One of my sources of threat intelligence is a bunch of honeypots that I’m operating here and there. They are facing the wild Internet and, as you can imagine, they get hit by many “attackers”. But are they really bad people? Of course, the Internet is full of bots tracking
Handling Malware Delivered Into .daa Files
Bad guys are always trying to use “exotic” file extensions to deliver their malicious payloads. If common dangerous extensions are often blocked by mail security gateways, there exists plenty of less common extensions. These days, with the COVID19 pandemic, we are facing a peak of phishing and scams trying to

[SANS ISC] Obfuscated with a Simple 0x0A
I published the following diary on isc.sans.edu: “Obfuscated with a Simple 0x0A“: With the current Coronavirus pandemic, we continue to see more and more malicious activity around this topic. Today, we got a report from a reader who found a nice malicious Word document part of a Coronavirus phishing campaign. I

[SANS ISC] Malicious JavaScript Dropping Payload in the Registry
I published the following diary on isc.sans.edu: “Malicious JavaScript Dropping Payload in the Registry“: When we speak about “fileless” malware, it means that the malware does not use the standard filesystem to store temporary files or payloads. But they need to write data somewhere in the system for persistence or

[SANS ISC] Very Large Sample as Evasion Technique?
I published the following diary on isc.sans.edu: “Very Large Sample as Evasion Technique?“: Security controls have a major requirement: they can’t (or at least they try to not) interfere with normal operations of the protected system. It is known that antivirus products do not scan very large files (or just

InfoSec Conferences Canceled? We’ve Hours Of Recordings!
If you planned to attend some security conferences in the coming weeks, there are risks to have them canceled… Normally, I should be now in Germany to attend TROOPERS… Canceled! SAS2020 (“Security Analyst Summit”)… Canceled! FIRST TC Amsterdam… Canceled! And more will probably be added to the long list. And,

[SANS ISC] COVID-19 Themed Multistage Malware
I published the following diary on isc.sans.edu: “COVID-19 Themed Multistage Malware“: More and more countries are closing their borders and ask citizens to stay at home. The COVID-19 virus is everywhere and also used in campaigns to lure more victims who are looking for information about the pandemic. I found
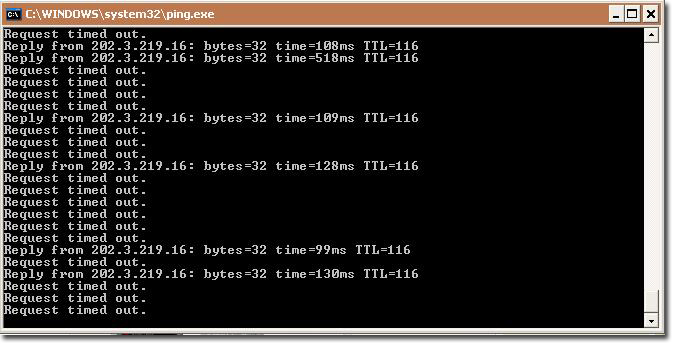
Remote Access Bad Stories
With the COVID19 pandemic ongoing, more and more countries are taking strong decisions to limit the movements of people. This is one of the best behavior to prevent more and more people to be infected. This has a big impact on many organizations that are now facing a business continuity

[SANS ISC] Agent Tesla Delivered via Fake Canon EOS Notification on Free OwnCloud Account
I published the following diary on isc.sans.edu: “Agent Tesla Delivered via Fake Canon EOS Notification on Free OwnCloud Account“: For a few days, there are new waves of Agent Tesla landing in our mailboxes. I found one that uses two new “channels” to deliver the trojan. Today, we can potentially receive

[SANS ISC] A Safe Excel Sheet Not So Safe
I published the following diary on isc.sans.edu: “A Safe Excel Sheet Not So Safe“: I discovered a nice sample yesterday. This excel sheet was found in a mail flagged as “suspicious†by a security appliance. The recipient asked to release the mail from the quarantine because “it was sent from