I’m just back from the second day of hack.lu. The day started early with Patrice Auffret about Metabrik! Patrice is a Perl addict and developed lot of CPAN modules like Net::Packet or Net:Frame. That’s why he had the idea to write a new UNIX shell working like a Perl interpreter.
So, Metabrik was born. It’s not only a shell but a true language that can be empowered with “briks“. A brik is a development/prototyping platform used to quickly build your own tool. You can also see it as a wrapper around existing tools.
Patrice’s philosophy is: “Everything should be possible from the CLI” but in an automated way and normalized syntax and in a human readable form. And indeed, all external tools are interfaced in the same way and results provided in the same format.
To demonstrate the power of Metabrik, Patrice performed some demonstrations. The first one showed how easy it is to create an array and use CPAN module directly from the shell. So easy! At the moment, Metrabrik has 200+ briks available. I’m sure you will find something interesting. Others demonstrations were performed. Personally, I liked the malware analysis automation. Patrice interfaced VirtualBox with Metabrik to spawn a guest VM, execute the malware and grab results (ex: by performing a memory acquisition with Volatility). If you are interested, have a look at his blog post here. Metabrik is a very nice tool but it will require some time to master it. The only comment that I received while discussing with friends about it was: “Why in Perl and not in Python?“. Please, no flame war! 🙂
The second slot was assigned to a master speaker: Saumil Shah. I don’t need to present him, he’s a regular speaker at hack.lu. Every time, I came on stage with a nice presentation. This time, in 2016, it was less technical. The title was “2016:The Infosec crossroadsâ€. It was more a reflexion about the defence. Everything started with a fact: “Today’s attacks succeed because the defence is reactiveâ€.
We have to be honest: attacks evolve way faster than defences. They are shifting regularly between different targets depending on opportunities (servers, workstations, IoT, …) because attackers just follow the money. If there is a change to gain more money, attackers will adapt their techniques. If today’s fashion is focusing on breaches, attackers don’t follow rules.
 Another fact: the defenders tried to buy back their bugs via bug bounty programs. It’s not a game anymore but a business. It’s a zero acquisition market. Then, Saumil talked about the (d)evolution of users. Advanced technologies are advanced and if you don’t know how to use them, it may become dangerous. What is the good reactive approach to defence? For Saumil, compliance and security are not the same. Attackers don’t follow rules. Today’s infosec defence remains based on rules, signature updates and machine learning. Existing strategies do not match attackers tactics. We have to switch from a reactive to a proactive approach! To achieve this, Saumil presented his own seven axioms:
Another fact: the defenders tried to buy back their bugs via bug bounty programs. It’s not a game anymore but a business. It’s a zero acquisition market. Then, Saumil talked about the (d)evolution of users. Advanced technologies are advanced and if you don’t know how to use them, it may become dangerous. What is the good reactive approach to defence? For Saumil, compliance and security are not the same. Attackers don’t follow rules. Today’s infosec defence remains based on rules, signature updates and machine learning. Existing strategies do not match attackers tactics. We have to switch from a reactive to a proactive approach! To achieve this, Saumil presented his own seven axioms:
- Collect everything: build a security data warehouse, retention is cheaper than retention,
- Can’t measure? Can’t use it!
- Proper Pentesting (are you more scared by pentesters then auditors?)
- User ratings
- Set booby traps
- Analysis decides actions
- Buy-in from the top
It was a very nice presentation but, let’s be honest, very difficult to put in practice. From both sides, money is the driver! Attackers want to make more money when defenders are asked to reduce costs!
After the morning coffee break,Fitzl Csaba and Miklos Desborders came to present their tool to automate the exploit generation and JavaScript analysis automation. The first part of the talk was focusing on automatic exploit development. If you’re an exploit developer, you know that this process is time consuming. It is an heavily manual intensive process based on recurrent tasks: start the process, attach the debugger, crash the application, analyze results, modify exploit, restart. When an EIP overwrite location is found, we have to examine the memory layout and registries, jump to shell code, generate it and put all the stuff together. To automate this, they wrote a tool in Python which used the PyKD library to attack to a WinDBG instance. What does it do? At the moment, it works for classic BoF, it can bypass ASLR, works for network and file based exploits. It creates exploits and automate the testing process. They performed a demo of the tool which found a vulnerability in a badly written application, generated the shell code to spawn a classic calc.exe. It sound awesome. The tool will be released after the conference.
The second part of the talk focused on a JavaScript analysis automation tool. Like classic exploits, it is also time consuming and a challenging process. The goal is also to get rid of anti-debugging and anti-reversing techniques. The process is based on the following steps: deobfuscate the code, catch the function before its execution, locate the exploit code and understand the shellcode. To achieve this, the speakers developed another tool that automates this process (currently working only on IE11). The exploit generator code is available here.
Today’s keynote was presented by Quinn Norton: “A network of sorrows, Small adversaries and small allies†or a status of the Internet… It started with a nice picture: Attackers are everywhere!
Quinn reviewed several issues on the Internet today and how people/organization react to security issues. Example: many schools and hospitals are hit by ransomware in the US. It seems also that  teenagers are more concerned about being spied by their parents than by the NSA. The Internet introduced new technologies that are not well understood by users. This is a classic behaviour:
No you won’t have my SSH key but I can give you access to my desktop via TeamViewer!
Keep in mind that users must be educated to face the changing world. We ask our users to listen to our advices but we should also listen to the users. They use tools (and the security issues related to them) to solve their problems.
After a good lunch and discussions with peers, there was a second set of lightning talks but I did not attend them, too busy to exchange with peers (that’s also the goal of security conferences!). The next talk focused on SAP and how to exploit it via default accounts.
This was presented by ERP-SEC. For most of us, SAP is a boring environment but being using by all of the big players in many business fields and the data stored in SAP systems being highly valuable, such environments are good targets. Of course, patches and security fixes are released by SAP but patching means downtime and downtime means unavailability which means loss of money. So, systems are not often patched. Two big attack vectors for SAP have been identified by ERP-SEC:
- Default accounts
- SAP RFC gateway (then pivoting)
A SAP system may have many default accounts, the first method will be the preferred one. One slide full of default usernames and passwords was displayed. A fact reported by ERP-SEC: 100% of tested SAP instances had at least one default account. For customers, the key question is: “Are those users in my system?†Most of them have! Indeed, the SAP Solution Manager may require new accounts when some features are activated like enabling some monitoring features in the product. An important remark is that a default account alone does not immediately mean a bug security hole. It must be combined with another vulnerability (SQL execution, SMB relay, OS command injection, …) to fully compromise a system. The second part of the presentation was based on demos. How to protect? Nothing new here: Change default passwords, delete / disable unused users if not required. There is nothing new but often not applied.
The next talk was about GPO’s (Microsoft Group Policies). The idea of the speakers was to use them to deploy a malware and get persistence. The goal of the talk is to create some awareness or to give more evil ideas to pentesters. How does it start? Microsoft recommends using GPO to solve management issues. Example: to enable WMI on all workstations.
Mainly used in companies, GPO’s are also badly managed:
- It tends to be messy
- They are stored everywhere
- There is a lack of naming convention
To achieve their goal, they used a well-known framework called PowerShell Empire. The first  demo was about to set persistence by creating a ‘RunOnce†registry key which contains the malicious exe file (“calc.exe†in this case for demo purposes). The second demo was about to find a way to quickly search for a specific file across all the workstations. To achieve this, they created a new GPO that enable WMI and open the local firewall to allow the attacker to connect to the victim. It’s a nice tool and they are for sure plenty of way to use it for malicious purposes. So, how to protect you? There is no all-in-one solution. To protect yourself, you must review GPO’s in place, limit admin privileges, monitor the activity on the network and, of course, keep your environment healthy.
Then, Clarence Chio came to present “Machine Duping – Pwning Deep Learning Systemsâ€. Machine learning, or deep learning, or “artificial intelligence” refers to computers which can take decisions by themselves (to briefly resume). The idea of Clarence was to search for a way to pwn them, read: to make them take wrong decisions. As such kind of computer will be more and more used, it is interesting to see how they can be abused.
The presentation explained in details how those computers can be abuse but it was purely theoretical (too much) for me. Clarence looks to really master his topic!
After the second coffee break of the day, the last wave of talks started… Four in a row! That was quite intensive… Matt Weeks came to present “Credential Assessment: Mapping Privilege Escalation at Scale“. Matt demonstrated that in major breaches, often the complete network is compromised, data are stolen. He reviewed some nice stories like Target, Home Depot of JP Morgan Chase. Sometimes the attack is more destructive like Sony or TV5-Monde. Usually, a data breach is based on multiple techniques: social engineering, modification of a malware to evade controls in place, etc.
What do they have in common? Credentials were (ab)used to gain access to the infrastructure. In a second part, Matt explained how to protect credentials to not be used in such attacks. But, this must be combined with other security controls. Lessons learned demonstrate that often:
- The corporate network was open to contractors
- There was no response from anti-intrusions or monitoring tools in place
- There is a lack of network segmentation
Matt explained how to track credentials and how to enforce security controls. What must be performed:
- Identification of credentials dissemination
- Identity reused
- Identify impact of credentials
It is mandatory to determine mechanisms to break the chains and to clean up credentials. Data must be collected as much as possible with privileges assignments, group membership, etc.
The next slot was assigned to two guys from Checkpoint (Yaniv Balmas & Ben Herzog). They presented “When crypto fails†or “Finding cryptographic bugs for mere mortalsâ€. Checkpoint guys are also regular speakers at hack.lu. Crypto is everywhere and more and more malware implement cryptography today. They are right when they say that cryptographic bugs are not in the crypto algorithm but un the way the developer implements it. Sometimes, a bug can be found in the crypto library. In this case, they recommend to disclose it privately.
After this introduction, the second part of the talk was a review of different badly implemented crypto in pieces of malware. The first one as Zeus, the well-known banking malware. Many malware use RC4. It is very popular, not complex and easy to implement. But… why do the Zeus developers decided to implement their own algorithm, called ZRC4? They called this example: Voodoo programming.
The next example was based on Linux.Encoder which was one of the first ransomware targeting Linux hosts. It uses PolarSSL\mbed-TLS libs for encryption tasks. To provide randomness, it uses the following code to encrypt files: SRAND(time(NULL)). What’s bad: encrypted files were created with a new timestamp, so they were easy to decrypt. Keep in ming that when you use time-based seed, the time can be used again to decrypt. The last one was Petya, the ransomware which encrypts also the MBR and finally the Nuclear Exploit Kit.
SRAND(time(NULL))
What’s bad: encrypted files were created with a new timestamp, so they were easy to decrypt. Keep in ming that when you use time-based seed, the time can be used again to decrypt. The last one was Petya, the ransomware which encrypts also the MBR and finally the Nuclear Exploit Kit.
The next talk was presented by Jacob Torrey: Bootstrapping an architectural research platform in 60 mins. I bypassed this one…
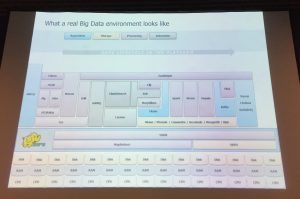
The day ended with a presented about Hadoop, the tool developed by Apache. Here again, the title of the presentation induces a false idea. The presentation was about abusing Hadoop. After an introduction to Hadoop and its infrastructure (which is quite complex), Thomas & Madhi explained how the framework is badly configured (by default).
Then, they reviewed the Hadoop security model which is very “open”. By default, there is no authentication: “simple” means none but there is an alternative based on Kerberos. About authorization and auditing: all components implement their own model. This make it very complex to maintain. Data encryption is available but, here again, disabled by default. If you try to build an attack surface of an Hadoop instance, you will see that many TCP ports are used! The rest of the presentation was based on demonstrations that prove that the security model is by default inexistent! More scary, there are Hadoop instance available publicly available. IMHO, the conclusion to this talk is: Hadoop is a mess!
That’s it for today! Same place for the third wrap-up tomorrow…








RT @xme: [/dev/random] Hack.lu 2016 Wrap-Up Day #2 https://t.co/H1ioJzXe1k
RT @xme: [/dev/random] Hack.lu 2016 Wrap-Up Day #2 https://t.co/H1ioJzXe1k
RT @xme: [/dev/random] Hack.lu 2016 Wrap-Up Day #2 https://t.co/H1ioJzXe1k
RT @xme: [/dev/random] Hack.lu 2016 Wrap-Up Day #2 https://t.co/H1ioJzXe1k