecting USB storage devices!
I’m not sure to understand why you’re trying to do. Could you give more details?
Hi, Im pretty new with Gossec, Im trying to develop some rules, I could see the first and the second alert the first time but now it doesn’t work any more. What do you mean with clean up the windows hosts. Sorry Im very with this stuff. Thanks for the help.
Daniel (the owner of the OSSEC project) posted a new article on his blog[1] about the USB detection…
The new OSSEC release (2.4) will introduce a new feature: check_diff[2] which will greatly increase the ease of USB devices detection!
[1] http://www.ossec.net/dcid/?p=199
[2] http://www.ossec.net/dcid/?p=198
Thanks for this tip ! Great explaination, may test it very soon. Untrusted USB storage is a major pain because of Windows viruses & associated autorun.inf …
I hope you will be in a funny day to follow the funny step ^^
Very nice article!
Another approach which would make this real-time is to simply monitor the creation of HKLM\SYSTEM\CurrentControlSet\Enum\USBSTOR\Disk&Ven_USB&Prod_Flash_Disk&Rev_0.00 or HKLM\SYSTEM\CurrentControlSet\Services\USBSTOR\Enum using a real-time file integrity alert. These don’t get sent by default, but if you created a rule dependent on rule 554, then you’ll know pretty much as soon as it happens.
-Michael Starks