I’m back to Luxembourg for a new edition of hack.lu. In fact, I arrived yesterday afternoon to attend the MISP summit. It was a good opportunity to meet MISP users and to get fresh news about the project. This first official day started later and in a classic way: with a keynote. The slot was assigned to Alice Hutchings and was named: “Stressed out? Denial of service attacks from the providers’ perspectiveâ€.
Alice is working for the Cambridge Cybercrime Center Computer Laboratory. The keynote title did not reflect the exact content of the keynote. It was not covering the DDoS aspect from an “Internet providers” point of view but from the DDoS services providers, read: the bad guys. The idea of the keynote was “know your enemy!“.
Alice started with an example of a website providing DDoS services to anybody. A nice look, support, description of the different types of supported attacks, the different membership plans. Looks very professional. Those guys are called “booters“. The Alice’s research was to study who they are, how they work. She started with cybercrime trajectories: the theory of initiation, maintenance and desistance. First of all, they are techies who know how to attack, how to abuse. It starts always with opportunities. Two pathway:
- The general pathway: Â the initiation goes from strain to presented opportunity
- The Technical pathway: the initiation goes from associations with others to learn skills and neutralisations
For both, the maintenance is mainly low likelihood detection and benefits relating to offending. Finally, the desistance is when costs outweigh benefits
The biggest part of the study was to organize an online survey. Once a list of booters was identified, she sent invitation request and, first surprise, 25% of them responded (positively as well as negatively). Two of them even accepted an interview. Based on the information gathered, what she learned from the respondents? They are often young and are active from a few months up to a few years. And, what a surprise, their main motivation is to make easy money. Alice release all details of her research in a document called “Exploring the provision of online booter services” (available here). An interesting fact: those guys do not realize that they provide illegal services. For them, it is a normal business.
Then, a first set of lightning talks was organized. Amongst other, I noted:
- A cool demo of Metabrik (they will be the topic of a talk tomorrow)
- A very nice exploitation (RCE, XSS) of a Kerio UTM appliance (“when your firewall turns against youâ€)
After the lunch, the regular talks started again with “Exploiting and Attacking Seismological Networks… Remotely†by James Jara. Why seismological devices? Because it’s not a juicy target for most people and it may be an idea for cool scenarios. Indeed such devices are not only used to detect earthquake but also by oil & gas companies to find new sources of combustible.
Like for other devices, they are different vendors, Nanometrics being the biggest one. The devices are Linux based, provide remote management facilities (SSH, Telnet, FTP), a web server, GPS chop, good batteries or solar panels. Of course, they are connected to the Internet to be able to send collected data to seismologic centers. James explained how he found devices. Â Via netdb.io, a site similar to shodan.io but more focusing on IoT devices. A nice story, to get a copy of the firmware, he just sent a mail to the manufacturer askin politely a copy… and he received one! Everybody know that once you get a copy of the firmware, the most difficult step is completed. It’s then easy to analyze it to extract keys, passwords,e etc. James performed lot of demos (some recorded, some live – which is, IMHO, a little bit borderline). Nice research but the audience was not the right one. The vulnerabilities found are the same as any other IoT device. It would be interesting to present the same research to scientific people!
The next talk was “Secrets in Soft Token – A security study of HID global soft token” by Mouad Abouhali.It was a nice research about a specific 2FA implementation based on the HID soft token app. He started with a review of a classic 2FA implementation. Today, many solutions can be installed on smartphones. We don’t need hardware tokens which are difficult to manage/deploy and expensive. If the HID solution is available on multiple mobile operating systems, the research focuses on the Android version. The idea was to analyze what may happen when a device is stolen, how the application is protecting itself, how data is stored and how cryptographic features are implemented. If the application looks quite well protected (code is obfuscated, it does not run in a jailbroken environment), the code was successfully analyzed by Mouad’s team: they read the code, debugged it and rebuilt it. They also analyzed the behaviour to generate logs and analyze them.
The next step was to understand the encryption tasks. Where is stored the PIN? A first vulnerability was discovered: it is possible to clone the application by copying the HID config files and to gather the Android_id secure attribute. But the attacker still needs the user’s PIN code (that can be collected using social engineering techniques). The second vulnerability was to discover the PIN. The develop a tool to do this and it seems to be quite useful. Mouad explained in details how it works. That was a great research performed in one month. They reported the findings to the vendor which is busy with a new design of its application.
Then, “KillTheHashes, 30 million malware DNA profiling exercise” was presented by Luciano Martins, Rodrigo Cetera & Javier Bassi. It started with a fact: Today, the identification of a piece of malware only with its hash is a fail.
Luciano gave several examples of well-known malware (Stuxnet, Zeus, Dino). All of them have specific characteristics like a file name, a system call, a DLL name. The idea behind this talk is to classify the malware based on this information. To achieve this, a tool was developed which provides:
- A DNA profiling search engine that discovers malware patterns and characteristics.
- File type search capabilities
- A framework to search malware
- Large scale malware analytics
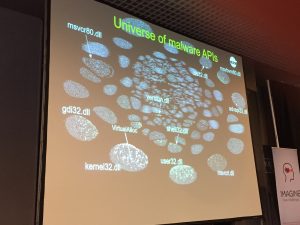
Another example, most popular malware code sections are the TSULoader, NullSoft PiMP stub or the 7zip extractor. They can also be used to identify malware samples. Based on this, the malware universe map was created:
The tool is called CodexGigas and is available here. This is definitively something that you have to test if you’re dealing with many malware samples.
After a well-deserved coffee break, Wayne Huang & Sun Huang presented their analyze of a malware campaign: “Unveiling the attack chain of Russian-speaking cybercriminals“. The botnet is called Asprox and is online since 2007. It targets Windows and Android devices (since 2014). Being operated by Russian speaking guys, it is delivered via classic spam emails. If the delivery is classic, some interesting checks and features are implemented like a delivery testing (they verify the domain reputation via online services like scan4you.org or avdetect.com). Waves of spam are also scheduled by geographic areas. The attack chain is classic:
Victim > Compromised Server > TDS Server > Botnet > NGinx Reverse-Proxy > C2 > Attacker
The explained in details how the botnet works, what are the techniques used to defeat the security researchers’ job but also the business around the botnet. Some techniques to make the analyst’s life more difficult are really evil. Example with the NGinx reverse proxy: the configuration with C2’s IP addresses is generated, the proxy started and the config immediately deleted and replace by a fake one.
The next speaker was Matthias Deeg with a talk called “Of Mice and Keyboards: On the Security of Modern Wireless Desktop Sets”.
His talk focussed on remote keyboards and mouses (using RF to communicate with a USB dongle). After a short introduction to the technology used and how it works, Matthias explained the goal of his research. There was already papers and presentation on the same topic but he focused on multiple device vendors (Cherry, Microsoft, Logitech & Fujitsu). The methodology was a classic approach: open the device, identify the chops, read (a lot of) documentation and write some code. The nRF24 looks to be the most popular one. The different exploited scenarios were:
- Physical attack: extract the firmware, change the firmware, extract crypto material and manipulate it
- Use radio signals: exploit open radio comms
- Replay attacks
- Keystroke attacks
- To try to decrypt comms
Matthias made some nice demos: abuse a wireless mouse to launch a virtual keyboard and type some text. The replay attack simply unlocked a Windows desktop by replaying the user’s password. The best one was the injection attack: a Powershell payload can be injected and executed! Nice demo but we already know that such devices provide a low level of security.
Paul Rascagnères explained how Microsoft implemented code signing protection but also how to bypass it. A small reminder about Authenticode: it was developed by M$, based on certificates. Kernel drivers must be signed since Win7 64bits. Really?
Paul explained several ways to bypass this protection: low cost and high end. The low cost is based on the bcdedit.exe command that can be used to switch the system to test mode :
bcdedit.exe -set TESTSIGNING ON
If a message is displayed by winlogin.exe, it can be removed by patching the process in memory to NOT display this info on the screen. The other technique (used by Uboruros) is based on CVE-2008-3431. Via VBoxDrv.sys, no message is displayed but it can be detected using bcdedit.exe. Other techniques explained by Paul were exploited by the malware Derusbi, GrayFish and HIDEDRV.
The last talk was presented by Kevin Borgolte about Shellphish and the DARPA Cyber Grand Challenge. The idea behind this project is to organize a CTF game (“Capture the Flag”) but instead of human players, computers are playing between and try to exploit each others and to protect themselves in an automated way. Kevin explained in details how it works but it was way too complex to get the point. Just visit the website if you’re interested in this topic or watch the video.
That’s all for the first day! Note that talks are recorded and videos posted very quickly after the presentation. The Youtube channel is here. Stay tuned for the second wrap-up by tomorrow!






RT @xme: [/dev/random] Hack.lu 2016 Wrap-Up Day #1 https://t.co/r1iTQjBYQA
RT @xme: [/dev/random] Hack.lu 2016 Wrap-Up Day #1 https://t.co/r1iTQjBYQA
RT @xme: [/dev/random] Hack.lu 2016 Wrap-Up Day #1 https://t.co/r1iTQjBYQA
RT @xme: [/dev/random] Hack.lu 2016 Wrap-Up Day #1 https://t.co/r1iTQjBYQA
RT @xme: [/dev/random] Hack.lu 2016 Wrap-Up Day #1 https://t.co/r1iTQjBYQA
RT @xme: [/dev/random] Hack.lu 2016 Wrap-Up Day #1 https://t.co/r1iTQjBYQA
RT @xme: [/dev/random] Hack.lu 2016 Wrap-Up Day #1 https://t.co/r1iTQjBYQA
RT @xme: [/dev/random] Hack.lu 2016 Wrap-Up Day #1 https://t.co/r1iTQjBYQA
RT @xme: [/dev/random] Hack.lu 2016 Wrap-Up Day #1 https://t.co/r1iTQjBYQA