 This is already the last day! We started again at 08:30 with a talk about IP cameras: “Do you know who’s watching you? An in-depth examination of IP cameras attack surface” by Francisco Falcon & Nahuel Riva. This isn’t the first time that IP cameras are used as targets for a talk. What was the motivation for this presentation? Found vulnerabilities in small cameras used everywhere (like at home for surveillance)! The goal was to: understand, find bugs, use the cam as an attacking device, modify the stream. First some general information about those gadgets: most of them have the same features: motion detection, night vision, two way audio, alarm connector, alerting. They run a webserer, a RTSP and UPnP servers. As most embedded devices, IP cams have a serial console. To access it, use a Bus Pirate with the UART chip and you are good to go. Then, Francisco & Nahuel reviewed some cameras available on the home market. The first target was a low-cost IP cam made in China (MayGION). Discovered vulnerabilities were:
This is already the last day! We started again at 08:30 with a talk about IP cameras: “Do you know who’s watching you? An in-depth examination of IP cameras attack surface” by Francisco Falcon & Nahuel Riva. This isn’t the first time that IP cameras are used as targets for a talk. What was the motivation for this presentation? Found vulnerabilities in small cameras used everywhere (like at home for surveillance)! The goal was to: understand, find bugs, use the cam as an attacking device, modify the stream. First some general information about those gadgets: most of them have the same features: motion detection, night vision, two way audio, alarm connector, alerting. They run a webserer, a RTSP and UPnP servers. As most embedded devices, IP cams have a serial console. To access it, use a Bus Pirate with the UART chip and you are good to go. Then, Francisco & Nahuel reviewed some cameras available on the home market. The first target was a low-cost IP cam made in China (MayGION). Discovered vulnerabilities were:
- FTP with hardcoded credentials
- Buffer overflow
- Path traversal
Then, a Foscam model was reviewed. Same status: pwn3d! This cam has default credentials: “admin/<empty>”. With a simple HTTP request (GET /get_status.cgi), you have access to technical info. Another request (GET /../../../../../proc/kcore) gave access to the cam memory. The following was a D-Link DCS IP cam with hardcoded telnet credentials (root/admin) and a RTSP server running by default without authentication, just use your VNC client to see the live stream. Then the speakers explained how to get full access to the cam using different methods. The Zavio cam was the next to be analyzed. It uses a specific authentication mechanism which was also broken. This cam has a backdoor that cannot be disabled! Two CGIs can be accessed using hardcoded credentials (used for factory testing). Command injection was also found and easy to get access to /var/www/secret.passwd. Next victim? A TP-Link IP cam. This one as a backdoor (manufacturer:rerutcafunam). At least, developers at TP-Link are more inventive. For this cam, they successfully build their own custom firmware.
After owning a device, the next step is post-exploitation! On the Foscam camera, they backdoored the web server (check_user2_cgi) and added  a system() call in the authentication code to execute any command passed to the CGI. What else? Netcat to the rescue to get a reverse shell. Keep in mind that in your camera, we can see your  access-points, search for credentials (MSN, FTP, SMTP, SMP, PPPoE, etc). Your IP cam knows a lot about you. The next post-exploitation example was to pivot through the camera. Awesome!
Finally, a demo of video stream hijacking… The speakers  explained in details how it was possible to replace the video stream with some images played in a loop. To achieve this they built a custom firmware. Once uploaded the live stream is replaced! What are the conclusion? “ALL IP cameras are broken!“. Don’t expose them (just have a look at shoran for curiosity), keep the firmware updated. Some vendors did even not responded to the vulnerability reports! More information about this research is available here.
Then Dominique Bongard presented his research: “Deanonymazing members of French political forums by breaking gravatar hashes“. The title of this talk looked interesting, I was curious.. It was not very technical but with more focus on privacy risks (Isn’t it a hot topic in those days?). Gravatar is “a service which allows members of forums and blogs to automatically have the same profile on all sites“. Do you know that it uses the MD5 hash of the email address to identify a person. It’s very easy to create your Gravatar with a few clicks. Then your avatar is displayed via a link to Gravatar like “http://l.gravatar.com/avatar/<md5>?size=xxx“.Note that MD5 hashes are also displayed for users who didn’t register with Gravatar!
What about privacy? You can discover people email’s addresses. Generate MD5 hashes from addresses and lookup for them to verify them. It’s like cracking a password like hashcat! In 2008, 10% of email addresses from stackoverflow.com users where retrieved! The response of Gravatar was just to say that email addresses are not private.
Now a practical example with the political context in France… In France, no right to free speech and forum posters can be sued. So, is it possible to de-anonymize members of political forum? Dominique performed test with a famous French forum: fdesouche.com. The process was to crawl MD5 hashes (he collected 2400 of them) then crack them like password cracking. To achieve this successfully, it is mandatory to use good dictionaries. He built one based on:
- The user nicknames,
- FR & UK first and last names
- FR & UK words
- Wikipedia entries
- Sport teams,
- Numbers
- Current year, & zip codes.
He successfully found 20% of emails. oclHashCat was limited to 15 chars, with the latest version, it was possible to crack up to 45% of them. But there was still limitation and Dominique wrote his own tool. Some stats:
- gmail is top one domain
- 20% use probably their own name
- 10% use username
- 30% use numbers
- 20% contain a dot
- 5% contain underscore
Those stats are very interesting to optimise dictionaries (like cracking passwords)! Note that many people use disposable email providers to register on forums. This leverage a new type of attack: By disclosing the disposable email address, you can trigger a reset password function on a blog or forum and receive the mail via the mail service website, indeed, no password is required to access the temporary mailbox.
After a welcomed caffeine-refill break, Sebastien Larinier & Guillaume Arcas spoke about their framework “Exploit Krawler” or “Seeking exploit kits at large scale make easy“. They are many exploit kits delivered via websites today, some of them became famous names like “BlackHole“. To be able to fight against them, it is necessary to know them (“Know your enemy“) but it requires lot of resources and time. The goal of this project was:
- To discover similarities in exploit kits
- To understand URLs diffusion methods
- To understand targets selection
- To understand obfuscation methods
- To identifying authors?
- Find malicious URLs (not the most difficult part 😉
- Browse the pages with vulnerable browsers
- Avoid failures
- Extract relevant information
eBanking became a common application for most people on the Internet. In countries like Belgium, more and more people do “Internet banking”. Adrian Furtuna presented his research called “Practical exploitation of rounding vulnerabilities in Interner banking applications“. This is a talk that was presented at Hack In Paris 2013, see my previous wrap-up here.
After a lunch break, the second session of lightning talks was organised. The first one was about SCADA with “SCADAVIRT” a lab based on an hynesim:
The second lightning talk was presented by the Dutch CERT about “Responsible Disclosure” or “I want to report a vulnerability“. Not always easy… Hackers and organisations are like dogs & cats. A project from the CIRCL was presented: PCAPDJ, to merge/process pcap-ng files without storing them. Another one about pwning McAfee ePo, check out funoverip.net for more details (this research will be presented at the OWASP Benelux Days in a few weeks). The next one was a technique to detecting XORed binary in Suricata in LUA. Finally, “Pcap2Bubbles” is a project to visualise pcap files. Originally performed with Afterglow, the project switched to D3.js and Malcom. Nice tool!
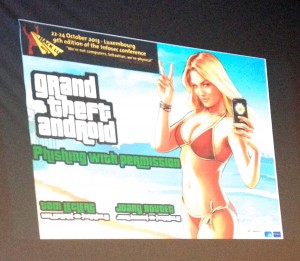
After this set of awesome of lightning talks, the floor was given to Axelle Apvrille who presented “Playing hide and seek with Dalvik executables“. There was already a talk related to Dalvik the first day as mobile malwares remain a hot topic. Inside APK files, we have DEX – “Dalvik Executables” – files. And inside the DEX? We found classic program stuff like classes, fields, strings, methods etc. This is the topic of Axelle’s talk. The first part focused on how to hide a method? Axelle demonstrated her tool to patch a DEX file and hide a particular method (Demos available online). The second part of the talk was, logically, how to call those hidden methods? So what? Hidding code is used to hide some malicious code. How to detect it? There are two ways: strings are not hidden and the byte code is always there. The last demo demonstrated how to find interesting strings and how to decode malicious bytecode starting at  a certain address.Luckily,Axelle did not find this method in a malware right now… Regaluar malwares remain simple. Example: sending a SMS to a premium number requirres only a few lines of code. The question is: Until when?
Philippe Teuwen also presented a talk related to eBanking: “Unveiling online banking authentication devices“. Digipass used for bank operations have two buttons labelled “M1” and “M2” (like in Belgium). “M1” is used to authenticate and “M2” is used for transaction signature. How to learn what’s inside the small box? Google returned nothing relevant. Philippe found a documentation. Another group of researchers found how work the “M1” function. If you can’t find how it works via the classic (soft) way, use the hard way… Use the card interface, UART based but only 1 I/O pin and arbitrary baud rate. A Bus Pirate was a good solution (for the 2nd time today!). As a result, it was possible to emulate the “M1” function of the Digipass. Of course, the next step was to emulate the “M2” function. Some stange stuff was detected in communication between the card and the reader. A control over cryptogram was needed. Java Card applet was used in this case. What’s next? Philippe wrote a Digipass emulator script in Python. So, based on Adrian’s talk, what’s the best solution? Hardware or software? Interested? More resources are available here.
Finally, Shift closed the schedule with “Interactive Deobfuscation“. A very very technical session… It should be very interesting but slides full of assembler code and math formulas… I was lost! 😉 Anyway, kudos to the speaker for his first presentation at a security conference. Good job! This wrap-up closes the 9th edition of hack.lu. I spoke to the team and they will prepare us awesome stuffs for the 10th edition! Book already the same period in one year. By the way, the two pictures below are a good proof that devices must be properly protected! They have been taken in the hotel lobby:



RT @xme: [/dev/random] Hack.lu 2013 Wrap-Up Day #3 http://t.co/r2ysbQjaR5 #hacklu
RT @xme: [/dev/random] Hack.lu 2013 Wrap-Up Day #3 http://t.co/r2ysbQjaR5 #hacklu
RT @xme: [/dev/random] Hack.lu 2013 Wrap-Up Day #3 http://t.co/r2ysbQjaR5 #hacklu
RT @xme: [/dev/random] Hack.lu 2013 Wrap-Up Day #3 http://t.co/r2ysbQjaR5 #hacklu
RT @xme: [/dev/random] Hack.lu 2013 Wrap-Up Day #3 http://t.co/r2ysbQjaR5 #hacklu
RT @xme: [/dev/random] Hack.lu 2013 Wrap-Up Day #3 http://t.co/r2ysbQjaR5 #hacklu
RT @xme: [/dev/random] Hack.lu 2013 Wrap-Up Day #3 http://t.co/r2ysbQjaR5 #hacklu