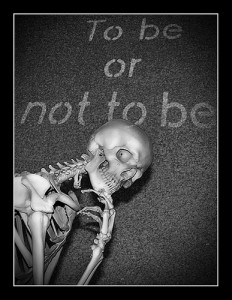
 The idea of this post came after I read another blog post from Light Blue Touchpaper. Picking a good password is a never-ending story. You can find multiple recipes, tips & tricks. One of the way, also promoted by Google is to create passwords based on quotes or common sentences. The example provided by Google is the Hamlet’s quote: “To be or not to be, that is the question“. Take the first letter of each words to start your password: “tbontbtitq“. This is still an easy crackable password. Replace some letters by numbers (“i” = “1”, “o” = “0”). The new version will be: “tb0ntbt1tq“. Replace some common English words by a number (“to” = “2”, “for” = “4”): “2b0n2bt1tq“. And finally, add a special caracter: “2b0n2bt1tq!“. Strong password isn’t it?
The idea of this post came after I read another blog post from Light Blue Touchpaper. Picking a good password is a never-ending story. You can find multiple recipes, tips & tricks. One of the way, also promoted by Google is to create passwords based on quotes or common sentences. The example provided by Google is the Hamlet’s quote: “To be or not to be, that is the question“. Take the first letter of each words to start your password: “tbontbtitq“. This is still an easy crackable password. Replace some letters by numbers (“i” = “1”, “o” = “0”). The new version will be: “tb0ntbt1tq“. Replace some common English words by a number (“to” = “2”, “for” = “4”): “2b0n2bt1tq“. And finally, add a special caracter: “2b0n2bt1tq!“. Strong password isn’t it?
If quotes are well-known, there are chances(risks) that people use it as said in the Light Blue Touchpaper article: more people used “tbontb” as password! Despite the method used to generate your passwords, they must remain unique to you!
Again, Internet is your best friend: they are plenty of sources to download famous quotes, proverbs, lyrics. I also downloaded my copy of the RockYou passwords list and started to play. Let’s search for the string “tbontb“:
$ grep tbontb rockyou.txt tbontbtitq tbontbtit9 tbontbtit tbontb65 tbontb2 tbontb18 tbontb04 tbontb rytbontbtitq
As you see, in some cases, a suffix has been added with number. By experience, this is often something like:
- The password owner’s age
- An office number
- A week or month number (classic when password policies force to change passwords at regular interval – people are lazy)
Also some letter have been replaced by their number equivalent (“q” = “9”) to make the password more “l33t“. Another exercise: I downloaded a list of 523 English proverbs and converted them in simple strings (Example: “A chain is only as strong as its weakest link” –> “acioasaiwl“). Let’s search for the strings:
cat proverbs.txt | while read L
do
egrep ^$L$ rockyou.txt
done
Results: 30 occurrences found! Not bad isn’t it?
Worse, but certainly not from an attacker point of view, the choice of the sentences is often directly related to your target. Ex: gamers or teenagers will use lyrics from songs in the charts or popular quotes (Do you remember the famous “All Your Bases Are Belong to Us“?). The Perl script I used to generate the password is available (“as is”) here. A long time ago, I wrote a “Social Dictionary Generator“, the link is here.
To conclude, for me the best way to handle passwords is to generate them randomly and store them in a password manager. In this case, you only have to take care of your master password. Of course, this last one must be super-strong or better based on a two-authentication factor…
Hi Xavier,
I’m happy some people like you see this. Using a sentence as a mean of remembering a password is not bad as long as this sentence is not in a dictionnary.
Also, why do we still advise to use numbers instead of letters ? Do we really believe that hackers have not figured out l33t encoding ?
I agree with the fact passwords should be random and stored in a secure medium. However, the problem of access to the password manager worries me – either you’re using some kind of tamper-resistant device and you can easily use two factor authentication (let’s say your passwords are stored in a pin protected smartcard or in a TPM chip, either they’re stored in an unsecure storage (hard disk, cloud) and the only way to protect it reliably is a passphrase.
I dream of a world where passwords are a thing of the past, and we all use smartcards for authentication and encryption.
Aris
Other good idea
– car plate number of your father
– add some one in your phonebook like http://www.infobel.com/en/uk/001_taxis_ltd/stroud/businessdetails.aspx mix name and phone number
TAXIS LTD + 01453755989 -> 0T4a5x3i7s5L5T9D89