The third day is over! After the speaker dinner in a cool place and a very short night, I attended more talks today (no workshops). Let’s go for the daily quick wrap-up…
The first talk was “Internet scanning – conducting research on 0/0†presented by Mark Schloesser from Rapid7 and is also a developer of the Cuckoo sandbox. The topic focused on the IPv4 address space of course. IPv6 could be nice for another talk but has many challenges.
Mark’s topic was not only the scanning part but also wide data-gathering. Example: when the port 80 is publicly available, the website behind is crawled. People think that scanning the Internet takes time… months? In reality, there are quite performant tools today like masscan or zmap that are able to scan the complete Internet addresses space in less than one hour. Of course, this is theoretical because packets are processed by many routers which can affect the overal performances of the scan. Scanning the Internet is not a new topic and other projects exist for a while like Shodan, the shadowserver foundation, ErrataSec. Of course, Mark said that scanning the Internet is only performed for research purpose (in his case of course). He reviewed some interesting findings:
- The top 3 UPnP software contains vulnerabilities / are exploitable
- The IPMI server management protocol vulnerabilities
- Widespread misconfigurations (ex: NTP DDoS amplification)
- SNMP listing processes with arguments (and such arguments can contain passwords)
- Telnet – some devices even don’t bother about passwords… (some are honeypots of course but not all). Funny, he found license plate readers!
- Serial ports servers (for remote management)
Mark presented a Rapid7 project called “Sonar” which helps to scan the Internet for specific ports/protocols. Here are some results:
- Port 443/TCP: They found 40M open ports, 25M certificates and crawled 55GB in 4 hours
- Port 80/TCP: They found 70M open ports and downloaded 220GB in 10 hours
- Reverse DNS
- Forward DNS
- Several UDP probes (UPnP, NTP, MSSQL, SIP, …
Some recent findings?
- NAT-PMP issues / misconfiguration (>1M public IP)
- MSSQL vuln deployment (50K runs 2005.sp4 (9Y old), 25K runs 2000.xxx (>10y old)
- DNS parser, in the wild records and types (tx about TXT records)
- SIP / VoIP misconfigurations
- NTP (DDoS)
To conclude, Mark said that, in such project, the collaboration is key! It is important to make data available to the infosec community. To achive this, a website exists: scans.io. It was a great talk to start the day!
The next talk was presented by Saumil Shah. Do we have to present him? Saumil is a very cool guy who comes always with new crazy ideas and who explains them with simple words and modesty. This time, he came with a talk called “Hacking with pictures“.

Saumil has been delivering exploits for some years. When you write exploits, the first goal is work below the radar with techniques like:
- JavaScript obfuscation
- Broken file format
- OLE embedding
- JS / ActionScript
In 2011, he came with a cool attack called “255 shades of grey†and today it was a new one called “IMAJS” which consists of an image with embeded JavaScript. The concept: The same file can be used twice:
<img src=“image.gif> <script src=“image.gifâ€</script>
The evil trick is to use comments to hide the image data:
GIF89A/*xxxxxx*/=0;xxxxxx
The JPEG format is event more powerful thanks to the EXIF data! But the problem is that some caracters must be avoided.Another demo was an exploit using an heap spray attack to pop up, guess what, a calc.exe! This technique was called “Stegosploit” by Saumil and is based on the vulnerability labeleld MS14-035 by Microsoft. The next idea was to have an attack based on some kind of “time machine”. The image is downloaded by the victim at a certain time but the exploitation occurs later. This could have a huge impact in incident response! Conclusions of this talk:
- From an offensive point of view:
- Lot of possibilities
- Weird container, weird encoding or obfuscation
- Such attacks are emerging in the wild
- And not limited to browsers!
- From a defensive point of view:
- DFIR is a nightmare
- You can’t rely on extensions, file headers, MIME types or magic numbers
It was really a good presentation, my favourite of today!
After a short break, Paul Rascagnères and Eric Leblond presented “D&D of malware with exotic C&C“. This was a good team: Paul is a respected malware researcher and Eric is a core developer of Suricata, the open source IDS.

Paul described different cases that he faced while doing malware analysis. How malwares communicate with their C&C servers? Then, Eric explained how to configure Suricata properly to catch the communications (while keeping the performances acceptable).
- Case 1: simple HTTP communication.
Here the goal is to optimise the Surcata rule to get only interesting stuff (and not doing a simple grep on all flows). Problem with PCRE is performance! Rules can be optimised. - Case 2 : HTTP + Gzip communications (Ex: the RAT IcoScript)
Suricata uses SSLLibhtp handles gzip transparently. - Case 3: Named pipe comms (Ex: the Uroburis rootkit. \\machine\\piipe\\xxx)
In this case, we are facing communications between desktops or laptops. Usually, this kind of traffic is not inspected by an IDS. But, if it’s the case, Suricata is able to detect this type of traffic as demonstrated Eric. - Case 4: Communications via User-Agents (Ex: Houdini)
- Case 5: Communications via DNS requests (Ex: FrameworkPOS)
In this case, Suricata can use LUA capability to extract data. See https://github.com/inliniac/suricata/pull/1169. - Case 6: Steganography communications (Ex: Uruburos next generation)
Conclusion of this talk: even if we have nice tools like dynamic sandox analysiss systems, it’s still very useful to reverse the malware code to understand how the  communicate and write powerful rules! Funny presentation made by two crazy guys!
Then, two presentations were scheduled but I did not follow them:Â Dominique Bongard spoke about WPS or “WiFi Protected Setup”. After a good description of the WPS working principles (You know the button you have on your router or the sticker on the bottom), Dominique explained the weaknesses of this system.
The next one was not a technical talk but a review of the cyberwar between Russia and Ukraine. Glib Pakharenko explained what hapened before and during the war between the two countries. The cyber attacks started before the revolution and they are not only hacking or DDoS. It can also be:
- Massive changes in Wikipedia pages
- Flooding forums with propaganda messages
A good example was the one of Russia which hacked SmartTV’s in Ukraine and forced them to show terrorists channels!
The next talk was a presentation of mitmproxy by Maximilian Hils. This proxy plays man-in-the-middle and intercept HTTPS requests. This tools is free and basically allow you to inspect encrypted traffic between the browser and the server but not only! It can also:
- be extended with Python scripts (example: to replace some text by another one on the fly)
- act as a regular proxy, a transparent proxy or an up-stream proxy
- replay sessions (server or client)
The tools is console based and really deserve to be part of your regular toolbox!
And we continued with another talk. This one was called “How I hacked my city” by Amihai Neiderman. This was a walkthough talk. Amihai told us a story. How it begun when I discovered a strange SSID “FREE_TLV” broadcasted on the street. Curious, like many of us, he tried to connect to it and found more and more information.

He explained step by step like a novel how he successfully compromised the devices behind the wireless network. Starting from test standard passwords, SQL injections, download of the firmware (after being able to identify the vendor product) and how he successfully exploited the firmware.
The next talk focused on exploiting Virtualbox via the 3D acceleration feature. This was called “Breaking out VirtualBox through 3D acceleration” by Francisco Falcon. When I read the abstract of this talk, my first reaction was: “But, how many people use this feature with VirtualBox? Who’s running games on VirtualBox?“. Anyway, Francisco found a great way to abuse this feature! Â Note that the VirtualBox developers already warn users in the document: “This code may contain bugs“.

Before explaining how to exploit the feature, he explained how it works. VirtualBox 3D acceleration is based on Chromium, a library that allow remote rendering of graphics (but nothing related to the browser). The flow of data is the following:
host hardware -> host OS
-> VirtualBox hypervisor (chromium server)
-> Guest OS (vboxguest.sys)
-> OpenGL client
The second part of the talk was dedicated to the detailed explanation of how to exploit this architecture.
My last talk was the one of Garcia Sebastian who presented a nice way to detect botnets activities via the network traffic (“Botnets Behavioral Patterns in the Network“).
The idea behing this talk was based on the following question: How do we detect malwares? We can analyze binary files (the malware itself) or the generated traffic (to exfiltrate data, to communicate with the C&C). The files analysis can be static, dynamic but remains complex. And, it’s the same for the network traffic. What are the performed actions and how they change? An interesting statistics is how we analyse the network traffic?
- 47% use fingerprints or rules
- 34% use repuration
- 50% use anomaly detection
- Only 2 machine learning algorithms (not anomaly detection)
The next question is: Is it working?
- Fingerprint is fast (portscan)
- Fngerprint give FP but can be tuned
- Reputation is fast bur difficult to get (less tuning)
- Anomaly detection may work for very specific contexts.
What’s not working?
- Fingerprint: it’s a cat-and-mouse game (not all covered)
- Reputation is case-by-case
- Anomaly needs to build normality of each network (baseline) and adapt
- Machine learning has several weaknesses: lack of labeled datasets, lack of foot eval in real environments
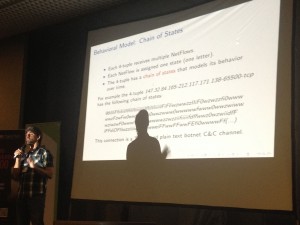
Sebastian’s idea was to focus on single connections (which is related to a specific action like: a DNS resolution, access to Google, a spam sent). He needed aggregation and created a 4-tuples based on: the source IP, the destination IP, the destination Port and the protocol. Then he explained how the model was created by analysing the behavior of each 4-tuples by extraction 3 features of each flow:
- The size
- The duration
- The periodicity
Based on the sizes of the flow, Sebastian explained how to assigned a specific caracter to it (36 states possible). Based on this model, he was able to build a botnet dectection model based on the Markov Chain. A nice research and a nice talk!
I did not attend the last talk. The day finished with the celebration of the CTF winners. The regular conference is now over. Tomorrow, no more regular talks, just a few workshops are still scheduled. Good edition of hack.lu which remains a conference with a specific atmosphere. See you next year for the 11th edition!
Note: the slides are available here.
2 comments