
Question: Do you remember the Amiga computer? I was an early fan is this wonderful machine and operating system. Starting with AmigaOS 2.0, a macro language called ARexx (with a letter “A” like “Amiga) was added. This language, derived from REXX (“REstructured eXtended eXecutor“) developed initialy by IBM. The power of ARexx was the communication skills with other applications using scripts. If the application had an ARexx port, it was possible to interact with it. A nice example was the automation of repetitive tasks (like images conversions). It was in 1990!
Since this wonderful period, we saw a lot of other solution developed to interact with applications. On UNIX, you can interact with a process using named pipes. There are also commercial solution like the OPSEC (“Open Platform for SECurity“). protocol developed by Checkpoint.
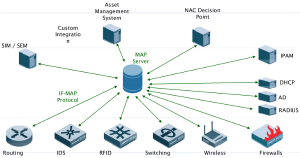
Did you ear about the IF-MAP protocol? It was announced in 2008 by TNG:
“Trusted network connect–part of the Trusted Computing Group–published its Interface for Metadata Access Point protocol on April 28 to provide a common framework for sharing event metadata. This means there’s finally a way for security and network devices from a variety of vendors to communicate, and thus make better assessments on whether to grant or deny access to everything from PCs to switches.”
Modern IT infrastructures become more and more complex and integrate several types of devices. In most cases, devices cannot talk to each other. If an IDS alert is send to the network administrator, his job is to take actions like blocking the suspicious traffic with a firewall. And if it was fully automatic? That’s the purpose of IF-MAP. Initially developed as a strong base for a NAC solution, IF-MAP is flexible enough to be used as an information resource by any networked device. Some commercial manufacturers already tested it. We can imagine so much interaction between network components like:
- Shut down a switch port if suspicious activity is detected by an IDS.
- Rate-limit an Internet connectivity for an IP detected on P2P networks.
- Changing a user profile (from full-internet access to restricted access) if suspicious traffic is detected
- Temporary allow some applications thru a firewall (ex: patches download)
- … (just let your imagination work!)
IF-MAP relies on a client-server approach where clients can retrieve or publish metadata about assets. The MAP servers keeps an instantaneous view of the network:
Today, open source application are moving to IF-MAP! There is an ongoing project in a German university called IRON or “Intelligent Reaction on Network Events“. Based on well-known open source applications (Nagios, Snort, ISC DHCP and netfilter), students are busy to extend them to support IF-MAP. The goal of this project is to mitigate today’s threats like malware infection, data leakage or internal attacks. The project started in September and sounds promising! Some source are already available.
Project homepage: IRON.
Thanks for mentioning our project. We are currently finalizing the first prototype and expect it to be released in January. The currently available sources focus on “plain” TNC, without support of IF-MAP. Some further information about IRON can be found here: http://trust.inform.fh-hannover.de/joomla/index.php/projects/iron/92-iron-overview.
@Matthew: Yes, false positives will be a challenging issue when you try to add real-time security measures to a network. However, to whitelist your own DNS servers for your IDS should not be a big deal.
Cheers, Ingo.
Great Post!
It’s nice to see people considering how to build the “self-defending network”.
Challenges with this sort of approach is that a false positive could have a lot of downstream impact. E.g. IDS/IPS sees an “attack” locks down a port/application etc.
I remember when I linked an IPS to a firewall to automatically block people port scanning. The IDS saw our Primary DNS as a port scanner and blocked it. Lucky I had a secondary, my self defending network shot me in my foot!