 I’m in London for the next three days to follow the RSA Conference Europe 2012. This is my third edition and I would like to thank the organizers for the received press pass which allows me to write this wrap up! (and the next ones in the coming days). Compared to security conferences like Defcon, Hashdays or BruCON, this event tries to mix the business guys with the techies which is, honestly, not always easy!
I’m in London for the next three days to follow the RSA Conference Europe 2012. This is my third edition and I would like to thank the organizers for the received press pass which allows me to write this wrap up! (and the next ones in the coming days). Compared to security conferences like Defcon, Hashdays or BruCON, this event tries to mix the business guys with the techies which is, honestly, not always easy!
During the first half-day, keynotes are presented by speakers working for the main sponsors: RSA, Symantec and Microsoft.
Art Coviello (RSA/EMC) opened the conference with his keynote about a new security model based on intelligence-driven security. With the new threats as well as new technologies, Art sad that it’s time to re-think the way we do security. Today, security is based on 80% prevention, 15% detection and monitoring, 5% response. This balance must shift. What about “awareness“? We have too much awareness (about information security) but what about the understanding or the context? There is a serious gap between the perception and the reality. According to Art, they are four levels of cyber maturity: control, compliance, IT risks and business risks.
The second keynote speaker was Tom Heiser (also from RSA). His keynote was a continuation of the previous one: What about the actions? First, move to a risk based security must be reconsidered. Then, re-think detection strategies and deploy continuous monitoring. Three, harden the authentication and finally, educate, educate and … educate! Users are often weak and are compromised but they can also play the role of an extra defence layer if properly educated.
Francis de Souza (Symantec) shared some researches made by Symantec about the threats landscape. What a cyber-attack looks today? Data-centers become bigger and bigger (with lot of storage, servers, hypervisors) but we have less control of the infrastructure as before. The security model has to change. Which security model? It’s impossible to win a battle by doing defence only. From a decade, we looked at specific attack: You got a virus? Install an anti-virus! But think globally, think about the entire campaign (the “multi-flank attack“). As an example, DDoS attacks are used to obfuscate the real attack. Focus on below the radar activity. We have lot of tools but we still have a feeling of being insecure. It’s important to understand the complete campaign and not focus on the results. What to look for? Focus on your data & assets. 10% or less of the information in an organisation is really important (why protect spam, newsletters, multiple copies of PPT?) Think about “intelligence“: What’s the campain running against us? “Know yourself” (agility) As example of unexpected situation: VMotion moves a critical app to a non-hardened server. Finally: the power! It does not care if your AV is good or bad. Custom malware is written for you. => use reputation. Ask the question to yourself: “Did we see this file already?“
Adrienne Hall (Microsoft) talked about the risks and rewards of cloud adoption? What does Microsoft propose to fight new threats? the Security Intelligence Report version 13 was relaeased today? From this report, we see that that HTML/Java is today 70% of top exploits families. Microsoft also offers free tools: Attack Surface Analyzer, Anti-Cross Site Scripting Library and EMET (Enhanced Mitigation Experience Toolkit). Those are available here: aka.ms/securitytools. Then Adrienne talked about the ongoing survey started by Microsoft about the cloud adoption.
To close the keynote sessions, Hugh Thompson (Program committee RSA conference) made show as usual. This is really a fabulous speaker! Again, he started his keynote with a personal story. Then he discussed about the different types of users. Nobody addresses security in the same way. People have different views of security! Â Going to several steps before making a choice (ex: certificate issue on a website). Users have different approaches to risk; security needs to take user differences into account. Knowability: the death of first impression. Goal of the conference: change the perception you have of security?
What to say about those keynotes? Well, first they are reserved to main sponsors. They present their visions of the security business (yes: they make business with security). Nothing brand new was revealed. For me the best speaker was, of course, Hugh Thompson. But a special mention to Francis de Souza who did not presented a brand new content but it was performed in a very nice way.
After the lunch, the track sessions started. Each track is composed of multiple sessions organised in big topic like “Development“, “Data Security“, “GRC“, etc… Of course, it’s not easy to make your choice. My first session was “The Science Lab: Live RAT Dissection” presented by two speakers: Uri Fleyder (RSA) and Uri Rivner (Biocatch). I liked the title and the way they presented the talk.

They started about a review of the “RATs” (Remote Access Tools). Why RATs are spreading in the underground? There are lot of support tools which allow to take control of your desktop. The combination of those tools + exploit kits keeps increasing. Then they focussed on Citadel which is a Zeus clone. Zeus code was leaked and new kits emerged on the crime scene and new features added. Did you know that Citadel has also a “store” where you can buy extra modules? Do you need a new feature? Just submit a request and, if relevant, developers will do their job. It became a real business model. Some interesting modules in the store are:
- Log parser plugin ($295): It adds filtering option to the huge amount of stolen incoming data.
- Automatic iFramer of FTP accounts from logs ($1000). It steals FTP account credentials from bots and feed them info iFrames that facilitate traffic to the bonnet’s infection points.
- Citadel CRM Membership ($125)
- VNC module
This VNC module allow to take a full control of the victim’s host. That was the live infection demo! First they visited an infected website, then visited the bank website. A hidden VNC instance was started to use victim’s pc and access his bank account. Next step is how to get a challenge (generated by the owner’s security device) ? The trojan pops up a message asking to generate a code, which will be sent to the attacker and … used! The demo was nice and proven that VNC is a real threat! How to protect against this attack? Developers have to consider randomising as much as possible and encrypt the complete DOM space. Patching is also mandatory to run the latest version of the software (nothing new here). This track was flagged as “Advanced” but I expected more technical details… This demo could be a perfect example to show during a security awareness program.
Then, I attended the presentation called “No followers, no bonnet, no problem! Asymmetric DoS attacks” by Bryan Sullivan (Microsoft). DoS attacked evolved! The good old time of the geek starting an attack against a server from his basement is over. Today, DDoS attacks are performed by hacktivists and are not easy to block and track. But, this kind of attack has risks for the attackers. What about obtaining the same results (eg an unresponsive server) with only a few bytes? That’s what presented Brian. He started by explaining the algorithmic complexity. This can be applied to attacks and proven this using demos. The first one was hash collisions. If you use a weak functions (which can be legitimate if data are not very critical), you increase the risk to have collisions. The demo showed a time of 0.01″ to 7.17″ to insert hashes in a table! Most languages were affected (ASP.net, PHP, Java, Python) but it’s now fixed. The next demo was based on sort algorithms. Here again, a bad choice may have huge performance impacts! Then, Brian explained how input validation can also be a problem! (input validation being recommended by most security professionals!). Different regular expressions have different impacts on the server load. Example:
- ‘^\d+$’ vs ‘^(\d|\d\d)+$’
- ‘^.*a$’ vs ‘.*a’
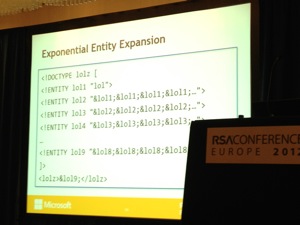
Recursive entities have the same problem: CPU usage becomes exponential! (cfr the “Billion laughs attacks“!). A great presentation!
Finally the last one for today: Â “FlipIt: a game-theory handle on password reset and other renewal defences” by Ari Juels (RSA). It’s a fact: compromized accounts may not occur, they will occur. Using FlipIt, let’s translate mathematical aspects into security. Assumptions may fail! (Murphy’s law). Most crypto is like the Maginot line: A hard work is performed to deploy good keys than we sit back and wait. What about key loss? Calling a bit-string a “secret key” does not make it automatically secret! The goal is to develop new models for scenario evolving the total loss of keys. Then came the FlipIt game (“Stealthy Takeover“). There is a contested critical secret resource like a pass, a digital signature or a computer. It’s state is binary (blue or read, good or bad). A key can be “secret” or “stolen“. “clean” vs “compromised“. Defender move: put in good state, attacker move put un bad state. there is no perfect defense: an attacker can take over a system at any time. Â Only option is to re-take control! This game may go-on forever! Â Ari explained this using mathematical formulas. Password reset can be modelled using FlipIt. Most organisation impose a default password expiration (90 days?). What can we learn? Be prepared to deal with total failed (loss of control), Â Play fast! (reboot frequently, change pw often), Arrange the game so that your “moves” cost much less than opponents. For more information about this, visit www.rsa.com/flipit.

This ends the first day. Today, almost all speakers came from sponsors, this is a bit disappointing. But I quickly checked the second day schedule, they will be interesting talks. Â Stay tuned for the second wrap-up tomorrow!