
The third day is already over! It started very (too?) early with Candid Wuest (Symantec) presented  “Dissecting Advanced Targeted Attacks – Separating myths from facts“. Not easy to speak so early and not a lot of people present in the room. For a while, the press plays a big role in broadcasting information about APTs and attacks. Hype or FUD?
If there are big stories like Duqu, Stuxnet and other well-known malwares, there is also a lot of attacks occurring back stage. Candid reported that 5.5 billions attacks were blocked last year by Symantec! On top of those attacks, come the targeted attacks (151 identified per day!). There are different motives and different ways to attack: hacktivism, money, espionage or sabotage. Note that size does not matter! Small businesses are often not well protected: “37% of targeted attacks are performed against companies with 1-250 team-members” said Candid. Those companies can be used to attack (jump to) bigger organisations because they are connected (example: a small printing company working for a big group). What about the affected sectors of activity? Top-5 are: Government, manufacturing, finance, IT services and chemistry.

In fact, targeted attacks phases looks like a pen test. The same phase are performed:
- Reconnaissance phase: Social networks are a gold mine!
- Incursion: the “real” hack. Usually a combination of social-engineering with a vulnerability. Two most common infection methods: spear phishing and watering hole attacks.
- Discovery: Where I am, what can I expect, what are the useful (read: valuable) data. The next step can be going further in the infrastructure by infecting local devices. Targeted attacks looks for precise data (ex: PDF files, files on the Desktop, in “recent” directories).
- Capture: Grabbing interesting data. This could happen over years (below the radar). Databases and file servers are common targets.
- Exfiltration: Stolen information is sent to temporary servers (rented, compromised or free hosted). There are multiple techniques: asymmetric encryption, SSH, HTTPS but HTTP remains used (less suspicious).
RSA imposes to speakers to have some slides to give tips and conclusion (“How to apply”). Personally, I liked the way Candid did it: a tag-line was added on each slide with protection tips! Most attacks could be stopped by deploying basic checks and countermeasures. Not all attacks are sophisticated but dangerous!
The second talk was the one of Jason Hart (Safenet) about hacking the virtual world. It looked a very interesting topic to me. The presentation focused not only on “virtualisation” in term is hosts and guests but also in virtualised online services (in the cloud). Jason has a good background in ethical hacking and started his presentation with a big disclaimer… Will we see interesting stuff? Security is based on confidentiality, integrity, availability, accountability & audit ability. How to achieve this in a virtual world? “Welcome to the next generation“. First, there was servers, then came the browsers and today: virtual hacking! “Gaining someone’s password is the access to the skeleton of his live” said Jason. Sensitive data is everywhere. Where are your keys? Who’s access your data? Where is your data? Those questions are critical.
- VM’s are easy to copy (read: steal). In the same way:
- VM’s are easy to move.
- They have multiple backups and snapshots.
What? vCenters are directly available on the web?
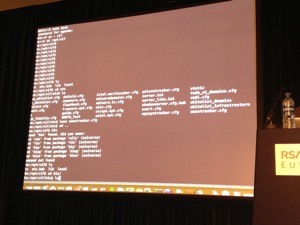
How can a hacker pwn a VMware vCenter in 60 seconds? What services are running? Update Manager, vCenter Orchestrator & Chargeback and each service has a web server… Back to the roots! Passwords are encrypted using MD5 in a file on the server. Rainbow tables are your best friend! Metasploit has also a nice module (auxiliary/scanner/wmvare/vmware_enum_sessions) to enumerate the login sessions. Virtualization has more and more vulnerabilities (2012 already 20). And by type? 41 are gain privilege access (cvedetails.com/vendor/252/Vmware.html). Pineapple demo! (btw, I found this funny but totally out-of-scope) Feel free to join the provide SSD. Cain & Abel. This proved that virtual services are not so safe. Jason reviewed some popular virtual services and their associated problems: Dropbox, Skydrive, Google Docs, etc. Amazon is a wonderful platform for virtualisation but, according to the contract, the end-user is fully responsible of its data security. The battle for the virtual world has begun. There is only one key recommendation: encryption! Consider virtual services as a DMZ!
The next talk covered the new Metasploit extension: Poortego. Mike Geide (Zscaler) presented his tool as a “Maltego for Metasploit“. Very important remark from the author: it’s only a tool! Intelligence is necessary to interpret the results. For good resultst, data must be: organised and understood to be able to act on it! First, Mike reviewed the basics of OSINT.The goal is to find information about bad stuff for the protection of good stuff (from a defensive point of view). It can be defined as using publicly available information/sources to increase your protection. Example of interesting search engine: toddington.com/resources/. How to perform OSINT?
- Data collection / aggregation
- Data correlation (extrapolate)
- Apply “meaning” to information.
Aggregation tools are SIEM, log management and CIF (“Collective Intelligence Framework“) See collectiveintel.net for details about this framework. The first demo showed how to configure and use CIF to search for interesting information (“Is there mentions about Obama in malwares or domain names used by attackers?“). Intelligence tools are a niche and commercial solutions are super expensive. It’s difficult to speak about OSINET without mention to Maltego which is some kind of standard. But it has limitations (free version has limited transforms) and it does not have the open-source flexibility. Note that data are shared with Paterva! (unless you purchase a Maltego $$$ server). Keep this in mind! Other tools: FOCA, Sploitego (released during Defcon 2012), Dradis, Netglub, EAR. And Poortego? It focus on OSINT and is flexible. It can be used for attack/defense, support multiple backend storage, support transform functionality and is easy integrated with other tools. Poortego is available stand-alone or from Metasploit. Arround Poortego, a community started to improve the project. The next demo performed by Mike:  Getting some intelligence from an attacker point of view: He wrote a transform to parse the RSA Conference website and extract information. Once exported using Grahpviz, we had a nice view of the relations between speakers, rooms, etc. A second transform was demonstrated to extract metadata from the PDFs and check the author. Mike found that some PDF were processed by an external company. Based on this information, you could perform nice targeted attacks. Think about a mail sent to this company origination from RSA: “Dear xxx, here is the last version of my RSA slides“. It’s definitively a tool to keep in mind and follow. It’s power will come from the transforms added to it.
After the lunch, two more sessions! The one I would like to attend was cancelled in last minute (Forensics in cloud environments). In backup, I attended “How to build a cyber intelligence capability” by Stewart Kenton Bertram (Verizon / iDefense). This presentation is coming from a white paper from iDefense. I just write the following fact: there is a contextual change in cyber threat. What’s the difference between a DDoS in 2000 and 2012? More people are online and the today’s attack affects much more people. Otherwise, due to the speaker words debit, it was impossible to follow the talk and take notes at the same time…
The last talk was “Hacking Senior Management” by Brian Honan or “Getting your message across“. Infosec people are often failing to pass the right message to management. Security is in the media today on a daily basis and threats are growing (coming from curiosity, personal fame to personal gain and national interests). And it continues to evolve. Today, hacktivism plays an important role in the game. Don’t forget your own users. They are careless. If threats are growing, in parallel, IT infrastructures became critical. IT Security is not a topic in board agendas. Companies cannot ignore it. In a normal situation, the management should give resources to security team to get the job done. Helas, often it’s like this:
Hacking systems is easy, hacking applications, same. Don’t think the management is stupid! They have lot of experiences, lot of trainings and are very busy. But they have their own issue. Their drivers are: money, compliance (not only in IT!) and reporting. Managers have always to report to an upfront manager. When we talk about security, we use too much technical tersm says Brian. For the management, its just “blah blah blah“. You’ve to translate your message into their language. Our problem: we come with problems and never come with… solutions! This is seen as a waste of money. About money, we also forget other costs like training, annual maintenance costs. This introduces more confusion. To hack a system, you must understand it. Same for the business. You must understand it. Open your mind and read! Try to reduce the FUD (emergency decisions are never good) and focus on benefits. Act professionally! A very good talk in the context of the RSA Conference.
The closing keynote was presented by Jimmy Donal Wales, the founder of wikipedia.org. The topic was democracy and the Internet. Wikipedia is a great project! Free access to the knowledge.
But what’s the “sum” of this knowledge? 20M of articles in 270 different languages (200 in very active projects). Top languages are English, German and French. What about China? Wikipedia is blocked for 3 years. Except some pages relation to specific content like Beijing olympic games. Pages are different based on the future/language. Example: who invented the air place? Pages in English and French will be completely different. The same applies for the type of categories visited by people. Interesting question: Who are the wikipedians (contributors to Wikipedia)? The new generation does not know encyclodepias. They use Wikipedia. Â 87% male, average 26y old. The next stop was “Freedom of speech”. During the Arab spring, communication tools were very important giving to people the ability of protest. The Internet is giving that. Another example: SOPA.What will the threat in the future? More censorship and intrusive regulation.
The 2012 edition of RSA Europe is now over! What can be conclude about this edition? Security remains a nightmare. Everybody agrees on the fact that we must perform better but nothing change. About the organisation, I found that many sessions where scored as “Advanced” but the content was below my expectations! For me, “Advanced” means going deeper and deeper to really address the problem or understand how things works. Displaying a command line interface is NOT advanced. Second point, lot of talks  were out of scope (sometimes only a part of them) but it was difficult to rely in the abstract.