The second is over, so here is my daily wrap-up! After some welcomed coffee cups, it started sharp at 9AM with Christiaan Beek who spoke about Ransomware: “Ransomware & Beyondâ€. When I read the title, my first reaction was “What can be said in a conference like Botconf about ransomware?”. I was wrong! After a short review of the ransomware landscape, Christiaan went deeper of course. It’s a fact: The number of ransomware really exploded in 2016 with new versions or techniques to attack and/or evade detections mechanisms. Good examples are Petya which encrypts the MBR or Mamba which performs FDE (“Full Disk Encryption“). We also see today “RaaS” or “Ransomware as a Service“. Not only residential customers are targeted but also business users (do you remember the nice story of the hospital in the US which was infected?). Why remains ransomware so successful?
- It’s an organised crime with affiliate program
- Open source code available
- Buying is easy (aaS)
- Customer satisfaction
What does Christiaan means by “Customer satisfaction� On many forums, we can find thankful messages from victims towards the attackers for providing the decryption key once they paid the ransom. This could be compared to the Stockholm syndrome. We see also services like Ransomware for dummies where people are able to customise the warning messages and so customise their campaign. An important remark was that, sometimes, ransomware is used like DDoS as a lure to keep security teams attention while another attack is ongoing, below the radar.
Then, Christiaan explained how he tried to implement machine learning to help in the detection/categorisation of samples but it stopped to work when attackers started to use Powershell. The memory analysis approach remains interesting but consumes a lot of resources. They are interesting initiative to improve our daily fight against ransomware: McAfee released a tool called “Ransomware Interceptor” that gives good results. An nice initiative is the website nomoreransom.org which compiles a lot of resources (how to report an incident, how to decrypt some ransomware – tools are available).  What about the future? According to Christiaan, it’s scaring! Ransomware will target new devices like home routers or… your cars! Cars look a nice target when their CAN bus is directly available from the entertainment system! Be prepared! A very nice talk to start the day!
The second talk was about Moose! “Attacking Linux/Moose 2.0 Unraveled an EGO MARKET†by Olivier Bilodeau and Masarah Paquet-Clouston. Yes, Moose is back! This was already covered during Botconf 2015. So, its started with a quick recap: Moose infects routers and IoT devices running an embedded Linux with a BusyBox userland. Once infected, the worm tries to spread by brute forcing credentials of new potential victims. The installed payload is a proxy service used to reach social media websites. So, the question was “What are the attackers doing with this botnet? How do they monetize it?“. The next was to attack the botnet to better understand the business behind it. To achieve this, a specific honeypot environment was deployed. A real machine (based on Linux ARM) was deployed with other components like Cowrie. By default cowrie has no telnet support. So, they contributed to the project and added telnet support. The next step was to break communications with the C&C. This was also explained, it was based on mitmproxy. What about their findings?
- The botnet remains stealthy (no x86 version), no add fraud, spam or DDoS, no persistence mechanism
- It is constantly adapting
- It uses obfuscated C&C IP addresses (XORd with a static value in the binary)
- Update bot enrolment process (with more correlation checks)
- Protocols updated (real HTTP and less easy to spot)
As the botnet has no direct victimes, how is it used? Social media fraud is the key! This kind of fraud proposes you to buy “clicks” or “followers” with a few bucks. Instragram is the main targeted social network with 86% of the bot traffic. Masarah explained that this business is in fact very lucrative. But who are the buyers of those services?
Based on the people followed by Moose fake accounts, we may found:
- Business related accounts (like e-cigarette vendors)
- Business related account but represented by one individual (ex: people looking for business)
- Celebrities expecting more visibility.
So, indeed, no direct victims but some get fooled by the “false popularityâ€. What about the prices? They were analysed and they’re differences: Instagram is cheaper than LinkedIn. Who’s being Moose? They identified 7 IP addresses, 3 languages used (Dutch, English and Spanish) and, at least, 7 web interfaces. It was a nice talk with a good balance between technical and social stuff. I liked it. If you’re interested, two interesting links about Moose:
Then, John Bambenek came on stage to present “Tracking Exploit Kits”. The first question addressed by John was “Why tracking exploit kits?”. Indeed, when one is brought down, another comes alive. Law enforcement services are overloaded. Because they are one of the major way to infect computers (the other one being spam). An EK can be seen as an ecosystem. Many people work around it: operators, exploit writers, traffic generators, sellers, mules, carders, … There is only one way to protect yourself about EK’s: patch, patch and patch again. Rarely 0-day vulnerabilities are used by EK so you don’t have a good reason to not install patches. Also, the analyse of an EK may reveal very interesting stuff to better understand how they are operated. The second part of the talk covered techniques (and tools) to track EK’s. Geo-blacklisting is a common feature used by most of the EK (not only countries but also sensitive organsations are blacklisted like AV vendors or companies doing research). But VPN are not always properly detected so use a VPN! As each EK has its own set of exploits to test, you must tune your sandbox to be vulnerable to the EK you are analysing. Note that many EK pages can be identified via patterns (regex are very useful in this case). Then, John covered the landing pages and how to decode them. He also mentioned the tool ekdeco which can be very helpful during this task. If you’re interested in IOC’s, the following URLs has many ones related to exploit kits: https://github.com/John-Lin/docker-snort/blob/master/snortrules-snapshot-2972/rules/exploit-kit.rules. Again, a very nice talk for the first part of the day.
The next topic covered DDoS botnets and how to track them. Ya Liu’s presentation was called “Improve DDoS Botnet Tracking With Honeypotsâ€. In fast, Ya’s research was based on PGA or “Packet Generation Algorithm“. During his research, he found that a Botnet family can be identified by inspecting how packets are generated. It was a nice research with a huge data set: 30+ botnet families, 6000+ tracked botnets, 250K+ targets (it started in 2014). Ya’s goal is to collect packets during attacks and, based on the analysis, to map them to the right family. He explained how packets are generated and the identification is due to bad programming. Then algorithm to analyse data and extract useful info was reviewed. Interesting approach but the main issue is to find enough and good packets.
The first half-day ended with Angel Villega who presented “Function Identification and Recovery Signature Tool†or, in short, “FIRST“. The idea behind this project is to improve the daily life of malware researchers by automatic boring stuff. We don’t like boring tasks right? Here again, the goal is to analyse a sample to tag it with the right family. FIRST is an IDApro plugins which extracts interesting information from functions found in the malware samples (opcodes, architecture, syscalls, …) and send them to a server which will check the information in his database to help to identify the malware. Why does it work? Because people are lazy and don’t want to reinvent the wheel. So chances to find shared functions in multiple samples are good. As a kick-off for the project, there is a public server available (fisrt-plugin.us). It can be used as a first repository but you can also start your own server. Nice project but less interesting for me.
After the lunch break, Tom Ueltschi came on stage to present “Advanced Incident Detection and Threat Hunting using Sysmon (and Splunk)â€. Tom is a regular speaker as botconf and, this year again, he came with nice stuff that can be re-used by most of us. First, he made an introduction about detection techniques. It is very important to deploy the right tools to collect interesting data from your infrastructure. Basically, we have two types:
- NBD or network based detection
- HBD or host base detection
For Tom, the best tools are: Bro as NBD and Sysmon + Splunk as HBD. I agree on his choices. Why Sysmon? Basically, it’s free (part of the SysInternals suite) and, being developed by Microsoft, it is easy to deploy it and integration is smooth. It logs to the Windows Event Logs. Tom research started with a presentation he attended at RSA with the author of Sysmon. The setup is quite simple:
Sysmon > Windows Event Logs > Splunkforwarder > Splunk
Just one remark: take care of your Splunk license! You may quickly collect tons of events! It is recommended to filter them to just collect the ones interesting for your use cases. The second part of the presentation covered such use cases. How to start? The SANS DFIR poster is often a good starting point. Here are some examples covered by Tom:
- Tracking rogue svchost.exe: Always executed from the same path and MUST be executed with a ‘-k’ parameters. If it’s not the case, this is suspicious.
- Detection of Java Adwind RAT
- Advanced Hancitor (referring to Didier Stevens’s SANS diary)
It is also possible to perform automatic malware analysis, to detect key loggers and password stealers, lateral movements (why a workstations has flows with another one via TCP/445?). It is also interesting to keep an eye on parent / child processes relationship. And a lot of interesting tips were reviewed by Tom. For me, it was the best talk of the day! If you’re working in a blue team, have a look at his slides asap.
Sébastien Larinier & Alexandra Toussaint presented “How Does Dridex Hide Friends?â€. They presented the findings of an investigation they performed at one of their customers. He suffered of a major bank fraud (800K€!). The customer was “safe”, had 2FA activated but it was compromised and asked to find “how?”. They reviewed the classic investigation process which started with a disk image that was analysed. What they found, how, the artefacts etc. The first conclusion was that the computer was infected by Dridex. But 6 days later, another suspicious was created which dropped a RAT on the computer. Nice example of a real infection (I was surprised that the customer accepted to be taken as an example for the talk).
And the afternoon continued with “A Tete-a-Tete with RSA Bots†by Jens Frieß and Laura Guevara. Here again, the idea of the talk was to automate the analyse of encrypted communications between a bot and its C&C. When you are facing encryption every day, it may quickly become a pain. The good news for the research was that there is not a log of changes in encrypted communications across malware families. Also, bad guys are following best practices and rely on standard encryption libraries. The analyse process was reviewed to be able to decrypt communications: It is based on a fake C&C with a rogue certificate, a DNS server to spoof requests and the injection of a DLL with cryptographic functions.
After a quick coffee break, the next presentation was “Takedown client-server botnets the ISP-way†by Quảng Trần who is working for a Vietnamese ISP. Takedowns are important countermeasures in fighting botnets. Why is it so important from an ISP perspective? Because they need to protect their customers, their network and also respond to local law enforcement agencies requests. Quang explained the technique used to bring a botnet down: Once the IP & domains have been identified, the ISP can re-buy expired domains or perform domain / hosting termination. In this case, the major issue is that some ISP’s are not always reactive. But for an ISP, it can be interesting to maintain the DNS, monitor the traffic, reroute it or perform DPI. The technique used is a sinkhole server that can serve multiple botnets via their own protocols and mimic their C&C via a set of plugins. With this technique, they can fake the C&C and send termination commands to the bots to bring the botnet down in a safe way. Interesting remark during the Q&A session: such kind of operation is illegal in many countries!
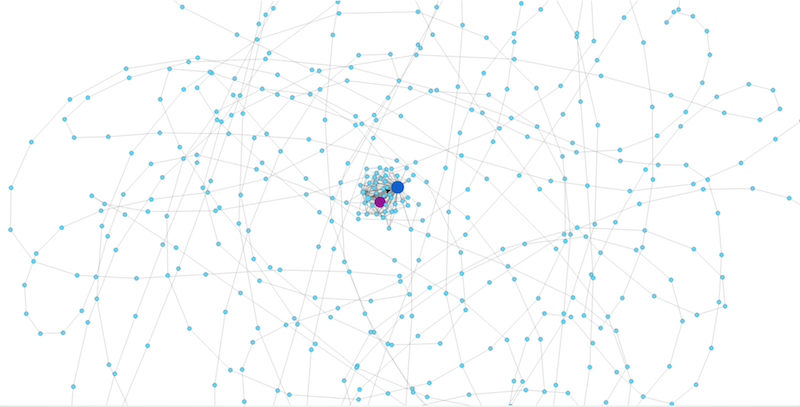
For the next talk, the topic was again “automation” and “machine learning“. Sebastian Garcia presented “Detecting the Behavioural Relationships of Malware Connectionsâ€. The idea of his research is not rely only on IOC’s (that the only real info that we have today to fight against malwares and botnets). But, it is not performant enough with new malwares. Sebastian’s ideas was to put more interests on network flows. Sometimes it can help but not always. What about checking the behaviour? He explained his project which produces indeed nice graphs:
It was not easy for me to follow this talk but the information shared looked very interesting. More information is available here.
The last talk had an attractive title: “Analysis of Free Movies and Series Websites Guided by Users Search Terms†by Martin Clauß and Luis Alberto Benthin Sanguino. The idea is to evaluate the risk to visit FMS websites. FMS means “Free Movies and Series“. They are juicy targets to deliver malicious content to the visitors (millions of people visit such websites). The idea was to collect URLs visited while browsing to such websites and check if they are malicious or not. Classic targets are Flash Players but they are many others. How to reach FMS websites? Just search via Google. Search for your favourite singer, the latest Hollywood movie. The x first results were crawled and analysed via online tools like VT, Sucury, ESet, etc. The results are quite interesting. As you can imagine, a lot of web sites redirect to malicious content. Based on 18K pages analised, 7% were malicious (and 10% of the domains). Other interesting stats were reported like the singer which returned the biggest amount of malicious page or who’s most targeted (Spanish people). Nice talk to finish the day.
Before the official reception, Â a lightning talks session was organised with 10 x 3 minutes about nice topics. That’s enough for today, seen you tomorrow with more content!