
Everything has been said about the “cloud”, or more precisely, “cloud computing”. Like any new technology, there are pro and con, good and bad things. BTW, the cloud is not so new. For a while, lot of organizations already used a cloud infrastructure but it remained a “private cloud”. Since it moved to the Internet, the biggest issue is now: “Where are located my data?”.
Today, I won’t restart the debate about the cloud computing, no. Let’s be positive and see how the cloud can help us in our daily life of system admin / network admin / security analyst / consultant / etc (choose your best title). A few days ago, I blogged about another cloud service called pcapr.net. This online tool allows you analyze the traffic via pcap files and report statistics like the services running on an IP address, which IP address talked to another one, etc.
Much simpler, Cloudshark is a cool service also running in the cloud as I would like to see more and more. Basically it’s a web-based version of the well known packet capture analyzer Wireshark. Let’s imagine: you are working in a very restricted environment (you can’t install third party applications on your computer) and you need to analyze a pcap file generated by a firewall or any other type of appliance (often, they have an “expert” mode which allows to capture traffic on the fly).
How does it work? Your packet capture (in pcap format) can be sent into the cloud via three methods:
- Via an upload form
- Via an URL
- Via e-mail to cap@cloudshark.org
Once done, a unique decoding session will be assigned to you and available via your browser. The developers did a great job and the similarity with Wireshark is excellent! You won’t be lost if you’re already a Wireshark user:
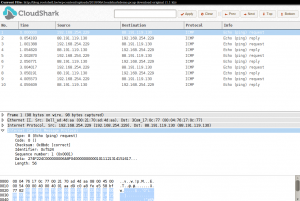
Check with this example.
Of course, do I have to warn you about the privacy of the pcap files you submitted to CloudShark? They don’t give absolutely no warranty. Don’t upload sensitive data! It’s a very nice to tool to avoid the installation of a local packet capture tool but the limitation of 512KB per file is, in my humble opinion, a little bit too restrictive (even more if you capture the payload of packets).
Excellent…Merci