 Yesterday, the three OWASP Benelux chapters organized together their annual OWASP BeNeLux day. This edition was held at the Fontys Hogeschool in Eindhoven (NL). First detail of this year, the weather conditions! After more than three hours of driving on snowy roads, I finally reached Eindhoven. Just in time for a coffee and to connect to the WiFi before the talks.
Yesterday, the three OWASP Benelux chapters organized together their annual OWASP BeNeLux day. This edition was held at the Fontys Hogeschool in Eindhoven (NL). First detail of this year, the weather conditions! After more than three hours of driving on snowy roads, I finally reached Eindhoven. Just in time for a coffee and to connect to the WiFi before the talks.
The event started with a welcome word by the local Netherlands chapter and by Seba Deleersnyder (from the Belgium chapter), who reviewed the status of some projects amongst the huge amount currently in the pipe. In a few words:
- New risk based OWASP Top-10
- New testing guide and code review guide (v4). Release in the beginning of 2011?
- OWASP numbering system
- pythonsecurity.org
- New mobile group started
- Improving the browser security with Mozilla
- OWASP O2 platform
- Modsecurity CRS (“Core Rule Set“).
The complete list of those projects (122!) is available here.
The first speaker was Marco Balduzzi from Eurecom. He talked about the “Clickjacking” attack. In a few months, the name “ClickJacking” became very popular. The number of hits returned by Google keeps growing but is it really a threat or a buzz? This is a real type of attack: Marco reviewed the “Twitter Bomb” attack which generates self-replicating Twitter messages by abusing some HTML/CSS features. But what is the coverage of such attacks on the Internet? To track them, Marco built an automated system based on browser scenarios. To replicate the user behavior, he uses the X.org libraries to move the mouse, generate clicks. The browser is protected by NoScript & ClickIDS (to reduce the risk of false positives). He scanned an initial set of 70K URLs and generated more than one million of Internet pages using a cluster of 10 Linux VMs (at a rate of 15K pages/day). The results? 37% of pages contained iFrames but only 0.16% of transparent iFrames. Only two (2!) real attacks were detected. Marco’s conclusion is that ClickJacking attacks really exists but are not the preferred method used by malicious guys. Finally, he reviewed some mitigations techniques like the X-FRAME-OPTIONS.
Radu State, from the University of Luxembourg, made an excellent talk about “Owning networks via VoIP and web attacks“. Normally, VoIP is not in the OWASP scope but Radu explained how to conduct web attacks through SIP devices. The presentation started with examples of common attacks against SIP phones. Most of them are vulnerable to attacks, often just be sending a single packet! The worst case is the one against the China’s Grandtouch phones which can be easily switched into “spy mode” (is it a bug or a feature?). To search for SIP vulnerabilities, Radu uses a fuzzer called KIF. The second part focused on ways to use SIP devices to perform SQL injections and XSS attacks. Example:
INVITE sip:<sqlinjection>@PBX
SIP was renamed by Radu as “UFBP” or “Universal Firewall Bypass Protocol“. Indeed, SIP is often allowed through firewalls without any further inspection and SIP proxies are available from the Internet. Another issue with IP phones: they are considered by users as “just a phone” but it’s a computer. They also embed web servers and this is the attack vector. Even if your phones are connected on a dedicated VLAN, the users will access them via their browser on the internal LAN. Some demos (videos) showed how to create a user in the VoIP system, how to redirect the user to malicious sites or perform network reconnaissance. A great talk!
Just before the lunch, Matias Madou presented “Finding back-doors in code“. This was the same talks as the one presented during BruCON in September. Matias explained why software have back-doors, what are the motivations of insiders (gain, vengeance) and what type of the different types of back-doors found in the code (with examples). Then, he reviewed methods and techniques to analyze the code and find them.
Thierry Zoller presented “How to NOT implement a Payback/Cashback” system. Thierry described what are the “Payback” systems and why they are so popular.
“In marketing generally and in retailing more specifically, a loyalty card, rewards card, points card, advantage card or club card is a plastic or paper card, visually similar to a credit card or debit card, that identifies the card holder as a member in a loyalty program. Loyalty cards are a system of the loyalty business model. In the United Kingdom it is typically called a loyalty card, in Canada a rewards card or a points card, and in the United States either a discount card, a club card or a rewards card. Cards typically have a barcode or magstripe that can be easily scanned, and some are even chip cards. Small keyring cards (also known as keytags) which serve as key fobs are often used for convenience in carrying and ease of access.” (Source: wikipedia.org)
Then he reviewed the weaknesses of a specific system massively deployed. Upon Thierry’s request, no more information will be disclosed here.
Next talk was about “Botnets / Bredolab”, presented by Michael Sandee. He started with a generic introduction about botnets. They receive more and more attention from medias and lead to hot debates. Bredolab is the name of a piece of malware (called “BManager“). Bredolab is in fact available for sale and generate a lot of different botnets. Michael explained how they are deployed and how they are managed to generate huge amount of money. Good cybercrime review!
Nick Nikiforakis discussed about the privacy of file sharing services. Those services are common today (You certainly already uploaded a file to Rapidshare). If you take care of your privacy, select your file sharing service wisely! Nick explained how most of those services work. No surprise, they are cloud based and suffer of the common cloud weaknesses: unknown physical locations, privacy but also availability. A cloud environment can also suffer of data loss (examples: Amazon EC2 in 2007 or Microsoft and the T-Mobile Sidekick data in 2009). Back to the file sharing services, they are very easy to use: just upload and share the URL returned by the service. But how are generated those URLs? Rick analyzed height well-known services. He uploaded several times the same file in a short interval and tried to find how they generated the returned tokens. File sharing services protect themselves trough obscurity (files can be accessed only by their ID). Really? Most generated keys are predictable. If you have an initial valid token, you can enumerate the whole database of files. Rick tried that via a script and get.. too much data to be analyzed manually! Amongst the grabbed files, he found: death certificates, bank statements, company budgets & salaries, medical transcriptions (often file sharing services are used by translation services). Once you get the information, you just use it to conduct regular attacks (espionage, mailing, racket, etc). To conclude: take care when choosing your file sharing service. Always encrypt the file content and delete it once shared with your peers. For companies, it could be a good idea to restrict them.
Chen Gour-Arie talked about “The social networking corporate threat” or what are the threat added by social networks in corporate environments. They are used by “internal” users but organizations also use them as a communication channel. Chen gave some figures, threats and how to penetrate an organization using social network. What are the risks?
- Information leakage
- Social engineering
- network infiltration
- Application layer attack
The path is always the same: study -> approach -> attack. Via a demo video, he explained how to exploit a corporate environment in less then 7 mins!
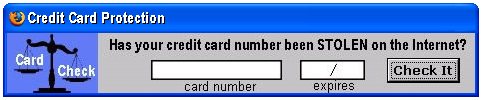
Finally, Walter Belgers presented “Attacking is easy, defending is hard“. Working as a defender, you have to find ALL the weaknesses of an infrastructure. From the attacker perspective, one is enough! The weak spots are the applications, the users, the physical access (ex: a shared collocation). Walter reviewed the common problems when a physical access to the device is possible. He also explained best practices with softwares: you do not only need to install a software, you need to configured it (hardening) properly. Too much application are installed with default settings (Scada products are a good bad example). How to protect? By using multiple lines of defense, by logging and monitoring everything (detection) and by having a plan ready (reaction). Users education (awareness) is also mandatory. How will users react to this:
The day ended with the CTF results and acknowledgements. Book already the following event: 30rd November – 1st December 2011 in Luxembourg. Great organization by OWASP!
Thanks for those useful summaries you provide.