 When talking about security to small companies – the “SME market” as the business says – their reaction is often: “Me? Why should I care? I’m so small and my business is not relevant for cyber-criminals…“. This is a big fail! As a proof, I like to ask them for a top-10 or top-20 of their customers. There are chances that a big name will pop-up. Let’s take a practical example: A contractor is in charge of some systems maintenance on your network Usually a VPN has been established with this company and you restrict access to your servers to this VPN only. But do you really know who’s sitting behing the keyboard at the other side of the encrypted tunnel? For years, I’m in contact with customers using such services and most of them do not care of this problem. A VPN must be considered as a door into your network and properly controled in this way! (VPN are configured with an “Any to Any : Allow” rule at the central firewall)
When talking about security to small companies – the “SME market” as the business says – their reaction is often: “Me? Why should I care? I’m so small and my business is not relevant for cyber-criminals…“. This is a big fail! As a proof, I like to ask them for a top-10 or top-20 of their customers. There are chances that a big name will pop-up. Let’s take a practical example: A contractor is in charge of some systems maintenance on your network Usually a VPN has been established with this company and you restrict access to your servers to this VPN only. But do you really know who’s sitting behing the keyboard at the other side of the encrypted tunnel? For years, I’m in contact with customers using such services and most of them do not care of this problem. A VPN must be considered as a door into your network and properly controled in this way! (VPN are configured with an “Any to Any : Allow” rule at the central firewall)
But not only IT contractors are a risk. Let’s take a second example: A small local florist has won a contract with a big well-known organization. Once a week, he must deliver fresh flowers in the headquarters building. As a contractor, the florist is trusted and have a physical access to the building or access to an extranet. Once onsite, a malicious guy could connect a Pwn Plug in a corner of a meeting room (it tooks only a few seconds).
Every company manages valuable data and not only money, CC#, SSN#, patents or magic formulas. Sometimes it could be your customer base! And if you don’t implement security controls, you could be used as a “pivot“. Pivoting is a technique of using an instance (the “pivot“) to be able to move around inside an infrastructure. First step, you compromise a first system and, second step, you attack others instances which are normally inaccessible. Example: a corporate laptop is compromized while visiting a rogue website. Once the attacker gains a full control, it could perform all kind of tasks like port-scanning (reconnaissance), new attacks against critical server (the Active Directory is a new target) etc. If the definition of pivot focuses primarily to computers, it can also be applied to companies. How easy is it?
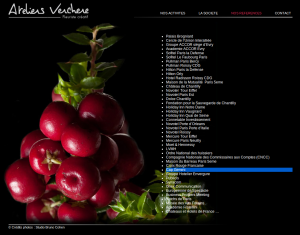
As usual, people disclose information online and Google indexes them. Let’s come back to the florist example: We choose a potential nice target: Cap Gemini, a big player in consultancy services and use this simple Google query:
intext:"cap gemini" fleuriste
We find a link to a florist in France which mentions Cap Gemini as a reference. Companies like to display their greatest customers and achievements. Can we blame them for being proud of their references?
The florist has contacts inside the organization and maybe an access badge to enter the Cap Gemini building, who knows? Do we show this only in Holliwood movies? Of course not. Do you remember, a few weeks ago, the US retailer Target was breached and millions of credit cards were stolen via PoS compomized by a malware. But such PoS are not facing the Internet, they should be connected to an internal network, how do they succeeded? After more researches, investigators found that Target was breached via a contractor responsible of the HVAC systems! They accessed the network using the contractor’s credentials! (Source here).
Conclusion: Do you know who are your contractors? How do they address their own security? Think about this story… “Don’t become a pivot!“, everybody has valuable data and could be the target of someone else!
RT @xme: [/dev/random] Pwning and Pivoting! http://t.co/Mtgi9Pi1oX
RT @xme: [/dev/random] Pwning and Pivoting! http://t.co/Mtgi9Pi1oX
RT @xme: [/dev/random] Pwning and Pivoting! http://t.co/Mtgi9Pi1oX
RT @xme: [/dev/random] Pwning and Pivoting! http://t.co/Mtgi9Pi1oX
RT @xme: [/dev/random] Pwning and Pivoting! http://t.co/Mtgi9Pi1oX