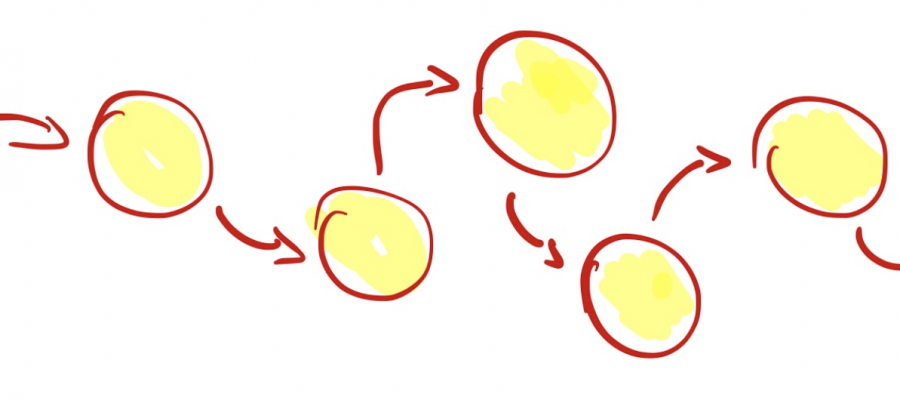
I’m using Tor for so long that I can’t remember! The main reasons to use it are to access some websites while preserving my anonymity (after all that’s the main purpose of Tor) but also to access dangerous resources like command & control servers or sites delivering malicious content. The