TheHive is an awesome tool to perform incident management. One of the software components that is linked to TheHive is Cortex defined as a “Powerful observable analysis engine“. Let’s me explain why Cortex can save you a lot of time. When you are working on an incident in TheHive, observables are linked to it. An observable is an IP address, a hash, a domain, filename, … (note: it is not an IOC, yet!). Let’s say you have an incident evolving 10 IP addresses. It could be quite time-consuming (read: “boring”) to search for each IP address in reputation databases or websites like Virustotal. Cortex is made for this purpose. It relies on small modules called “analyzers” that will query a specific service for information about your observables, parse the returned data and pass them to TheHive. There are already plenty of analyzers available today for most of the well-known online services (the complete list is available here) and, regularly, people submit new analyzers for specific online resources. Being a SANS ISC Handler, one of my favourite IP reputation database is, of course, DShield which has its own API. Surprisingly, there was no analyzer available for DShield. So, I wrote mine!
The analyzer is provided to work with IP addresses: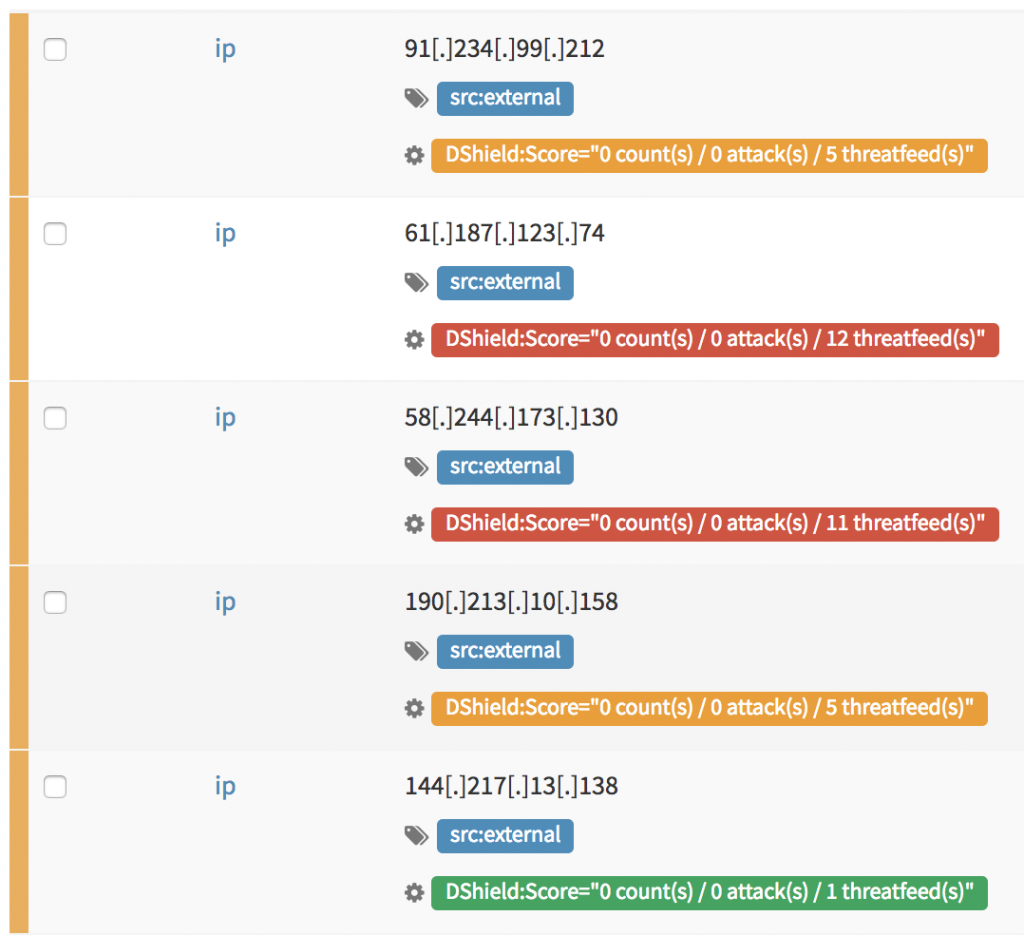
When you click on a DShield taxonomy, you get the details about this IP address: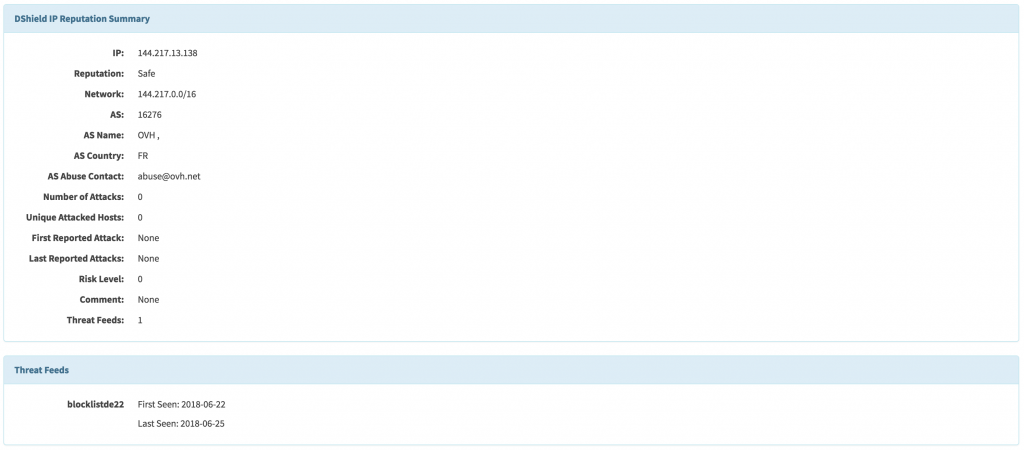
To install the analyzer, copy files from my Github repo in your $CORTEX_ANALYZERS_PATH/analyzers/ and restart your Cortex instance. The analyzer will be listed and can be enabled (no further configuration is required). Enjoy!
(Note: I’ll submit a pull-request to the official repository)

Old habits 😉 Just restarting my Docker container.
Tx for the info…
Hi Xavier,
Thanks for the blog post and the analyzer. If you are using Cortex 2, you should not need to restart your instance. Instead, as an orgadmin, once you add the analyzer with its pre-requisites, just hit the ‘Refresh analyzers’ button in the UI.