 This is my first Troopers conference. I already heard lot of positive comments about this event but I never attended it. As I’ll start a new job position soon, I had the opportunity to take some days off to join Heidelberg in Germany. The conference is split across two days and three tracks: “attack & researchâ€, “defence & management” and a special one dedicated to the security of SAP. Honestly, I’m not working with SAP environments so I decided to not follow the last track. The core organizer, Enno Rey, made a funny introduction speech and gave some numbers about the 2015 edition: 73 speakers, 160 people from the industry and 51 students (fresh blood). A key message for the conference is to not see speakers as super-stars. Don’t be afraid to talk to them and share!
This is my first Troopers conference. I already heard lot of positive comments about this event but I never attended it. As I’ll start a new job position soon, I had the opportunity to take some days off to join Heidelberg in Germany. The conference is split across two days and three tracks: “attack & researchâ€, “defence & management” and a special one dedicated to the security of SAP. Honestly, I’m not working with SAP environments so I decided to not follow the last track. The core organizer, Enno Rey, made a funny introduction speech and gave some numbers about the 2015 edition: 73 speakers, 160 people from the industry and 51 students (fresh blood). A key message for the conference is to not see speakers as super-stars. Don’t be afraid to talk to them and share!
The first day started classically with a keynote presented by Haroon Meer, the founder of Thinkst, an applied research company with a deep focus on information security. The title was “The hard thing about the hard thingâ€.
It’s a fact: Doing security is pretty hard. Harmon cited a tweet: “If our industry is so broken, why don’t you leave and become a truck driverâ€. For him, (un)fortunately, we don’t have to convince people anymore that security is important. We have to focus on the bug problem and not on secure engineering. Another interesting quote was: “We don’t have a malware problem, we have an adversary problemâ€. Harmon reviewed three key components which directly affect security:
- Software complexity
- People
- Market
What about complexity? Networks of the future (today?) will become complex and complex and difficult to manage from a security point of view. As an example, Haroon cited the Linux kernel and the Chrome browser. The code is maintained by thousands of developers and has millions of code. Think about this when you just browser a website! It became so complex that sometimes we loose the control and how to protect something that we don’t understand? In a composite system, there is no critical gate, everything is a gate. We are bad at writing safe code. Microsoft spent millions of dollars to improve code for years and today IE still suffers of many vulnerabilities (in the last Microsoft security bulletin of February 2015, many patches were released for Internet Explorer!). Shellshock is a very example of composite system. Another example: the black phone. Mark Dowd found a bug in the messaging application. Based on software quality checks, we better defend our network with PowerPoint than with a CheckPoint firewall (quote from FX). The market is also a source of problems. Incentives are part of the business failure. Managers get promoted by shipping new software all the time. Check out how many operating systems and versions you used since you’re working with computers. Even if some companies suffered of giant breaches, this did not affect their value or their customers. In organisations, it’s difficult to evaluate risks. To correctly evaluate them, you must know what can happen. Not easy! Remember: “You can’t buy security!â€. Haroon gave many other examples which prove that we are at an inflection point with hard problems to be solved. A very nice keynote!
For the first talk, my choice was to follow Arrigo Triulzi who presented “Pneumonia, Shardan, Antibiotics and Nasty MOVs: a dead hand’s taleâ€. A curious title! Arrigo was not able to travel from Switzerland to Heidelberg and gave his presentation via a Webex. From a technical point of view, it was perfect, I must confess that it’s not the same as seeing the speaker in real life even if Arrigo started with a joke: “I’m not a Snowdenâ€.
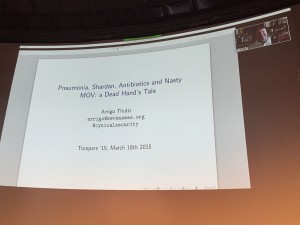
The talk started with a review of all technologies used during the cold war with nuclear weapons. For a long time, attackers use the “decapitation attack†to take out the C&C. To avoid this, defenders developed countermeasures to not loose the control if the C&C is compromized. As analogy with the infosec field, Arrigo explained that a SOC in a big company may become blind of the deployed sensors are killed. Back to the modern world, Arrigo explained how he successfully changed the microcode of processors. The biggest issue was the persistence. If the CPU is power cycled, the changes are gone. To prevent this, he explained step by step how he added persistence using, i.e. nicssh, another project used to run a SSH daemon in a NIC firmware. If the idea of the talk was interesting, I had some difficulties to follow Arrigo’s ideas, maybe due to the webex?
Then, I switched to the second track with “Game over, does the CISO get an extra life?†presented by Richard Rushing, CISO of Motorola Mobility. The Richard’s idea was interesting: He compared the daily life of a CISO to a modern online game. He started with some facts called “Security campingâ€;
- We focus on something so closely we miss everything else
- We need an IR process
- Data center
- Perimeter focus
- You cannot see it coming
- You have to time to react

A game focuses is on the player, but security focus is on the attack surface. Think about the “shark in the water†: never use terms like “theoreticalâ€. A good quote: “What is the difference between theoretical and practical? A few lines of code!â€. The next comparison was based on grinding or farming: What we do, what we hate in our job. Automatisation is good but we can’t buy a solution. According to Richard, we must build it because all structures are different. Then came the lagging… So important in games but also in security. People also lag. Keep in mind that we can get pwned by a 10y-old kid. We need good IR process, vulnerability reports. The time is critical! The next analogy with games was the multi-players aspect. Security is a team sport. Everybody listens and comments. Especially if you have processed like incident response. Bring people that can make decisions. What about “power levellingâ€? Use known strategies to level faster, learn from friends, strangers and old-guys? What about newbies or noobs in security? Use them even if it is for cannon fodder. Like games, security can have glitches: we need patches. And Richard gave more examples. IOC’s can be compared to easter-eggs in software (hidden messages). And what about the final boss in games? The problem with security is that it’s a never over game. A good talk with nice analogies to the gaming world.
After a lunch break, I moved back to the attack and defence side. Michael Ossmann presented “RF Retroreflectors, Emission Security and SDRâ€. This was the best talk of the day IMHO. The goal was to explain then demonstrate a retroreflector attack. The principle is based on an attacker -> target -> implant -> radar. It really acts like a classic radar, listening for returned data.

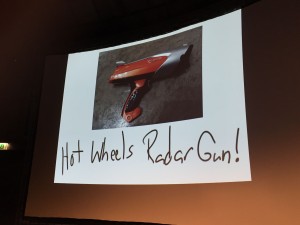
In such attack, the implant is very important. Note that attackers can also benefit from unintentional emissions like screens. The first implant in the history was the “thing†(The great seal bug). It was very simple, required no battery, can run for years and very difficult to detect. Between the Thing and the ANT catalog, 53 years… What happened during this period? There is no real study, only rumors and speculations. So, to listen to the data returned by the implant, you need a “radarâ€. Michael started to play with old police radar but it was not very effective. Later he found a game radar from Hotwheels which was good enough.
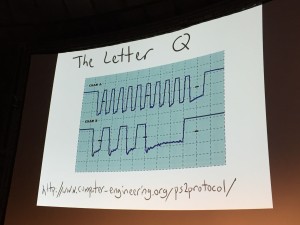
He explained the lab that he deployed, based on two HackRFOne, one for emitting and one for reception data). They act as a sound card using a microphone and speakers. Instead of classic antennas, Michael used coffee cans. The implant he developed was very simple and called the “Congaflockâ€. If this one is easy to hide into a cable or a keyboard, he quickly developed a new mode with PS/2 connector (more convenient). He made a live demo and captured some key press on the keyboard.
The next device which was presented is the “Salsaflock†which listen for VGA signals. Michael explained how screenshots can be captured using… The Gimp!
More details are available here.
Then Gabriel Barbosa and Rodrigo Branco talked about “Modern platform-supported rootkitsâ€. Why this talk? They are working at Intel and they had to follow mandatory trainings. But they had ideas to attack systems in different ways.

This talk was the result to their research. The biggest problem is assumption. People assume that a system behaves in a specific way. This is wrong! It is programmed to behave like this. A malware will change the way a system works.The current challenges for modern rootlets are: OS dependency, security mechanisms and the different model of computers. Gabriel and Rodrigo reviewed many examples of system abuse. It was really technical and hard to follow for me.
After the afternoon coffee break, “Defender Economics†was presented by Andreas Lindh. The goal of this talk was to understand attackers, their capabilities and their constraints. Yes, they also have constraints! Because if was a defensive talk, the goal was to use this to improve our defences. Two facts: An attacker only need to find one way to hit his target.  But a skilled and motivated attacker will always find a way.
We must keep in mind that attackers are evolving and we can’t protect against everything. A good point is that attackers don’t have unlimited resources. Do you really need to protect against everything? Not sure. Attackers also have bosses and budgets. They also use basic maths: if the cost of an attack is less than the value of the information to attack, go for it!. The attacker’s economics are:
- Attacks must have an economic sense
- Attackers use available resources
- The attack must be kept into the budget
And for the defenders:
- Know the attackers limitations
- Break the attacker’s budget
Attackers can be profiles. What are their motivations, resources and procedures? Motivation behind the attack and level of motivation per tatted. What about resources? People and skills, tools and infrastructure or the supply chain. Regarding the procedures, what are the attack vectors, post exploitation activities and flexibility. Andreas explained this by comparing two scenarios:
- The Google Chrome browser and classic malwares
- A big company X targeted by an APT (buzzword)
The company X has multiple solutions to reduce the risks:
- Cheap but effective: exploit mitigation / secure software mitigation (example by installing EMET on all computers)
- Expensive and effective: 3rd party sandbox
- Very expensive and possibly effective: email security product
Keep in mind that we do not fight the armor but the man inside. Security is hard but:
- Attackers have limitations
- Attackers are not made of magic
- Understanding these limitations is the key to make good defensive decisions
- Raising the cost of an attack can be very effective
- This is not to be 100% secure
The day ended with some lightning talks. I really liked the one about virtual machine introspection & DRAKVUF. This is a dynamic malware analysis system which does not work as the other ones. Why focus on WMI? In-guest agents are easy to detect and vulnerable to rootkits. So, we need to move the security outside the VM. Quick presentation of a nice tool to perform malware analysis. Have a look at it.
The first day was closed with the social event in a typical German restaurant. As usual, good food, beers and very interesting chats. For a first day, I’m really happy with the organization: nice venue, stable WiFi, SIM card available with a dedicated mobile network (I did not trust it ;-), good food, lot of Club-Mate. I’m looking forward the second day!

RT @xme: [/dev/random] #Troopers15 Wrap-Up Day #1 http://t.co/faiIOqk8ck
RT @xme: [/dev/random] #Troopers15 Wrap-Up Day #1 http://t.co/faiIOqk8ck
RT @xme: [/dev/random] #Troopers15 Wrap-Up Day #1 http://t.co/faiIOqk8ck
RT @xme: [/dev/random] #Troopers15 Wrap-Up Day #1 http://t.co/faiIOqk8ck
RT @xme: [/dev/random] #Troopers15 Wrap-Up Day #1 http://t.co/faiIOqk8ck
RT @xme: [/dev/random] #Troopers15 Wrap-Up Day #1 http://t.co/faiIOqk8ck
RT @xme: [/dev/random] #Troopers15 Wrap-Up Day #1 http://t.co/faiIOqk8ck
RT @xme: [/dev/random] #Troopers15 Wrap-Up Day #1 http://t.co/faiIOqk8ck
RT @xme: [/dev/random] #Troopers15 Wrap-Up Day #1 http://t.co/faiIOqk8ck
RT @xme: [/dev/random] #Troopers15 Wrap-Up Day #1 http://t.co/faiIOqk8ck