 We are already very close to the EOY and we are all expecting the Christmas break in a few days. Tonight, the last OWASP Belgium chapter meeting for 2013 was organised with the help of another local chapter which was created in 2013: the ISC2 one. Thanks to the F5 Belgium team who sponsored the pizzas! Two very interesting presentations tonight about browser or more precisely, how to use them otherwise. Of course, the classic intro by Seba with the local chapter and global OWASP news.
We are already very close to the EOY and we are all expecting the Christmas break in a few days. Tonight, the last OWASP Belgium chapter meeting for 2013 was organised with the help of another local chapter which was created in 2013: the ISC2 one. Thanks to the F5 Belgium team who sponsored the pizzas! Two very interesting presentations tonight about browser or more precisely, how to use them otherwise. Of course, the classic intro by Seba with the local chapter and global OWASP news.
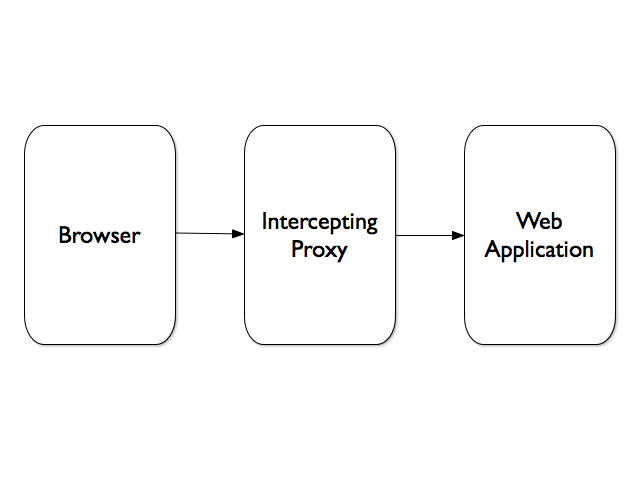
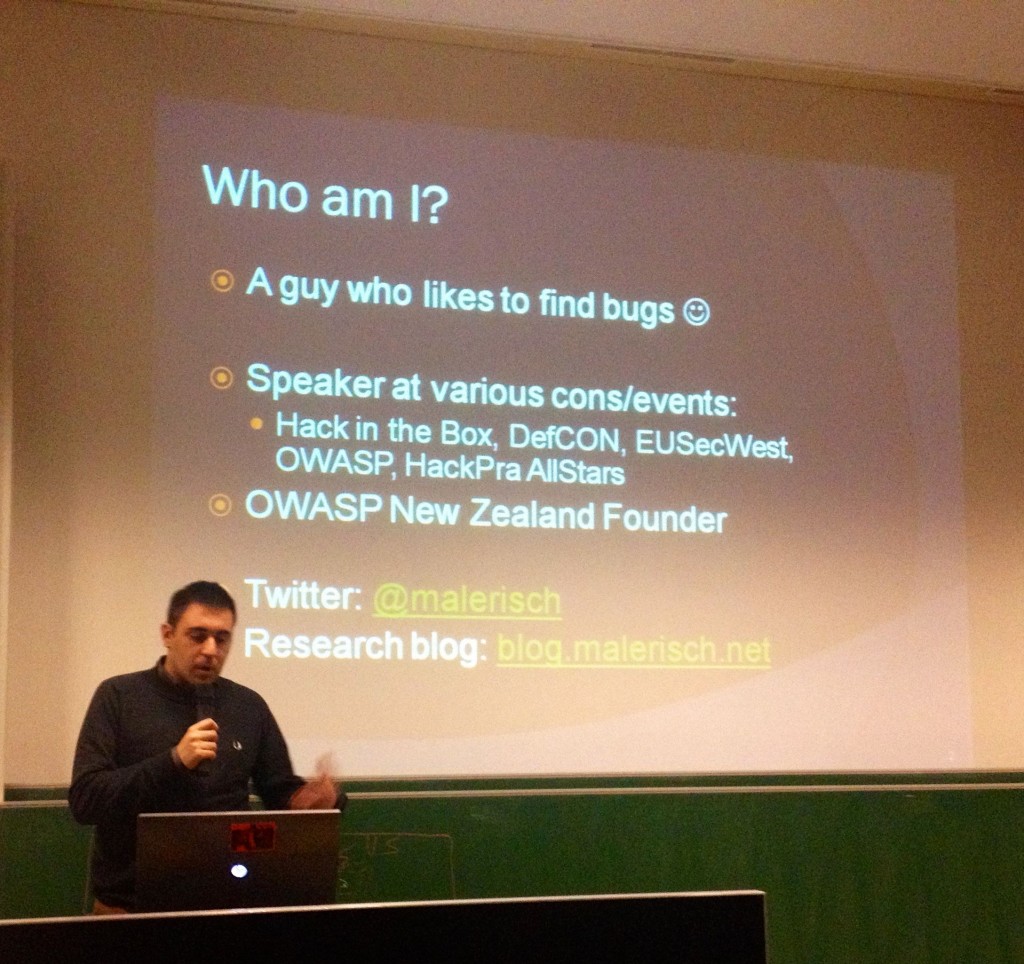
So, two speakers were scheduled today. The first one was Roberto Suggi Liverani. His talk was called “Augmented reality in your web proxyâ€. The topic was about a BurpSuite extension developed by Roberto and called “CSJâ€. He started with some facts about a classic web testing approach. We use an intercepting proxy like BurpSuite or Zap.
A classic testing flow is like this:
Roberto used BurpSuite in his examples. Its core components are:
- Intruder
- Spider
- Scanner
- Repeater
The issue with the architecture showed above is the following: Â Such proxies cannot deal with client-side technologies (like JavaScript or HTML5). The question asked Roberto was: how can we have an intercepting proxy to behave like a regular browser? The new approach demonstrated by Roberto is:
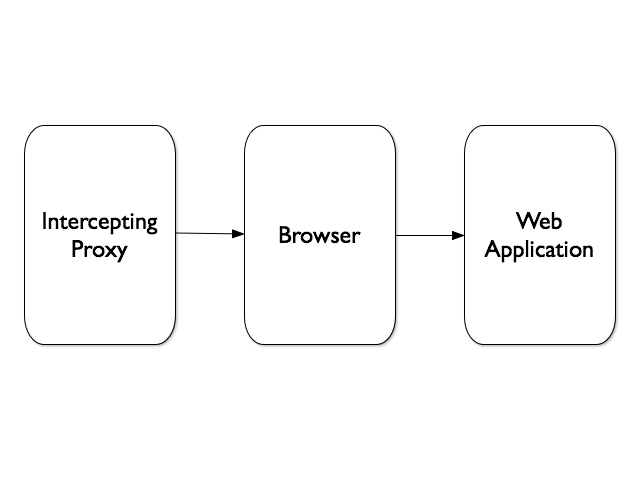 In fact, we have to be closer to the client side. How to automate this? They are different browser automation tools available  like Selenium, Crawljax or JUnit. To be able to use them with the proxy, it must of course also allow extensions. BurpSuite comes with an API, available in Java, Ruby or Python, which can interact with most of its components (see the list above). Which framework to integrate with BurpSuite? All have pros, Roberto chose Crawljax & JUnit. His extension integrates Crawljax and the JUnit test cases created by Selenium IDE.
In fact, we have to be closer to the client side. How to automate this? They are different browser automation tools available  like Selenium, Crawljax or JUnit. To be able to use them with the proxy, it must of course also allow extensions. BurpSuite comes with an API, available in Java, Ruby or Python, which can interact with most of its components (see the list above). Which framework to integrate with BurpSuite? All have pros, Roberto chose Crawljax & JUnit. His extension integrates Crawljax and the JUnit test cases created by Selenium IDE.
Then, Roberto make some demonstration. The first one was a website with authentication. A classic proxy cannot understand complex Javascript actions like onmouseover(). Crawljax is launched from the proxy and browses the website again via BurpSuite to be certain to catch all the URLS and test them using the components.
The second demo was based on phantomjs (a headless browser). It’s a very convenient way to quickly browse a complex website (no need to render objects).
Then, Roberto explained how JUnit was also integrated into BurpSuite. The next demo was based on a shopping cart. Via Selenium IDE, a test case is created to add one item into the basket. Then the test case is exported. The complete process is more complex because the exported code must be compiled into a Java class. But once the class is loaded and registered, it’s easy to automate complex testing scenarios. Roberto ended his presentation with some interesting findings made with CSJ during his research:
- Command injection via base64 encoded data
- Pages vulnerable to XSS that were clickable elements which would invoke toggle().
- A shopping cart with a special item which decreased the amount 😉 (found via JUnit)
Conclusion to the talk: combining classic and automation is a new way of testing (and to gain time). Roberto’s extension is available on here.
After a short break, the second speaker was a local player: Bart Leppens who talked about his baby: BeEF or “The Browser Exploitation Framework“. Bart is one of the developers who’s working on this project and his talk was called “If you tolerate this, your child processes will be nextâ€. In fact, Bart wrote some modules for BeEF. But what’s BeEF? It can be defined as a professional security tool which focus on client side attack vectors based on real attack scenarios. The original version was developed by Wade Alcorn.

Why develop BeEF? In fact, browsers’ 0-day vulnerabilities are very expensive. That’s why an attacker will give more focus on different targets like browser extensions or more classic attacks like XSS. The next question is: Once, the browser is owned, why not attack internal servers from the victim’s client? BeEF can be defined as a botnet for Javascript. The BeEF owner uses the BeEF control center to send commands to the zombie devices (like a regular botnet in fact). Once the browser is compromised (by download a Javascript payload),  BeEF can use multiple modules to perform attacks like info gathering, network discovery or social engineering. It can also be extended easily with your own modules. Some complex scenation can be built with RestFul API.
Once installed, BeEF proposes two URL:
- The hook URL (hook.js, to be included via XSS by example
- The UI url to control the browsers from remote
Bart demonstrated the basic features of BeEF:
- Social engineering: BeEF inject fake login pages into the browser (Facebook, Google, LastPass or …)
- Exploits (XSS, DoS, network, webcam, etc)
Then, the second part of the presentation focused on IPC (“Inter Protocol Communicationsâ€). The idea is to generate some traffic from the victim’s browser to a third-party application. To achieve this, the protocol must be very tolerant: HTTP headers are ignored and the HTTP body is used to send payload. A good example is the old fax server called ActiveFax. Bart demonstrated an attack called “XSF†or “Cross Site Faxingâ€. The goal was to send (from a compromised browser), fake faxes to an ActiveFax server. Which types of attacks could be performed?
- Sending fax to premium-rate fax numbers
- Flooding the fax server (DoS)
Sending faxes is funny but what about a reverse shell? That was the next demo! Bart demonstrated how to send a payload to the ActiveFax server and open a reverse shell to a listener (using a known vulnerability in the application). The next step was to use the BeEF Bind Shellcode instead. Why open a reverse shell to a 3rd party machine when you can enable communications between a browser and a process like cmd.exe? Awesome! The final scenario is: exploit browser using the Javascript payload, scan the network for interesting targets, pivot!
The two presentations of today were very valuable and demonstrate that, again, the browser is the “new operating systemâ€. It can be (ab)used in multiple ways for the good and the bad. A great evening!
RT @xme: [/dev/random] OWASP Belgium Chapter Meeting Wrap-Up: Using Browsers Otherwise! http://t.co/mr1J9fIPj2
RT @xme: [/dev/random] OWASP Belgium Chapter Meeting Wrap-Up: Using Browsers Otherwise! http://t.co/mr1J9fIPj2
RT @xme: [/dev/random] OWASP Belgium Chapter Meeting Wrap-Up: Using Browsers Otherwise! http://t.co/mr1J9fIPj2
[/dev/random] #OWASP Belgium Chapter Meeting Wrap-Up: Using Browsers Otherwise! http://t.co/usOCR7ZjFU via @xme #Infosec #Security