 The third day is just over, I just arrived at home in Belgium. Let’s write a quick review! The day started with Tom Keetch who demonstrated how to escape the protected mode of IE8. The feature is available with Internet Explorer 7 and requires at least Vista. Unfortunately, nothing is perfect in this world and Tom demonstrated how to elevate the privileges using issues in the implementation.
The third day is just over, I just arrived at home in Belgium. Let’s write a quick review! The day started with Tom Keetch who demonstrated how to escape the protected mode of IE8. The feature is available with Internet Explorer 7 and requires at least Vista. Unfortunately, nothing is perfect in this world and Tom demonstrated how to elevate the privileges using issues in the implementation.
No break and the ESIA (engineers school in France)Â came back on stage with Vincent Guyot. His talk was “Smart Cards As Stealthy Leakers“. After a review of the smartcards history (I learned that the first processor smartcards was developed in 1978!), he explained what they contain. In fact, it’s like any computer: they have a CPU, some (limited) storage and I/O capabilities (serial) and may also be target of attackers. Smartcards are usually used to provide access to something and are considered as trusted. Really? Vincent demonstrated that smartcards can also be used to store information in a fully transparent way.
Emmanuel Bouillon explored the new authentication mechanism in recent Windows versions (Seven, 2008) and how to steal users credentials. He previously given a talk about Kerberos during BlackHat 2009. After a review of the implementation issues in ActiveDirectory domains (not local accounts) and the Kerberos protocol, Emmanuel explained what changed between the old generation of Windows environment (W2003/XP) and the new one (W2008/W7). At Kerberos level, there are two common attacks: KDC (“Key Distribution Server“) spoofing and replay attack. Fortunatelay, Windows was not vulnerable to KDC spoofing (it properly handles tickets). But a new type of attack was discovered: KDC spoofing via PKINIT. This was presented during BlackHat DC 2010. The new attack is called “Pass the ticket“. It works locally as remotely. To perform a successful attack, some traffic must be sniffed. Emmanuel performed nice demos. The most important is how to protect? Here are some recommendations:
- Protect your layer-2! (in any case, it should!)
- Reduce the Kerberos ticket lifetime (default value is 10 (ten!) hours)
- Collect and manage your logs!
- Think twice before implementing a cross-domain trust relationship.
Emmanuel released some tools here. Note that this issue was discussed with Microsoft during a long period. Their conclusion was “This is a valid issue, however we do not consider this a vulnerability“.
In every conference, there is at least a talk about mobile communication. Ralf-Philipp Weinmann presented “All Your Baseband Are Belong To Us“. Smartphones uses a BTS (“Base Transmitter Station“) via 3-layers model:
- Layer 1 – Physical
- Layer 2 – LAPDm
- Layer 3 – Connection managemt / Mobility managemt / Radio resource
The baseband code used in most devices was created in the 90’s with the attitude of 90’s regarding the security. Network components are considered trusted (like for the Smartcards above). The best layer to perform attacks is the 3rd one. The initial targets for this research are iPhones (using an Infineon baseband) and HTC Dream (using a Qualcomm baseband). What are the type of bugs identified in their codes?
- Many uncheck memory copies
- Object/structure lifecycle issues (use after free, uninitialization of variables, …)
- Protocols foo-bars 🙂 Some part of the code normally used for UTMPS can be triggered using GSM frames
To exploit basedand, it can be useful to ask the help of unlock team who generally have a good knowledge. An example of attack presented was the “AT+S0=n” feature (this command enables the auto-answer feature of a modem). It’s possible to enable/disable this feature on an iPhone by using the following code respectively: *5005*AANS# or #5005*AANS#. Auto-answer can be enabled silently and being invisible. Ralf-Philipp reviewed some hardware to build your own base stations. To achieve this, open-source projects exist: OpenBSC and OpenBTS. Finally, some words were given about a potential “baseband apocalypse”. Imagine fake base stations deployed in crowed and sensitive areas like airports, financial districts, ambassies. It could be possible to brick phones, record audio, etc. The presentation is already available online here.
After the lunch, it was a festival of excellent presentations! Chris Nickerson (@indi303) talked about social engineering (“What ya lookin’ at PUNK!“). Social Engineering is a set of techniques used during pentests to collect information (cfr the “Red Team Testing” workshop of yesterday). Chris presented a talk with out any technical information, only focusing on people. He gave techniques which can be used for good or bad purpose, they remain the same. First, our communication can be compared to an iceberg: 7% is conscious (“visible”) and the remaining part – 93% – is unconscious (the hidden part of the iceberg). Chris reviewed some behaviors that everybody uses and which reveal our feelings:
- Your body’s territorial zone: intimate, personal, social, public (and how to define them)
- Palm face up / down
- Hand shacking
- Interlaced fingers
- Steepling
- Eyes
- Where you look is what you expect
- Pupil dillatation
- Blinking eyes
- The face
- Smoking styles
- Shoulders
To be able to capture the mind of people, you have to exercice! Try kids, watch everyone. For sure, be careful when talking to Chris, he knows you 😉
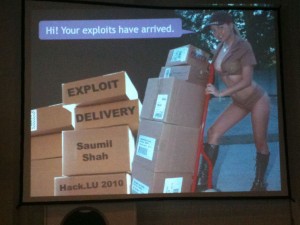
Saumil Shah (a regular speaker at hack.lu) presented “Exploit Delivery – Tricks and Techniques” and made the show. I really like Saumil’s style: presentations are clear, demos well prepared and work out of the box. He has always good comparison examples between info security and real life situations. Again, he warned us about the web and the current technologies which were not developed to work safely. And the new ones will have the same issues (Who read the W3C specs of HTML5?). The way the web evolves, more techniques help to distribute malicious code. Example: the URL shorteners and social networks. Some facts/quotes given by Saumil:
- What’s the problem with sandboxes? They remain on the computer, reading/writing files
- “calc.exe is the “hello world” of shell code”
- AV vendors are the ghostbusters of the web. They still rely on signatures – whatever the commercial name they give to their product)
- Good solution is to work with whitelists of allowed code to be executed
Saumil performed some awesome demos to own a browser. Using an URL shortener service and a VLC embedded code. Do you know that most of the URL shorteners allow any protocol? (like “smb://” or “ftp://”). Another demo was based on Javascript code embedded in a PNG file. Pixel values are extracted via “<canvas>”. Simple and powerful! Saumil’s presentation is already available on slideshare.net.
Finally, Gerard Wagener made a presentation called “AHA – Adaptive High-Interaction Honeypot Alternative“. After a brief review of what are honeypots, he explained the goal of its project. Regular honeypots are usually static systems which capture attacks. Gerard’s project was to make the honeypot reactive to attacks by creating frameworks as building blocks for adaptive honeypots. Adaptation mechanisms allow:
- Execution of a program
- Block the exec of a program
- Substitute the executed program
- Insult the attacker (to differentiate human vs machine)
How works the components interaction:
- Linux syscalls (sys.execve, sys.clone, sys.exit) patched
- Messages sent to the AHA daemon
- A decicion must be taken
- Exchange messages
The daemon reads messages generated by the User Mode, is the program execution related to an attacker, take a decisions and put in the queue. Insults are performed by replacing the requested command by /sbin/insult. Languages insults did not reflect the country code, difficult to locate attackers. A nice demo followed.
This closes the 2010 edition of hack.lu. A good year!
Thanks for the great coverage in your twitter account and the wrap-up here. great work.
Thanks for the coverage! And thanks for giving me props and featuring the cool slide photo in this article. I really enjoy Hack.LU – one of my favourite conferences. Very comfortable and close atmosphere, and I can be my natural extempore self. Thanks again for hanging out.