With the COVID19 pandemic ongoing, more and more countries are taking strong decisions to limit the movements of people. This is one of the best behavior to prevent more and more people to be infected. This has a big impact on many organizations that are now facing a business continuity issue: How to allow people stuck at home to perform their day to day job? In some cases, it’s impossible to work from a remote location (ex: when your organization has to “produce” some goods). In others, like cybersecurity, it’s much more convenient. I’m working remotely for some of my customers for years! With some exceptions… In very sensitive (classified) environments, you, as a contractor, have to be onsite.
But, for one week, things are moving ahead! Many organizations are implementing remote access solutions to ensure their business continuity. And, things done in an emergency are rarely the best ones! Here is a recap of problems or “don’t do this” situations that I faced or heard for a few days:
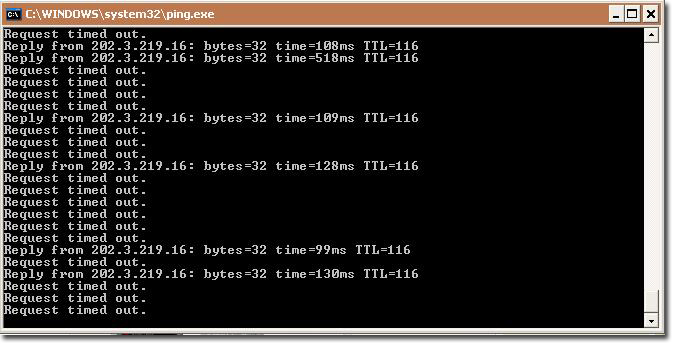
- The bandwidth dedicated to the remote access is not properly dimensioned and people can’t work or simply can’t log in. This is especially true when you use VDI (“Virtual Desktop Infrastructure”) or remote control tools.
- The remote access solution is used by regular AND power users. The administrators can’t simply access the infrastructure to fix users’ rights, close accounts, etc…
- There is a lack of hardware MFA tokens: all of them have been assigned (and nothing is foreseen to use software tokens)
- There is a license issue on the remote access platform that allows only 1/3 of the users.
- The bandwidth for remote access is shared with critical services like corporate web servers, API servers, …
- The channel to safely exchange critical data is not properly defined. If an employee can’t be met physically, how to exchange credentials, certificates, etc…
- It’s tempting to disable security controls to reduce the issues faced by users and flood the helpdesk. Is it a good idea to disable the host-checker feature of your VPN client to allow more people to connect from personal computers? Risks must be evaluated.
- No, “Any to Any: Allow” is not an emergency rule in your firewall…
And if you don’t have a remote solution already in place? It’s tempting to deploy services quickly…
- Don’t expose in the wild services running on top of critical protocols like RDP, SMB, HTTP, … (use them behind a VPN)
- Avoid low-cost remote access protocols like VNC, TeamViewer or ZoHo, … (same advice, use them behind a VPN)
- It’s tempting to quickly share data over the Internet. Be 200% sure to use very-very-very-strong passwords!
- Using the cloud might be your survival solution but keep in mind that you loose control of your data in many cases.
Keep this in mind and update your BCP (“Business Continuity Plan”) with those lessons learned once we’ll get rid of COVID19! Stay safe at home!