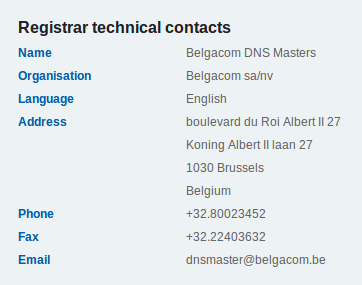
 This is not new but it still happens in 2014… Hijacking a website with just a small e-mail. Here are the facts. For a while, I’m hosting a friend’s website. His website is quite old and it already moved from servers to servers depending on my deployed infrastructure. A few weeks ago, I notified my friend that a new change should occur asap: The website will be moved (again) to another IP address. Since the last server change, the domain name also moved and is now hosted by an ISP. My friend trusted me and suggested to contact directly the ISP. In this case, the ISP was the registrar and hosting the zone on its DNS servers at the same time! I followed the procedure and contacted the registrar as mentionned on dns.be:
This is not new but it still happens in 2014… Hijacking a website with just a small e-mail. Here are the facts. For a while, I’m hosting a friend’s website. His website is quite old and it already moved from servers to servers depending on my deployed infrastructure. A few weeks ago, I notified my friend that a new change should occur asap: The website will be moved (again) to another IP address. Since the last server change, the domain name also moved and is now hosted by an ISP. My friend trusted me and suggested to contact directly the ISP. In this case, the ISP was the registrar and hosting the zone on its DNS servers at the same time! I followed the procedure and contacted the registrar as mentionned on dns.be:
I took a deep breath and sent an e-mail to <dnsmaster@belgacom.be> explaining the situation:
From: <me> To: <dnsmaster@belgacom.be> Cc: <my-friend> Subject: Change request xxx.be Dear DnsMaster, A friend of mine is hosting his website on my server (xxx.be). I would like to move the website to a new server. This change implies a new IP address for this host:  IN A x.x.x.x  IN AAAA x:x:x:x:x:x Could you please implement those changes? If extra controls are required, you can reach me on +32 xxx xx xx xx. Best Regards, Xavier
I was ready to fight and prove them that my request was legitimate but it happened otherwise. I received a nice auto-reply with some classic commercial content (read: “You are very important to us!“) and a ticket number. Step one completed! I expected to have, at least, another e-mail asking me for more details or a phone call (I gave my mobile number especially for this purpose) but… nothing! This is the timeline of events:
- 10:50 : Original mail sent (see above)
- 10:55 : Auto-reply with my ticket number
- 11:35 : Changes done, ticket closed
- 11:45 : Testing from a public DNS server (to avoid caching issues) – new IP alive!
In less than one hour, the domain name zone was updated! Scrary! In this case, it was good news for me because I was able to complete the website migration much quicker than expected. But from a security point of view, we are facing some issues:
- I’m not listed as contact or owner in the domain name administrative information
- I’m never in contact with the <dnsmaster>, they don’t know me
- The email sent was a piece of cake to write by a (novice) social-engineering guy
- No contact was taken with me to confirm the change (and even, as an attacker, I would reply: “Sure, do it!“)
Why spend time to pwn servers, play MitM attacks or poison DNS caches if only one e-mail is good enough to hijack a website?
I feel as amazed as Kristof.
It was quickly and as exactly as you asked.
That is stunning, so unlike BGC.
Always be very careful if you ask BGC to do something.
Normally you won’t know what they have done, who has done it, or when it was done.
And you will never get another response than the automatic mail.
Belgacom style ! “@xme: [/dev/random] DNS Hijacking With Just One Mail http://t.co/LrPpH23oGkâ€
I’m just impressed that you managed to get an ISP helpdesk to do anything at all. Especially that quickly. They also did exactly what you asked.
Franky, I find this to be an unlikely story!
RT @xme: [/dev/random] DNS Hijacking With Just One Mail http://t.co/X05Lx3AGZD
RT @xme: [/dev/random] DNS Hijacking With Just One Mail http://t.co/X05Lx3AGZD
A few months ago they accepted requests only if they contained a ‘valid’ from (address from the domain name). It was of course possible to forge a fake address but it was a little bit more secure. However one month later they suppress this condition.
RT @xme: [/dev/random] DNS Hijacking With Just One Mail http://t.co/X05Lx3AGZD
RT @xme: [/dev/random] DNS Hijacking With Just One Mail http://t.co/X05Lx3AGZD
RT @xme: [/dev/random] DNS Hijacking With Just One Mail http://t.co/X05Lx3AGZD
@xme .. got fax, everything was OK, no mater who sends it and from where. 🙂 #fun
@xme one local ISP some time ago approved this kind of request if only was faxed to them; tried with some fax services and as long as they..
RT @xme: [/dev/random] DNS Hijacking With Just One Mail http://t.co/X05Lx3AGZD
Another good reason to start monitoring the IP addresses associated with your public websites: https://www.corelan.be/index.php/2013/12/29/a-chain-is-only-as-strong-as-its-weakest-link-dns-hijack-monitoring/
🙂
I’ve experienced something similar with one of the biggest hosting companies in Belgium. I’ve called their helpdesk asking to adjust the records for a website. Immediately received an e-mail back, telling me i’ll have to send a mail in order to move the record. So i sent the mail. Result: record moved within 30 minutes.
RT @xme: [/dev/random] DNS Hijacking With Just One Mail http://t.co/X05Lx3AGZD
RT @xme: [/dev/random] DNS Hijacking With Just One Mail http://t.co/X05Lx3AGZD
RT @xme: [/dev/random] DNS Hijacking With Just One Mail http://t.co/X05Lx3AGZD