 And I’m back with my wrap-up for the second day. Here are a review of the talks I followed today. Rafal Los and Shane MacDougall spoke about “offensive threat modeling on its head“. Threat modeling primer: analysis for defensive purpose. The goal is to develop countermeasures. In what offensive threat modeling differs? By attempting to understand defenders, analysis of weaknesses. It is very useful for pentests and assessments. Where are the defences weak? Physically, human point of view? Think as a bad guy and get into the defender’s head. Human behaviour, defensive imperative, modus operandi, turning modeling into a weapon: gather intelligence, modeling, plan an attack. Like this quote says: “A battle is won by the side that has better intelligence“. A good example given by Rafal was the movie “Firewall“. From an artistic point of view, not the best Harrison Ford’s movie but it reflects quite well the reality of security: why attack strong systems? Just attack people: In the movie, kids are kidnapped! Who’s prepared to this? Know the adversary: build the attack surface, profile the defenses. Gaining an advantage: attack directly, attack using information bout defenders. Another example: Attacking kids via their online game. Then, different “P” were defined:
And I’m back with my wrap-up for the second day. Here are a review of the talks I followed today. Rafal Los and Shane MacDougall spoke about “offensive threat modeling on its head“. Threat modeling primer: analysis for defensive purpose. The goal is to develop countermeasures. In what offensive threat modeling differs? By attempting to understand defenders, analysis of weaknesses. It is very useful for pentests and assessments. Where are the defences weak? Physically, human point of view? Think as a bad guy and get into the defender’s head. Human behaviour, defensive imperative, modus operandi, turning modeling into a weapon: gather intelligence, modeling, plan an attack. Like this quote says: “A battle is won by the side that has better intelligence“. A good example given by Rafal was the movie “Firewall“. From an artistic point of view, not the best Harrison Ford’s movie but it reflects quite well the reality of security: why attack strong systems? Just attack people: In the movie, kids are kidnapped! Who’s prepared to this? Know the adversary: build the attack surface, profile the defenses. Gaining an advantage: attack directly, attack using information bout defenders. Another example: Attacking kids via their online game. Then, different “P” were defined:
- First P – “Pinpoint” – create high payoff target list, secondary targets, targets of opportunity, map out defensive capabilities
- Second P – “Points of attack” – decompose target assets in point of attacks.
- Third P – “Posture” – identify asset’s defensive posture, lot or critical time-based components, does the enterprise understand security? (ex incident response)
- Fourth P – “Pwn” – execute the attack, human weaknesses are often the easiest to exploit.
- Fifth P – “Poll” – monitor and maintain compromised assets.
They are plenty of places where to grab interesting information to prepare your attack. Think about welcome boards at receptions or signing books! They are gold mines! Some social application are scarring. Think about “Foursquare” which can disclose your exact location. Negative behaviors are also interesting: gambling, alcohol, extramarital affairs! They can lead to blackmail or extortion. Human are weakest where their guard is down (in bars, clubs, smoking area). The talk was interesting.
The next talk was “All your VoIP calls are still belong to us!” by Daniel Mende and Enno Rey. First, the speakers presented the “Seven Sisters” approach and how to apply it to VoIP security. It’s based on:Â access control, isolation, restriction, encryption, entity protection, secure management andvisibility. From this approach, some questions derived like how to manage components or provide visibility? Some real examples were given. I’ve The audience was asked to not take notes about them (real customers). I’ve a comment about this: I did of course but why disclose so much information in slides? It’s must be black or white! Information is public or not. If not, let the audience sign a NDA. Based on those examples, the main message is: crypto does not solve all problems but it can be helpful in number of scenarios. If correctly implemented!
The second part of the talk was dedicated to Cisco VoIP phones and how they managed encryption of communication. It’s interesting to learn that some manufacturers use “MICs” (“Manufacturing Installed Certs“). Then a live demo demonstrated the problem: a MitM attack with ARP spoofing and a rogue TFTP Server. Once rebooted the Cisco phone established a secure connection (the small lock is always displayed to the user) but in fact it’s not. All SIP traffic was seen in clear. How to prevent us against this? Certificate validation must be done right. Good crypto is complex environment and might be difficult to implement. But, again, it does not solve all problems! Question from the audience: “What’s the Cisco point of view about this attack?” Answer: “They are working on it!“
Ben Williams continued with a presentation about “Exploiting Security Gateways via their Web Interfaces“. Ben reported 40+ exploits to vendors since oct 2011. His research was to assess the security of devices/applications which are normally deployed to protect us. They are two types of security gateway: multi-functions (like NG-firewalls) or single functions (mail/web proxies). Some are available as appliances others as softwares to install on top of an operating system. First problem: often, the management interfaces are available thru all interfaces! Some are running really old piece of code (Example: Symantec Brightmail uses a 7-years-old Tomcat instance). Ben worked properly and used the same procedure for all products:
- Find the vendor site
- Register
- Download and install
- Scan with automated tools
- Deep analyze using Burp
- Create/test exploits
- Log and report to vendors
What about the common vulnerabilities detected? Nothing brand new:
- Input validation issues
- Hijack session management
- Predictable URLs and parameters
- Excessive privilegess
- Auth bypass and disclosure
- Old software and default settings
- Easy passwords (easy to brute force)
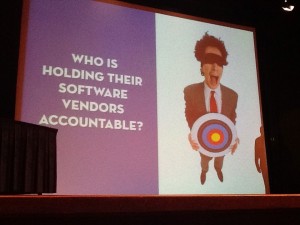
The first example given by Ben was ClearOs: The session token are easily readable with the disk utility (session IDs are in the file name!). Post exploitation was really easy. Most classic UNIX tools are installed (gcc, tcpdump, nc, nmap)). The system is not hardened at all. The second example was McAffee with another session tokens disclosure. WebSense was the third one. Ben found how to get a reverse shell just from a single URL. Then it showed how to make the proxy execute the query against itself using the address 127.0.0.2. Brilliant! Proofpoint was also a good bad example: It is possible to enumeration the email addresses managed by the system and, worse, sending Javascript to mail stored in quarantine. Once an administrator read them, the Javascript code is execute. Conclusion: exploiting such devices gives powerful position to the attacker. There is a wide range of issues (easy to hard to hard to find). Note that one of Ben’s colleagues is doing the same project against monitoring software. SSL VPNs should soon be addressed too. You can follow Ben’s research on his blog: insidetrust.blogsport.com. This was definitively my favorite talk today!
After a walking buffet, Chris Wysopal started the second part of the day with “Data Mining a Mountain of Zero Day Vulnerabilities“. Veracode analyzed lot of applications (9000+) from 100KB to 6GB, in production or prerelease, built or outsource, open-source or commercial. Then they classified the vulnerabilities and make some nice statistics. What did we learn? Lot of numbers, here are some facts:
- Most code is internally developed and Java is the preferred language.
- Top-5 of attacks: SQL injections, XSS, crypto issues, data leak and OS command injection. Web applications are much more vulnerable to those attacks.
- Top-3 of hacks: XSS, data leak, crypto
- Some attacks are NOT in the OWASP top-10: time and state, API abuse, encapsulation, race conditions, back doors and error handling
- For Java, common issues are XSS, CSRF and data leak
- For ColdFusion: XSS, SQLi, directory traversal
- For C: error handling, buffer over, buffer management error
- For Microsoft .Net.: XSS, data leak, crypto
- For PHP: XSS, directory traversal, SQLi
- Android: crypto, CRSF, info leak
- Different industries accept different vulns!
- Percentage of web applications which fail at #OWASP Top-10: 86% (!)
Interesting fact: developers of financial applicaions are doing a better job that security applications developers! This confirms Ben’s researches (see above). And what about smartphones? The retail industry is the top-1 of android applications user, then come technology. The latest interesting fact: if developers successfully passes security examinations, they still don’t apply them in their code.
IPv6 is at our doors! So it sound logical to see talks covering security about the new TCP/IP stack. Antonios Atlasis spoke about “Attacking IPv6 Implementation using Fragmentation“. Antonios focused on IP fragmentation. It’s a know problem in IPv4 but what about IPv6? And what are the consequences? Normally IP fragmentation is “normal” (the well-known MTU). If fragmented, packets are reassembled by the receiver, based on flags in the TCP header.  The problems related to IP fragmentation started in January 1988. The goal was to bypass IDS/IPS. And today, when IPv6 starts emerging? The header is limited but they exists not extension headers. Fragmentation fields moves to the “fragment header“. Note that IPv6 attempts to minimize the fragmentation by reduced the MTU to 1280 and allowing only hosts to fragment (with IPv4, routers could also fragment packets). After the theory, Antonios explained the tests he performed on different OS: Ubuntu, FreeBSD, OpenBSD and Windows 7. Using Scapy, he simulated several scenarios and checked the results. The conclusions were: Nothing news, IP fragmentation remains a valid way to perform OS fingerprinting or evade IDS/IPS solution. Interesting talk for no breaking news.
The last talk was presented by Damir Rajnovic about the different views of “Cyberspace“. What covers this name, they are multiple definitions. A first definition comes from 1984 by William Gibson in the Neuromancer novel. Why is there interest in cyberspace? Today, everything is “Cyber-*” (cyber-cafe, cyber-war, …) It’s important because we work,we live in cyberspace. Authorities try to regulate the cyberspace. That’s why a good definition is important for us! Damir made some searches on Google and found that top users of the “cyberspace” word are: .com, .co.*. Does it mean that cyberspace is a commercial term? Then he tried to locate official definitions (proposed by an international standard or a nation), to extract keywords and build an ontology. Damir found 11 definitions, mainly written by governments. Three definitions were given. Note, that nothing was found for China, India, Japan, Russia, NATO(!), OECD or United Nations. From the definitions, we can learn that the definitions are very different depending from where you look a it but common parts are:
- Virtual and physical came in same proportion
- Networks are present in many definitions
- The Internet is not the cyerspace!
Damir’s Conclusions? Cyberspace remains a new term and nobody has a good understanding of it. But governments are trying to regulate it! First, a good common definition is mandatory. I was a bit suspicious about this talk when I read the abstract but finally, it was really interesting. This is important to have clear definition of the place where we spend more and more time!
That’s all for day two! The conference has multiple talks in parallel. Therefor it’s impossible to fork() myself. I recommend to you two blogs maintained by friends who also cover the conference:
Following to the tradition, parties were organized tonight. It’s always nice put faces on names or to meet old good friends. I’ll get some sleep and stay tuned for the third day!
One comment