Hello Readers! The first day of the hack.lu conference is already over, here is my wrap-up! The event started around 10:30, plenty of time to meet friends around a first coffee!
The conference was kicked off by Axelle Apvrille who is a security researcher focusing on mobile devices and apps. The title was “Smartphone apps: let’s talk about privacy“.

Privacy and smart phone… a strange feeling right? The idea of Axelle was to make an overview of what leaks we have on our beloved devices and how much? How to spot privacy issues? The research was based on classic popular applications . They were analyzed from a privacy and security point of view with the tool Droidlysis. It disassembles the app and searches for patterns like attempts to run an exe, if obfuscated or attempts to retrieve the phone number etc. Many apps retrieve IMEI numbers or GPS location (ex: a cooking app!?). Guess what, many of them fetches data that are not relevant for normal operations. The package size can also be an indicator. More than 500 lines of Android manifest for some apps! Axelle asked to not disclose which ones. Axel also checked what is leaked from a network point of view: MitMproxy or better Frida to hook calls to HTTP(S) requests. Firebase leaks in a medical app for diabetic users. A good tip for developers: Do not integrate dozen of 3rd party SDK’s, provide ways to disable tracking, logging, analytics.
Then, Desiree Sacher presented “Fingerpointing false positives: how to better integrate continuous improvement into security monitoring“. Desiree is working as a SOC architect and hates “false positives”.

A SOC needs to rely on accurate company data to work efficiently. Her goal: build intelligent processes and efficient workflows and detection capabilities. How to prevent false positives: from a technical point of view (ex: change the log management configuration, collection) or admin/user action: update process. She reviewed different situations that you could face within your SOC and how to address them. By example, for key business process artefacts, if you get bad IOC or wrong rule pattens, do not hesitate to challenge your provider. Also, test alert! They should be excluded from reporting. Desiree published an interesting paper to optimize your SOC.
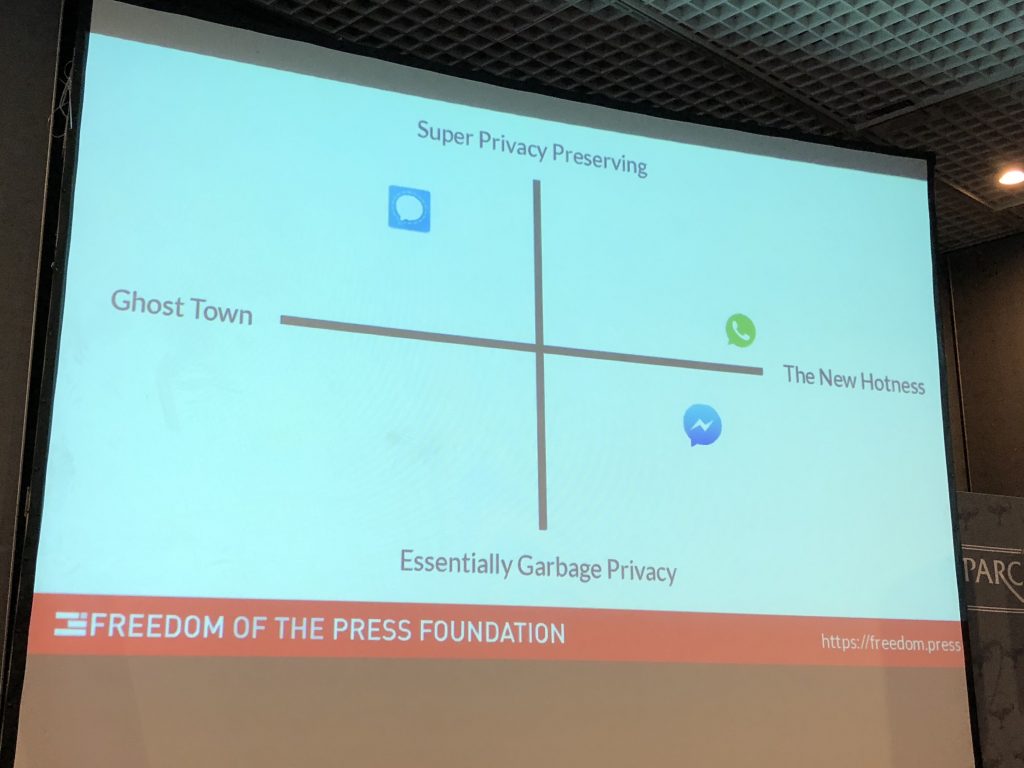
Harlo presented “Tiplines today“. She works for freedom of the press foundation. It’s a non-profit organization which does amongst other stuff software development (securedrop.org) but also advocacy: US Press Freedom Tracker and education: Digital security training. The talk covered multiple techniques and tools to safely communicate.
After the lunch break, the stage was to Chris Kubecka who presented “The road to hell is paved with bad passwords“. It was the story about an incident that she handled. It started (as in many cases) with an email compromise following by some email MITM, installation of a rootkit and some extortion. To initial compromization (the mailbox) was due to a very light password (“123456”)! 1st incident: email account breach (password = 123456). Chris reviewed all the aspects of the incident. At the end, no extorsion was paid, suspect reassigned and neutralized. Lessons learned: geopolitics, real human consequences, never trust gifts, prepare and… don’t panic!
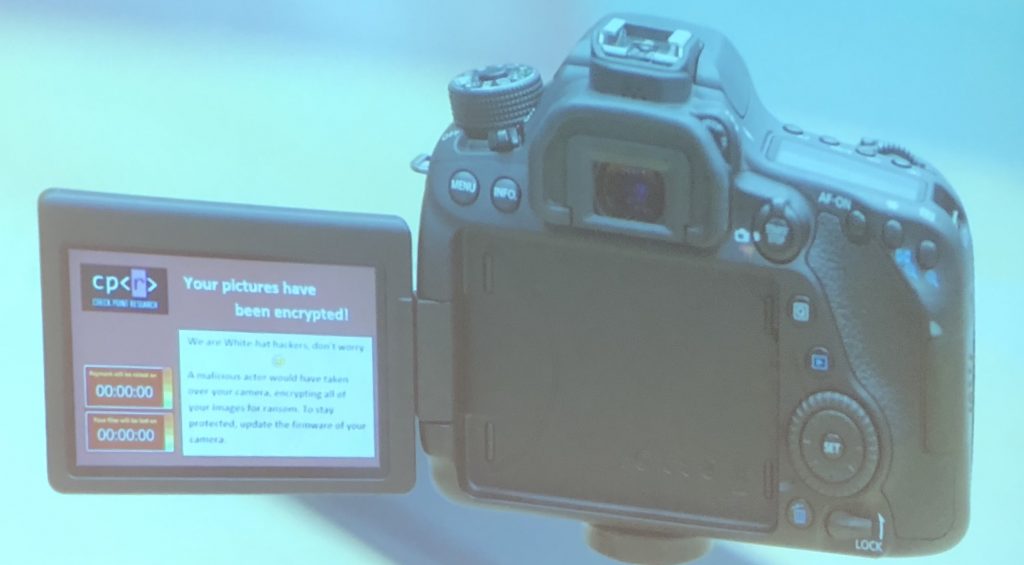
Eyal Itkin, from Checkpoint, came on stage with a talk called “Say cheese – how I ransomwared your DSLR camera?“. Like every year, Checkpoint is coming back to hack.lu with a new idea: what could be broken? 🙂 Conferences are good for this, also friends who use the targets on a daily basis. Why cameras? Photography is a common hobby with many potenial victims. People buy expensive cams and protect them (handled with care). They also contains memories from special events! birthdays, grand-ma’s picture, … with a huge emotional impacts on victims. Once you compromized the device, what to do? Brick it or setup an espionage tool? Why not ransomware? Some people reverse the firmware and added features (see magiclantern.fm). An open source project is great in this case, the documentation is key! The attack vector was PTP (Picture Transfer Protocol). Not only USB but also TCP/IP. There was already a talk about PTP that was presented at HITB in 2013 but more from a spying device aspect. The protocol has no authentication not encryption. Just ask the camera to take a picture and transfer it. First step, analyze the firmware. Grab it from the vendor website but it was AES encrypted and Google did not know the key. Can we dump the firmware from the camera? ROM Dumper! MagicLantern had the key, let’s dump and load into IDA. The OS is DryOS, proprietary to Canon, real-time OS. Let’s break PTP. Each command has a code (open, close, create, etc). Found 3 RCE and 2 were related to bluetooth. CVE-2019-5998 was the most interesting. Classic buffer overflow but not exploitable over WiFi. Restarted again… looking for more exploits. The last step was to write the ransomware, why reinvent the wheel? Use the builtin AES functions. The idea was to deliver the ransomware via a fake update. The presentation ended with a recorded demo of a camera being infected:
Eve Matringe was the next speaker with a talk titled “The regulation 2019/796 concerning restrictive measures against cyber-attacks threatening the Union of its member states” or… Europa is now NSA-Russia cyberbullet proof? This talk was not technical at all and very oriented to regulation (as the title suggested), not easy to understand when you’re not involved with such texts in a day to day basis. But for me it was a good discovery, I was not aware of its existence.
Mattias Deeg & Gerhard Klostermeier presented “New tales of wireless input devices“. Research based on Hack-RF One and CrazyRadio PA. It’s not a new topic, many talks already covered this technology. He started with a quick recapitulations of what has been said about keyboards and mouses researches (starting from 2016!). Interested but nothing brand new, guess what? Such devices provides lot of weaknesses and should definitively not be used in restricted/sensitive environments. Personally, I liked the picture with the 3 pointers bought from Logitech. Once opened, you have three different PCB’s totally different. Was there a rogue one amongst them? The question was asked to Logitech and no information was disclosed.
Solal Jacob presented “Memory forensics analysis of Cisco IOS XR 32 bits routers with Amnesic-Sherpa“. It was a short talk (20 mins) while Solal explained the technique and tools used to perform memory analysis on Cisco routers. Such devices are more and more implied to security incidents. It’s good to know that software exists to deal with them.
Finally, Ange Albertini closed the first day with his famous “Kill MD5 – Demistifying hash collisions“. See my wrap-up from Pass The Salt 2019, Ange presente the same content.
To conclude, a first good day with nice content. I appreciated to large presence of women who presented today! Good to see a better balance in security conferences! Stay tuned tomorrow for the second day!
