| 2005/04/15 | Page created |
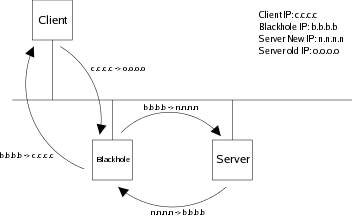
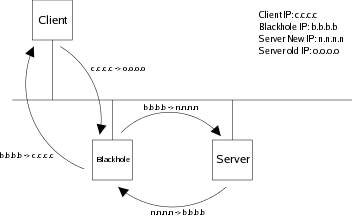
One of the requirements is to keep the server config "clean": no extra IP address to configure, nor firewall or routing table. This means that it works with any OS, any platform.
blachhole# echo '1' > /proc/sys/net/ipv4/ip_forwardOnce the server moved to the new IP range, configure its old IP on the blackhole:
blackhole# ifconfig eth0:0 10.50.10.250 netmask 255.255.255.0 upDefine the iptables rules. The first one will rewrite all incoming packets, the second one will rewrite all outgoing packets.
blackhole# iptables -t nat -A PREROUTING -i eth0 -d 10.50.10.250/32 -j DNAT --to 10.50.200.250 blackhole# iptables -t nat -A POSTROUTING -o eth0 -d 10.50.200.250/32 -j SNAT --to-source 10.50.10.240If you have a firewall enabled, don't forget to allow all incoming traffic to the old server address!
blackhole# iptables -t filter -A INPUT -i eth0 -d 10.50.10.250 -j ACCEPTImportant notes:
blackhole# tcpdump -i eth0 host 10.50.10.250 or host 10.50.200.250You should see something like this: (the client is 10.50.10.242)
09:22:33.629272 arp who-has 10.50.10.250 tell 10.50.10.242 09:22:33.629537 arp reply 10.50.10.250 is-at 00:30:f1:02:89:af 09:22:33.629313 IP 10.50.10.242.36299 > 10.50.10.250.ssh: S 2775584351:2775584351(0) win 584009:22:33.629577 arp who-has 10.50.200.250 tell 10.50.10.240 09:22:33.630526 arp reply 10.50.200.250 is-at 00:50:8b:6a:6b:fc 09:22:33.630541 IP 10.50.10.240.36299 > 10.50.200.250.ssh: S 2775584351:2775584351(0) win 5840 09:22:33.630790 IP 10.50.200.250.ssh > 10.50.10.240.36299: S 3980706886:3980706886(0) ack 2775584352 win 5792 09:22:33.630852 IP 10.50.10.250.ssh > 10.50.10.242.36299: S 3980706886:3980706886(0) ack 2775584352 win 5792