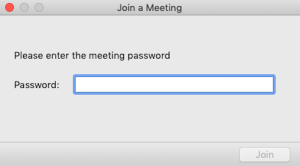
The popular web conference platform Zoom has been in the storm for a few weeks. With the COVID19 pandemic, more and more people are working from home and the demand for web conference tools has been growing. Vulnerabilities have been discovered in the Zoom client and, based on the fact