Incredible! Here is my first wrap-up for two years! Now that the COVID seems under control, it’s so good to be back at conferences and meet a lot of good friends. Like most of the events, Botconf was canceled, postponed, uncertain until the COVID situation was better and, finally, it occurs live! For this edition, we are in Nantes, France. I arrived yesterday to attend a workshop performed by CERT.pl about MWDB. I learned some interesting concepts and will probably write one or two blog articles about this tool.
The first day started with some words by Eric Freyssinet, the boss of the conference. This edition was back to normal with around 300 people registered, and coming from multiple countries. After some words about the sponsors (without them, no conference), he remembered that Botconf respects the TLP and privacy of attendees (about pictures, by example). With this edition, we are also back to the roots, the very first edition was already organized in Nantes in… 2013!
The first time slot was assigned to Berk Albayrak and Ege Balci who presented “Behind the Scenes of QBot”. The talk was given under TLP:Amber so I respect what Eric said and I won”t disclose any information they provided. They make an in-depth analysis of the QBot infrastructure. QBot (also known as Qakbot) is a well-known bot that is active for a long time. They provided a lot of useful information about the botnet internals, how it works, and some statistics about victims.
The second talk was “RTM: sink-holing the botnet” presented by Rustam Mlirkasymov and Semyon Rogachev. They started to work on this case in 2019 with the help of law enforcement agencies across multiple countries that helped to collect enough pieces of evidence to catch the attackers behind the botnet. It’s not a secret that Russia remains the top-1 provider of malware. Most banking groups in 2008-2017 spoke Russian. The RTM is spread through spear-phishing emails and has multiple stages:
- First stage: reconnaissance module (verifiy the presence of financial activity)
- Second stage (RTM Core): download of the malware from a C2 server like Pony Stealer. It has many commands like reboot, shutdown, video-process, …
- Third module (RTM Modules): many modules can be installed (like lateral movement, money stealing)
Of course, ransomware can also be deployed! The reconnaissance phase is based on the browser history (looking for the presence of interesting URLs). The most interesting part was the different ways used by the malware to connect to C2 servers: via livejournal.com blogs, via .bit domains or… based on Bitcoin transactions! The technique was explained, the IP address bytes are extracted from two transactions (2 x 2 bytes). Note that all C2 were proxy servers. When they understood how the Bitcoin transactions were used to generate the C2 IP. They create specifically crafted ones to “insert” a rogue IP address (that they managed) as a fake C2 server. This server was used to collect information (playing Man in the Middle) and redirect the traffic to official C2 servers. Brilliant technique!
The next presentation was “Private Clubs For Hackers: How Private Forums Shape The Malware Market” by David Décary-Hétu and Luca Brunoni. David is a legal guy and explained that there is a huge gap between legal people and “techies” but they have to work together to fight against criminals. The idea of this talk was to reduce this gap. They followed the criminal behavior of bad guys across different forums. These forums are used as sharing platforms. Sometimes, they are also used to perform transactions. Some of them are “public” while others are restricted (“private”) to keep out law enforcement agencies, researchers, etc. They try to create a safer and trusted environment… in theory! The initial question was: “Is there a myth of the elite or private forums?”. They compared two forums: one public with ~60K users and a private one with ~185K users and focused on malware trends. First finding, there is not a big difference in malware types (the goal remains the same: access the compromised computer and exfiltrate data). The type of access is RAT or bot but, on the private forum, more RAR were offered. About the exfiltration, the public forum offered more “stealers”. They also looked at prices, the reputation of vendors. What is the key difference? Not much:
- On the private forum, reputation and creation of good profiles is key
- On the private forum, they asked to not attack Russia
- Both provide a high sense of inpunity.
Interesting talk, not technical but it provided a good overview of the “underground” market!
After the lunch, Leon Böck presented “Insights and Experiences from Monitoring Multiple P2P Botnets“. Based on the blind men and the elephant; Leon talked about similarities with botnets: what are the targeted devices? the behavior? the affected regions? First, efforts are necessary to perform the reserve engineering of the malware and be able to understand the P2P protocol used to communicate with the C2 infrastructure. Leon explained the approach that was used in this research, based on crawlers (getting data from an external point of view) and sensors (which are part of the P2P network). The goal was to create a “BMS” or Botnet Monitoring System. After a detailed review of the infrastructure in place, Leon completed the talk with some statistics he gathered, like the presence of a diurnal pattern in many botnets.
The next talk was tagged as TLP:Green: “TA410: APT10’s distant cousin” presented by Alexandre Côté Cyr and Matthieu Faou. They mentioned that a blog post will be released by Eset soon…
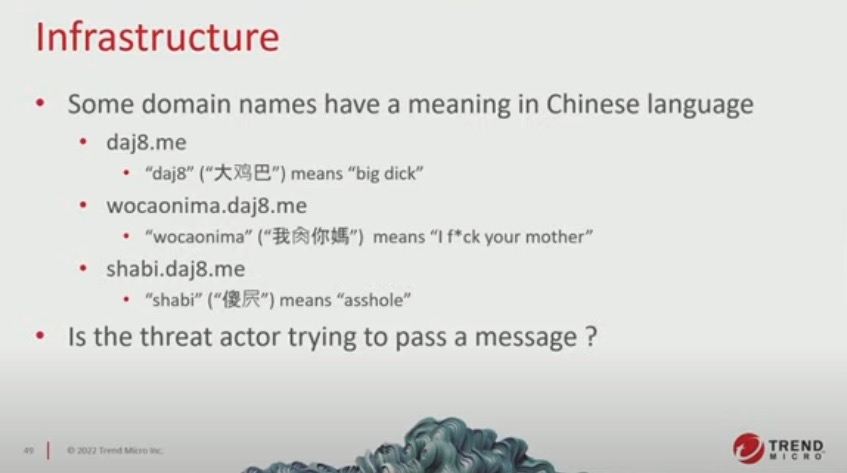
Then, “Operation GamblingPuppet: Analysis of a multivector and multiplatform campaign targeting online gambling customers” was presented by Jaromir HOREJSI and Daniel Lunghi. This research started with a sample of Xnote connected to the Operation DRBControl’s domain name. The infection vector was a fake chat application called “Mimi” (“secret” in Chinese). It targeted Windows and macOS computers. Built on ElectronJS, the malicious payload was delivered via extra code added at the end of the file electron-main.js. Another technique was a persistent XSS combined with a fake Flash installed. Yes, even if Flash is dead for a while, this technique still works. A third infection vector discovered was a fake .dmg to install BitGet (a Singapore cryptocurrency company application). Then, some payloads were reviewed (example: oRAT on macOS or AsyncRAT on Windows). Finally, the infrastructure was reviewed: 50 C2 servers, and 12 different RAT families(!). Based on “rude” strings, comments, it was clear that the actors were Chinese people:
After the afternoon coffee break, the next presentation was “Fingerprinting Bot Shops: Venues, Stealers, Sellers” by Bryan Oliver and Austin Turecek. The idea behind this research was to understand how bot shops and their ecosystems are used today. Some facts:
- Infostealers are rent, data exfiltrated and used to bot shops
- Bots are used to obtain initial access and/or monetised
- Combo “email:pass” is no longer enough for initial access brokers! Bot shops are the way to go with infostealer and their data (ex: cookies, MFA details, …)
- They covered 38 account shops, 5 bot shops over the last 3y
- Main components are bot shops, malware developers, cloud providers
- Some well-known bot shops: Genesis, Russian Market, Amigos, 2Easy
- Some cloud providers: Ross Cloud, Cash Cloud, Dark Logs Cloud, …Cloud Altery
What about monetization?
- Logs may be sold by category (and resold!)
- Logs can be used by multiple actors
- Persistent infections opens up new opportunities with status updates
- Cashing out? Cryptocurrency of course!
- Slack, Citrix, SSO, Okta access are sold and searchable (used for lateral movement)
- Some bots on Russian market are identical: rent it on one, it disappear on the second
Techniques are also constantly updated: Browsers, proxies, new emulations, new data points.
The next one was “How to Eavesdrop on Winnti in a Live Environment Using Virtual Machine Introspection (VMI)” presented by Philipp Barthel and Sebastian Eydam. The goal was to explain a typical usage of a tool called Tycho to perform malware analysis but from the hypervisor point of view. The selection malware was Winnit, a classic APT RAT that was used to attack many DAX corporations. First, they explained what is “VMI” or Virtual Machine Introspection. It’s a kind of IDS to collect and detect suspicious behavior. From the IDS world, we have HIDS (host) and NIDS (network). VMI is the best of both. It connects to the hypervisor (to the malware does not detected the presence of an agent in the sandbox). Tycho can be used to interact with the OS and collected data. By example:
calc = tycho.open_process(“calc.exe”)
calc.pause()
calc.read_linear(0,1024)
add_syscall_whitelist(syscalls.NtCreateFile)
It seems to be a very powerful tool but… for me, the presentation was too much focused on a commercial tool. Indeed, Tycho is not free but it deserves to be tested. Based on Tycho, they reviewed how Winnit encrypts data, how it communicates with its C2 server, etc.
The last presentation was “Evolution of the Sysrv mining botnet” with György Luptak and Dorka Palotay. The idea was to explain how to reverse Golang binaries using Ghidra. Why? More and more malware samples are written in Go (IoT, Linux) and Sysrv was a good example. What are the (some) issues with Go (from a reverse engineering point of view):
- Huge binaries (statically linked)
- Unusual strings handling
- No symbol names (stripped binaries)
Compared to other tools, Ghidra does not have all the capabilities by default. After a quick presentation of Sysrv (found in 2020, wormable and cryptominer), they explained how to use Ghidra to analyze Go code. Go programs are organized in packages. A package is a collection of source files in the same directory that are compiled together. They already exist tools to deobfuscate Go programs like obfuscate. But what about Ghidra? When you load Sysrc, Ghidra will find 3800+ functions! Where to start? Which one(s) is/are interesting? In the next part of the presentation, Dorka explained in detail how Go uses strings. In Go, they don’t end with a NULL character. After some examples, some Ghidra scripts were introduced to automatically extract strings (and function names) from Go programs. It was for me, the best talk of this first day! All scripts are available here.
Ready for day 2!
